Published by BladeIntel | Threat Intelligence
Attackers have always been opportunistic. They do not need to be the smartest person in the room. They just need to move faster than you patch. AI changed the math on that in a significant way, and the data backs up what security teams have been feeling for the past two years: the window between vulnerability disclosure and active exploitation is collapsing, and most businesses have not adjusted their response posture to match.
The uncomfortable truth is that most organizations were already losing this race before AI entered the picture. AI just made the gap impossible to ignore.
The Volume Problem Was Already Unmanageable
In 2024, vulnerability databases published over 40,000 CVEs, a 38% increase from the prior year. That works out to nearly 110 new vulnerabilities per day, every day, all year, and the seventh consecutive year of record-high disclosures. Projections for 2025 point toward 45,000 to 50,000 total CVEs.
No security team, regardless of size or budget, can meaningfully evaluate 110 new vulnerabilities per day. The result is that most organizations rely on automated scanning tools to flag what matters, and then those findings land in a queue that rarely gets cleared.
This is not a tooling failure. The scanners work. The reports are accurate. The problem is what happens after the scan finishes.

Most Companies Never Actually Remediate
Here is a pattern that we see consistently across client environments: a business invests in vulnerability scanning, runs it on a regular cadence, and reviews the reports. The findings list has the same vulnerabilities on it month after month. Maybe the team triages them and logs tickets. Maybe the patches require downtime that never gets scheduled. Maybe the vendor’s patch broke something in testing and the fix got deprioritized.
The scan keeps running. The report keeps coming back. The vulnerability stays open.
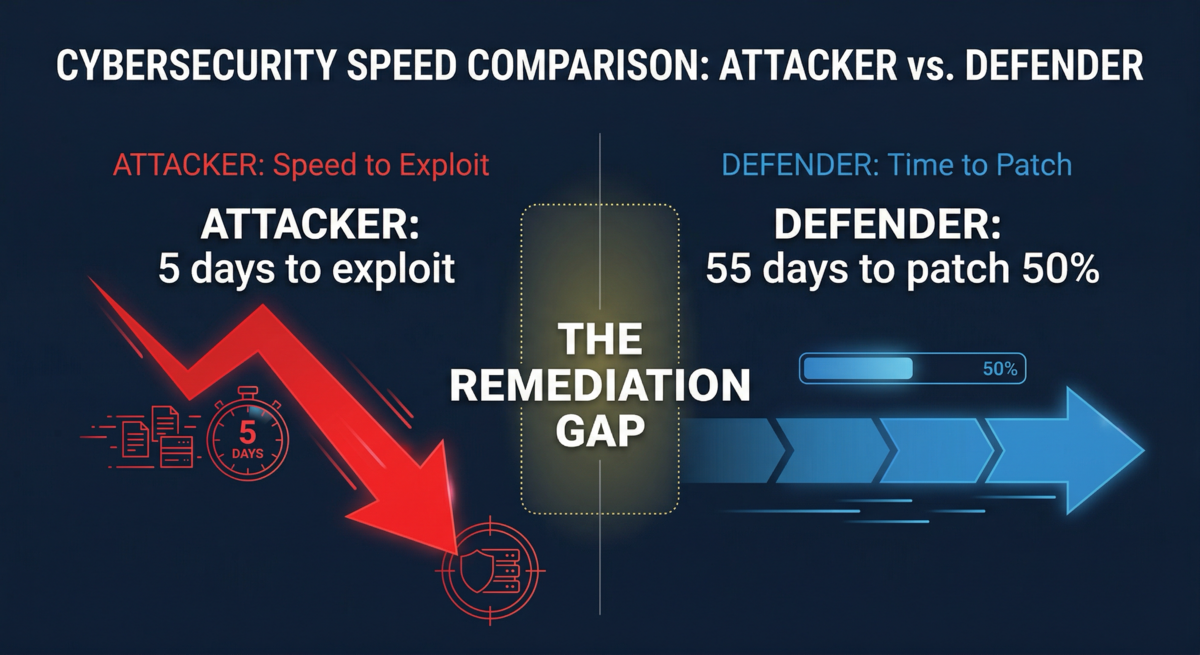
This is the norm, not the exception. Defenders currently need an average of 55 days to patch just 50% of critical vulnerabilities (Hadrian). That means half of the most dangerous findings are still sitting open nearly two months after a fix is available. For medium and low severity findings, the remediation timeline stretches into months or simply never happens.
The backlog grows. The scan reports get longer. The signal-to-noise ratio gets worse with every cycle. And eventually, the scan report itself becomes noise: a document the team acknowledges but no longer acts on with urgency, because there is simply too much on it to process.
The Noise Problem: Already Drowning Before AI
Even before AI accelerated the attacker side of the equation, most organizations were already struggling to distinguish real threats from background noise.
Vulnerability scanners produce findings. SIEMs produce alerts. EDR tools produce detections. Email gateways flag suspicious messages. Firewalls log connection attempts. Every one of these tools generates signal, and every one of them generates noise alongside it. The challenge has never been producing security data. The challenge is acting on the right data fast enough.
For small and mid-sized businesses, the math is brutal. A typical SMB security environment might generate hundreds or thousands of alerts per week across its tooling stack. Without dedicated security operations staff, those alerts sit in dashboards that nobody checks until something breaks. The findings accumulate. The logs roll. The actual threats hide in the same queue as the false positives, the informational findings, and the stale vulnerabilities that have been there for six scan cycles.
This is the environment AI-accelerated attacks are landing in: organizations that were already overwhelmed by the volume of their own security telemetry.
AI Is Making Everything Faster, and There Is More of Everything
AI did not create the remediation gap or the noise problem. It is accelerating both.
On the attacker side, AI collapsed the skill barrier for exploitation. A threat actor with modest technical skills can now use large language models to analyze newly disclosed CVEs, generate working proof-of-concept code, and craft phishing lures tailored to a specific product or vendor. Research from the University of Illinois demonstrated that GPT-4 could exploit 13 of 15 one-day vulnerabilities (87% success rate) simply by reading CVE descriptions (UIUC, 2024). What previously required hours of manual research now takes minutes.
The downstream effect is volume. When more actors can launch more attacks against more targets with less effort, the overall threat surface for every business increases. Ransomware groups listed 8,159 victims in 2025, up 33% from the prior year (ransomware.live). Vulnerability exploitation has been the leading initial access method for five consecutive years, consistently outpacing phishing (Mandiant M-Trends 2025).
On the disclosure side, AI-powered tools are helping researchers and bug bounty hunters find vulnerabilities faster than manual review ever allowed. The result is more CVEs, disclosed faster, creating more pressure on already-strained patching programs. At the same time, AI-generated noise is flooding the intake process: the curl open-source project shut down its bug bounty program in January 2026 after its maintainer reported that the vast majority of submissions were AI-generated reports describing vulnerabilities that did not exist (Daniel Stenberg, curl project). In six years of running the program, not a single AI-generated submission discovered a genuine vulnerability.
On the exploitation timeline, the window between disclosure and active exploitation has collapsed. The average time-to-exploit dropped from 32 days in 2021-2022 to just 5 days in 2023 (Mandiant). By 2024, Mandiant found the average was effectively negative one day, meaning attackers were exploiting vulnerabilities before patches were publicly available (Mandiant M-Trends 2025). In Q1 2025, roughly 28% of exploits were observed within one day of CVE disclosure (VulnCheck).
The net effect: more vulnerabilities discovered, more attacks launched against them, faster exploitation timelines, and all of it landing on organizations that were already failing to clear their remediation queues.

The Scan Report Is Not the Problem. The Queue Is.
If a business has a remediation backlog from previous scan cycles, that backlog does not sit quietly. Every new disclosure added to an uncleared queue represents another attack path that grows more accessible as exploit tooling matures and gets incorporated into commodity frameworks.
The real risk is not the vulnerability that showed up on this month’s scan. It is the one that showed up six months ago, got logged as a ticket, and never got patched because the team was already underwater. That is the vulnerability an attacker finds with a Shodan query and exploits with an AI-generated proof of concept in an afternoon.
Organizations that run scans but lack a disciplined, SLA-driven remediation program are producing security data without acting on it. The scan gives you visibility. It does not give you security. The gap between those two things is where breaches happen.
What Closing the Gap Actually Requires
The standard for adequate patching has moved. What worked three years ago does not work in a world where exploitation windows are measured in hours.
Continuous or near-continuous scanning. Monthly scanning is not sufficient when critical vulnerabilities are being exploited within hours of disclosure. Organizations need scanning cadences that match the pace of disclosure, with alerting that flags critical findings immediately.
Defined SLAs by severity. A written policy specifying remediation timelines based on severity and exploitability is not optional. Without it, everything becomes “we will get to it,” and the queue grows. Critical vulnerabilities should carry patch SLAs measured in days, not weeks.
Remediation tracking, not just scanning. Scanning tells you what is open. Remediation tracking tells you whether the gap is closing or growing. A vulnerability appearing in three consecutive scan cycles is not just a technical finding. It is a process failure that carries real business risk.
Noise reduction through prioritization. With nearly 110 new vulnerabilities published per day, not everything can be patched immediately. Organizations need to distinguish between theoretically vulnerable and actively exploited, and focus patching effort on the vulnerabilities attackers are actually using, not just the ones with the highest CVSS scores.
The Bottom Line
The problem is not that organizations lack security tools. Most businesses have scanners, firewalls, endpoint protection, and alerting in place. The problem is that the volume of findings, alerts, and disclosures already exceeded most teams’ capacity to act, and AI is compounding that overload on every side: more vulnerabilities discovered, more attacks launched, faster exploitation timelines, and more noise obscuring the signal.
A scan report that never gets remediated is not a security program. It is documentation of accepted risk. In a threat environment where attackers are operating at machine speed, that risk compounds faster than most organizations realize.
The question is not whether you have visibility into your vulnerabilities. It is whether you are closing them faster than attackers are using them. In 2025, that race got significantly harder to win.
If your scan reports keep growing but your remediation rate has not changed, the gap is already there. BladeIntel publishes threat intelligence and security research to help businesses understand the risks they face. For more analysis like this, follow us at bladeintel.com or subscribe to our threat briefings.
Sources: Mandiant M-Trends 2025, Hadrian 2026 Offensive Security Benchmark Report, VulnCheck Q1 2025 Exploitation Trends, University of Illinois Urbana-Champaign (2024), ransomware.live, Daniel Stenberg / curl project
Tags: vulnerability management, patch management, AI security, CVE, threat intelligence, SMB security, pentesting, remediation
