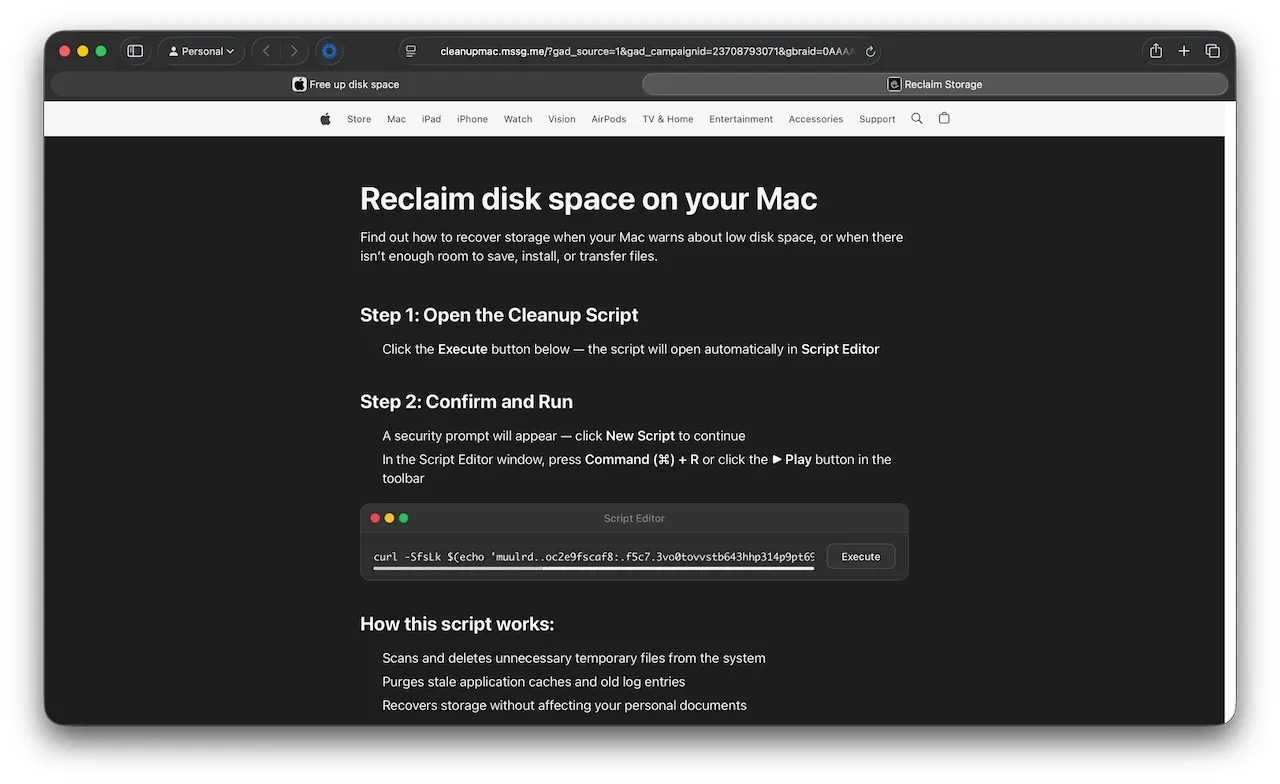
Security researchers at Jamf have uncovered a new ClickFix-style attack targeting Mac users via a fake Apple-themed webpage offering instructions on how to “reclaim disk space on your Mac”.
The malicious page (Source: Jamf)
ClickFix for everybody
ClickFix is a social engineering technique that cons victims into running malicious commands on their own machine, usually by pretending the commands are needed to fix a problem or perform routine upkeep.
This technique was initially aimed at Windows users, but in time, macOS and Linux users also started getting targeted.
“The go-to approach for ClickFix [macOS] techniques has long been convincing users to copy and paste malicious commands into Terminal under the guise of troubleshooting or routine system maintenance. Apple took direct aim at this in macOS 26.4, introducing a security feature that scans commands pasted into Terminal before they’re executed,” Jamf researchers noted.
For that reason, attackers have switched to using a browser-triggered workflow to launch Script Editor, a code editor for the AppleScript and Javascript for Automation scripting languages. (Both Terminal and Script Editor are installed by default on macOS.)
The lure and the end result
From the victims’ point of view, the attack looks like this:
- They visit the malicious page and follow the instructions
- They click the provided “Execute” button
- The page shows a prompt asking them to allow the website to open Script Editor
- The Script Editor is opened and is pre-populated with the attackers’ script
- Depending on the macOS version they use, they may or may not see an additional warning against running the script
- If they ignore the warning and allow the script to be saved on the disk and executed, the script will covertly download an Atomic Stealer (aka AMOS) variant and execute it.
Atomic Stealer is a subscription product, sold to criminals who then deploy it however they like. It’s capable of collecting system information, stealing data stored in Keychain (Apple’s built-in password management system), autofill data, passwords, cookies, and credit card information from browsers, cryptocurrency wallets, and more.
Jamf researchers have shared indicators of compromise related to this malware delivery campaign.

Subscribe to our breaking news e-mail alert to never miss out on the latest breaches, vulnerabilities and cybersecurity threats. Subscribe here!