Published On : 2026-04-24

Ransomware of the week
CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple industries, geography, and technology that could be relevant to your organization.
Type: Ransomware
Target Technologies: Windows
Introduction
CYFIRMA Research and Advisory Team has found Elite Enterprise ransomware while monitoring various underground forums as part of our Threat Discovery Process.
Elite Enterprise ransomware
Elite Enterprise ransomware is a high-impact ransomware that encrypts data on compromised systems while leaving filenames unchanged, making detection less apparent despite the complete inaccessibility of files. It employs a hybrid encryption model combining AES-256 for file encryption and RSA-4096 for key protection. Following execution, the malware generates two ransom notes, “elite_ransom.html” and “!!!ELITE_ENTERPRISE_RANSOMWARE!!!.txt” to signal compromise. The threat is associated with additional system-level actions described in its notes, including deletion of Volume Shadow Copies, potential modification of MBR/VBR boot sectors, intermittent file corruption, and disruption of system and network components.
Screenshot: File encrypted by the ransomware (Source: Surface Web)
The HTML ransom note (“elite_ransom.html”) provides a summarized overview of the attack, stating that infrastructure has been compromised, a portion of devices has been destroyed, and backup systems have been eliminated. It displays a countdown timer of 168 hours (7 days) and specifies a ransom demand of 227 BTC to be transferred to a provided wallet address. Notably, the message explicitly states that no contact or negotiation is possible and claims that decryption will occur automatically upon payment.
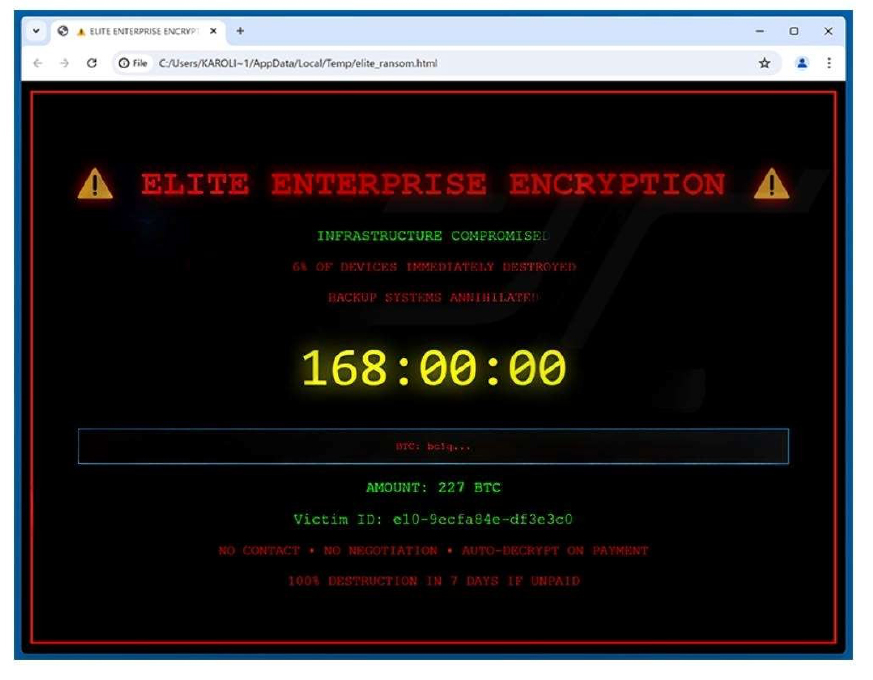
The appearance of the Elite Enterprise ransom note (“elite_ransom.html”) (Source: Surface Web)
The text-based ransom note (“!!!ELITE_ENTERPRISE_RANSOMWARE!!!.txt”) expands on the technical scope of the incident. It reports a completed multi-day propagation phase and outlines impacts such as disabled management tools, deleted cloud resources, and affected network infrastructure. The note reiterates the encryption methods used (AES- 256 and RSA-4096), along with additional actions like boot sector involvement and shadow copy deletion. Both ransom messages conclude with a fixed deadline of seven days and warnings of complete data and system destruction if the payment is not made within the specified timeframe.
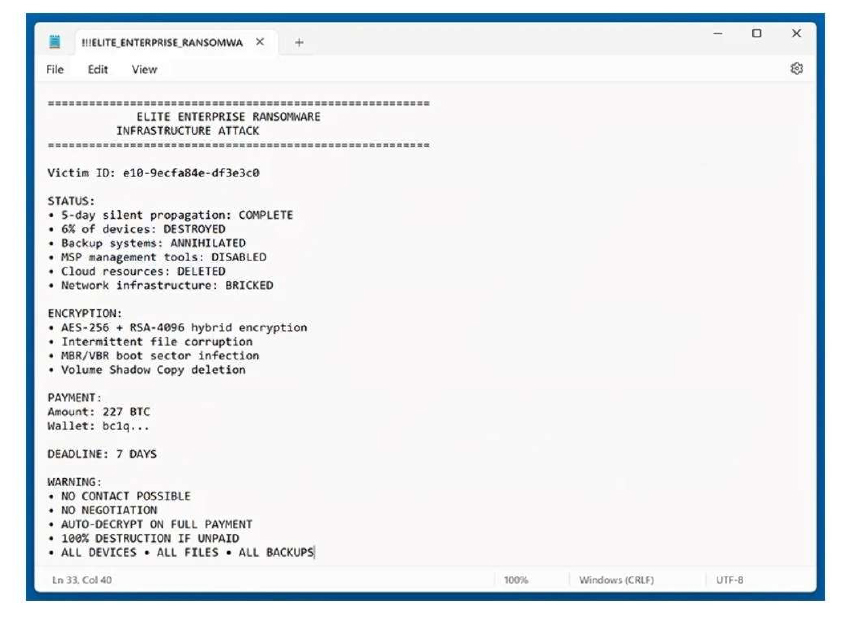
The appearance of the Elite Enterprise ransom note (“!!!ELITE_ENTERPRISE_RANSOMWARE!!!.txt”) (Source: Surface Web)
The following are the TTPs based on the MITRE Attack Framework
| Tactic | TechniqueID | TechniqueName |
| Execution | T1047 | Windows Management Instrumentation |
| Execution | T1053.002 | Scheduled Task/Job: At |
| Execution | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1106 | Native API |
| Execution | T1569.002 | System Services: Service Execution |
| Persistence | T1053.002 | Scheduled Task/Job: At |
| Persistence | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Persistence | T1112 | Modify Registry |
| Persistence | T1542.003 | Pre-OS Boot: Bootkit |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| PrivilegeEscalation | T1053.002 | Scheduled Task/Job: At |
| PrivilegeEscalation | T1053.005 | Scheduled Task/Job: Scheduled Task |
| PrivilegeEscalation | T1055 | Process Injection |
| PrivilegeEscalation | T1543.003 | Create or Modify System Process: Windows Service |
| PrivilegeEscalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| DefenseEvasion | T1014 | Rootkit |
| DefenseEvasion | T1027.002 | Obfuscated Files or Information: Software Packing |
| DefenseEvasion | T1027.005 | Obfuscated Files or Information: Indicator Removal from Tools |
| DefenseEvasion | T1036 | Masquerading |
| DefenseEvasion | T1055 | Process Injection |
| DefenseEvasion | T1070.001 | Indicator Removal: Clear Windows Event Logs |
| DefenseEvasion | T1070.004 | Indicator Removal: File Deletion |
| DefenseEvasion | T1112 | Modify Registry |
| DefenseEvasion | T1202 | Indirect Command Execution |
| DefenseEvasion | T1222 | File and Directory Permissions Modification |
| DefenseEvasion | T1497.001 | Virtualization/Sandbox Evasion: System Checks |
| DefenseEvasion | T1542.003 | Pre-OS Boot: Bootkit |
| DefenseEvasion | T1562.001 | Impair Defenses: Disable or Modify Tools |
| DefenseEvasion | T1564.003 | Hide Artifacts: Hidden Window |
| CredentialAccess | T1003 | OS Credential Dumping |
| Discovery | T1007 | System Service Discovery |
| Discovery | T1012 | Query Registry |
| Discovery | T1016.001 | System Network Configuration Discovery: Internet Connection Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1497.001 | Virtualization/Sandbox Evasion: System Checks |
| Discovery | T1518 | Software Discovery |
| Discovery | T1613 | Container and Resource Discovery |
| Collection | T1213 | Data from Information Repositories |
| Command and Control | T1071 | Application Layer Protocol |
| Impact | T1485 | Data Destruction |
| Impact | T1490 | Inhibit System Recovery |
Relevancy and Insights:
- The ransomware primarily affects the Windows operating system, which is commonly utilized in enterprise environments across multiple industries.
- The ransomware terminates processes such as vssadmin.exe Delete Shadows /all /quiet and wmic shadowcopy delete /nointeractive to delete Volume Shadow Copies, which are used by Windows for backup and restore. By deleting shadow copies, the malware prevents victims from restoring their data using built-in recovery features such as system restore points or local backup mechanisms.
- Persistence: The ransomware exhibits continuity mechanisms to ensure its survival and ongoing vicious conditioning within the compromised terrain. This could involve creating autostart entries or modifying system settings to maintain a base and grease unborn attacks.
ETLM Assessment:
CYFIRMA’s analysis indicates that Elite Enterprise ransomware is currently a highly disruptive ransomware engineered to target enterprise environments by encrypting data while deliberately leaving file names unchanged, thereby masking visible indicators of compromise despite rendering files fully inaccessible. It utilizes a hybrid cryptographic model combining AES-256 for data encryption and RSA-4096 for key protection, alongside reported system-level interference mechanisms such as deletion of Volume Shadow Copies, potential MBR/VBR boot sector modification, and disruption of management tools and network components. The deployment of multiple structured ransom notes further supports its operational design by clearly signaling compromise, enforcing strict payment conditions, and applying time- bound pressure, indicating a coordinated approach that blends technical execution with controlled communication.
Based on observed patterns in contemporary ransomware evolution, threats of this nature are increasingly shifting toward more integrated and large-scale attack frameworks that extend beyond isolated file encryption. This progression is characterized by enhanced stealth capabilities, prolonged undetected propagation within networks, and deeper interaction with critical system components and enterprise infrastructure. Future developments are likely to emphasize automation in lateral movement, tighter synchronization between encryption routines and system disruption techniques, and expanded targeting of backup mechanisms, cloud resources, and administrative controls. Such advancements would enable broader operational impact, allowing attackers to affect not only data accessibility but also system functionality, recovery processes, and overall organizational resilience in a more comprehensive and coordinated manner.
Sigma rule:
title: Disable Windows Defender Functionalities Via Registry Keys tags:
– attack.defense-evasion
– attack.t1562.001 logsource:
product: windows category: registry_set
detection: selection_main:
TargetObject|contains:
– ‘SOFTWAREMicrosoftWindows Defender’
– ‘SOFTWAREPoliciesMicrosoftWindows Defender Security Center’
– ‘SOFTWAREPoliciesMicrosoftWindows Defender’ selection_dword_1:
TargetObject|endswith:
– ‘DisableAntiSpyware’
– ‘DisableAntiVirus’
– ‘DisableBehaviorMonitoring’
– ‘DisableBlockAtFirstSeen’
– ‘DisableEnhancedNotifications’
– ‘DisableIntrusionPreventionSystem’
– ‘DisableIOAVProtection’
– ‘DisableOnAccessProtection’
– ‘DisableRealtimeMonitoring’
– ‘DisableScanOnRealtimeEnable’
– ‘DisableScriptScanning’ Details: ‘DWORD (0x00000001)’
selection_dword_0: TargetObject|endswith:
– ‘DisallowExploitProtectionOverride’
– ‘FeaturesTamperProtection’
– ‘MpEngineMpEnablePus’
– ‘PUAProtection’
– ‘Signature UpdateForceUpdateFromMU’
– ‘SpyNetSpynetReporting’
– ‘SpyNetSubmitSamplesConsent’
– ‘Windows Defender Exploit GuardControlled Folder AccessEnableControlledFolderAccess’
Details: ‘DWORD (0x00000000)’
filter_optional_symantec:
Image|startswith: ‘C:Program FilesSymantecSymantec Endpoint Protection’
Image|endswith: ‘sepWscSvc64.exe’
condition: selection_main and 1 of selection_dword_* and not 1 of filter_optional_*
falsepositives:
– Administrator actions via the Windows Defender interface
– Third party Antivirus level: high
(Source: Surface Web)
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
STRATEGIC RECOMMENDATIONS
- Implement competent security protocols and encryption, authentication, or access credentials configurations to access critical systems in your cloud and local environments.
- Ensure that backups of critical systems are maintained, which can be used to restore data in case a need arises.
MANAGEMENT RECOMMENDATIONS
- A data breach prevention plan must be developed considering (a) the type of data being managed by the company; (b) the remediation process; (c) where and how the data is stored; (d) if there is a requirement to inform the local authority.
- Enable zero-trust architecture and multifactor authentication (MFA) to mitigate the compromise of credentials.
- Foster a culture of cybersecurity, where you encourage and invest in employee training so that security is an integral part of your organization.
TACTICAL RECOMMENDATIONS
- Update all applications/software regularly with the latest versions and security patches alike.
- Add the Sigma rule for threat detection and monitoring, which will help to detect anomalies in log events, identify and monitor suspicious activities.
- Build and undertake safeguarding measures by monitoring/ blocking the IOCs and strengthening defence based on the tactical intelligence provided.
Active Malware of the Week
Type: Trojan| Objectives: Persistence | Target Technology: Windows OS | Target Geography: Global
CYFIRMA collects data from various forums based on which the trend is ascertained. We identified a few popular malwares that were found to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the week
This week, “CrystalX RAT” malware is in focus.
Overview of Operation CrystalX Malware
The sample analyzed, identified as CrystalX, demonstrates consistent behavior with a covert and evasive threat operating within a system environment. Rather than executing in a straightforward or easily observable manner, malware employs indirect execution techniques and integrates its activity with legitimate system processes. This approach suggests a deliberate attempt to reduce visibility and avoid traditional detection mechanisms.
CrystalX further exhibits characteristics of a sophisticated threat through its interaction with core system components and reliance on trusted processes to mask its operations. By aligning its behavior with normal system functionality, it enhances its ability to persist without raising immediate suspicion. Such techniques indicate a focus on maintaining a stable presence while minimizing the risk of exposure.
Overall, the observed activity associated with CrystalX reflects a threat that prioritizes stealth and persistence over immediate disruption. Although no direct impact is evident at this stage, its behavior suggests potential for prolonged unauthorized access, making continuous monitoring and deeper investigation essential.
Attack Method
CrystalX malware exhibits a structured and methodical execution approach that leverages native Windows components to reduce its operational visibility. The initial execution phase is facilitated through Windows Management Instrumentation (WMI), involving processes such as wmiadap.exe and wmiprvse.exe. This method enables the malware to execute indirectly through legitimate system frameworks, thereby minimizing reliance on conventional execution vectors. Additionally, the deployment of a randomly named executable within the temporary directory reflects a staged delivery mechanism designed to obscure its presence.
The execution flow further demonstrates deliberate process chaining, wherein the malware operates through trusted system processes, including svchost.exe under standard service groups. By embedding its activity within legitimate processes, the malware effectively blends into normal system operations, complicating detection efforts. The use of dynamically generated or non-descriptive executable names suggests the presence of modular components, potentially allowing malware to extend functionality or sustain persistence within the compromised environment.
From an analytical perspective, the malware incorporates obfuscation and packing techniques to conceal its structure and impede reverse engineering. These measures are indicative of an intent to evade signature-based detection mechanisms and delay in-depth analysis. Furthermore, behavioral similarities observed across executions suggest alignment with previously identified malicious patterns, despite potential variations in the underlying binary.
A notable aspect of the attack methodology is its interaction with low-level system components, particularly the DeviceKsecDD driver, which is associated with core security and cryptographic operations. Such interactions may indicate attempts to perform privileged actions, manipulate security-related processes, or establish secure communication channels. The concurrent use of modules related to authentication, cryptography, and remote procedure calls further supports the likelihood of controlled and potentially encrypted communication with external systems, underscoring a sophisticated and stealth-focused operational design.
The following are the TTPs based on the MITRE Attack Framework for Enterprise
| Tactic | Technique ID | Technique Name |
| Defense Evasion (TA0005) | T1027.002 | Obfuscated Files or Information: Software Packing |
| T1036 | Masquerading | |
| Execution (TA0002) | T1047 | Windows Management Instrumentation |
| Privilege Escalation (TA0004) | T1068 | Exploitation for Privilege Escalation |
| Command and Control (TA0011) | T1071 | Application Layer Protocol |
INSIGHTS
- The behavior exhibited by CrystalX indicates a controlled and deliberate operational design, where activities are carried out in a measured and coordinated manner. Rather than generating noticeable disruption, the malware appears to focus on maintaining stability within the affected system, while executing its objectives. This structured approach suggests that its deployment is aligned with specific intent, emphasizing precision over indiscriminate activity.
- A further observation is the malware’s inclination to remain inconspicuous within the system environment. Its ability to align with normal operational patterns reflects an approach centered on minimizing visibility and avoiding unnecessary attention. By maintaining a low profile and limiting overt system impact, the malware demonstrates a clear emphasis on continuity of operation without interfering with standard processes.
- Moreover, the consistency observed in its behavioral patterns, despite potential variations in individual instances, points to a well-defined underlying framework. This uniformity indicates that the malware is developed with a structured methodology, ensuring predictable execution across different environments. Such consistency enhances its operational reliability while maintaining a coherent pattern of activity.
ETLM ASSESSMENT
From an ETLM perspective, threats such as CrystalX indicate a gradual shift toward low-visibility operations that may increasingly challenge traditional detection and response approaches within organizations. Future impact is likely to manifest through prolonged, unnoticed presence within enterprise environments, potentially affecting internal trust, data reliability, and operational transparency. As such threats continue to evolve, employees may unknowingly interact with compromised systems during routine activities, contributing to extended exposure periods without immediate indicators of compromise. This trend reflects a broader movement in the threat landscape where persistence, subtlety, and integration into normal workflows are expected to play a more significant role in shaping organizational risk.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems.
YARA Rules
rule CrystalX_String_IOCs
meta:
description = “Detects CrystalX using string-based IOCs (hash artifacts)” author = “CYFIRMA”
date = “2026-04-21”
strings:
/* Malware Sample Hash artifacts as strings */
$hash_md5 = “0086bd9d9053890e8ed999a4444e7b57”
$hash_sha1 = “ca33f55d44de5c97389785f7281c03050d7d6f33”
$hash_sha256 =
“edd7e88acbf5e866bf68fdb45d2dcb3fe19bb8c5014a4ddc65ff59703abd42da”
condition:
any of ($hash_*)
Recommendations
Strategic Recommendations
These are high-level, long-term initiatives to strengthen organizational cybersecurity posture:
- Establish a behavior-driven security strategy that prioritizes the detection of abnormal system activities rather than relying solely on signature-based tools.
- Strengthen visibility across endpoints and system processes to ensure that hidden or low-noise threats can be identified effectively.
- Integrate threat intelligence practices into security operations to continuously align defenses with evolving threat patterns.
- Promote a security-first culture across the organization, ensuring that awareness of subtle and persistent threats is embedded at all levels.
- Invest in centralized monitoring and logging capabilities to improve correlation and analysis of suspicious activities across environments.
Management Recommendations
These focus on policies, procedures, and governance to ensure proper oversight and risk mitigation:
- Ensure regular review of security monitoring outputs to identify patterns that may indicate prolonged or hidden threats.
- Support the implementation of advanced monitoring tools that can detect anomalies in system behavior and process execution.
- Encourage cross-team collaboration between IT, security, and operations teams for faster identification and response to suspicious activity.
- Define clear incident visibility and reporting protocols to ensure that subtle indicators are not overlooked.
- Allocate resources for continuous skill development of security teams to enhance their ability to detect and analyze evolving threats.
Tactical Recommendations
These are immediate, actionable steps to prevent, detect, and respond to malware at the operational level:
- Monitor and analyze the execution of system processes, such as WMI and service- based activities, for unusual patterns.
- Track activity within temporary directories to identify irregular or unauthorized executable behavior.
- Implement logging and alerting interactions with sensitive system components to detect abnormal usage.
- Regularly review process chains and parent-child relationships to identify hidden or indirect execution paths.
- Enable detailed endpoint logging to capture low-level activities that may indicate stealthy operations.
- Implement proactive security controls by monitoring and blocking identified IOCs, leveraging YARA rules for detection, and strengthening defenses based on actionable tactical intelligence.
CYFIRMA’s Weekly Insights
1. Weekly Attack Types and Trends Key Intelligence Signals:
- Attack Type: Ransomware Attacks, Malware Implant, Vulnerabilities & Exploits, Data Leaks.
- Objective: Unauthorized Access, Data Theft, Data Encryption, Financial Gains, Espionage.
- Business Impact: Data Loss, Financial Loss, Reputational Damage, Loss of Intellectual Property, Operational Disruption.
- Ransomware – Qilin Ransomware, RansomExx Ransomware| Malware – CrystalX RAT
- Qilin Ransomware – One of the ransomware groups.
- RansomExx Ransomware – One of the ransomware groups. Please refer to the trending malware advisory for details on the following: Malware – CrystalX RAT
Behavior – Most of these malwares use phishing and social engineering techniques as their initial attack vectors. Apart from these techniques, exploitation of vulnerabilities, defense evasion, and persistence tactics are being observed.
2. Threat Actor in Focus
Sapphire Sleet (Lazarus Group): A North Korea–Aligned Actor Focused on Financially Motivated Cyber Operations
- Threat Actor: Sapphire Sleet aka Lazarus Group
- Attack Type: Botnet Operations, Malware Implant, DLL Injection Attacks, Direct IP-based C2 Communication, Impersonation, Obfuscation, Open Proxy Usage, Credential Stealing, Social Engineering Attack, Supply Chain Attacks, Ransomware Attacks, Cryptocurrency theft, Exploitation of Vulnerabilities.
- Objective: Information theft, Espionage, Financial Gains.
- Suspected Target Technology: Windows, macOS, Linux, SAP Systems, Cryptocurrency Exchanges, Financial Platforms (including SWIFT), JetBrains TeamCity, Oracle Products, Dell Systems, Atlassian Confluence, Citrix NetScaler ADC/Gateway, GitHub and GitLab repositories, Microsoft Visual Studio Code.
- Suspected Target Geography: Australia, Brazil, Brunei, Canada, Chile, China, Darussalam, Democratic People’s Republic of Korea, France, Germany, Guatemala, Hong Kong, India, Indonesia, Islamic Republic of Iran, Japan, Myanmar, Philippines, Poland, Republic of Korea, Russia, Thailand, United Kingdom, United States, Vietnam, Bangladesh.
- Suspected Target Industries: Aerospace & Defense, Capital Markets, Consumer Finance, Cryptocurrency, Defense, Diversified Financial Services, Energy, Entertainment, Government, Hotels, Investment Trusts (REITs), Media, NGO, Real Estate, Restaurants & Leisure, Technology, Telecommunications, Thrifts and Mortgage, Banks, Venture Capital, Blockchain Organizations.
- Business Impact: Financial Loss, Data Theft, Operational Disruption, Reputational Damage.
About the Threat Actor
Since at least 2009, the Lazarus Group has been identified as a highly sophisticated, North Korea–aligned cyber threat actor associated with the Reconnaissance General Bureau (RGB), and is also tracked by the U.S. government as “Hidden Cobra.” The group is believed to operate through entities linked to DPRK military intelligence, including components associated with Lab 110.
Lazarus demonstrates advanced capabilities in malware development, with the ability to rapidly adapt, modify, and evolve tooling to support diverse operational objectives. The group has increasingly focused on financially motivated activities, particularly targeting cryptocurrency exchanges and digital asset platforms.
Operationally, Lazarus is understood to function as a multi-unit structure, including subgroups such as Andariel and Bluenoroff, each aligned to specific mission objectives ranging from regional targeting to global financial operations and espionage. The group’s ability to reuse infrastructure and coordinate across sub-units enables sustained, scalable, and adaptable cyber operations across multiple sectors and geographies.
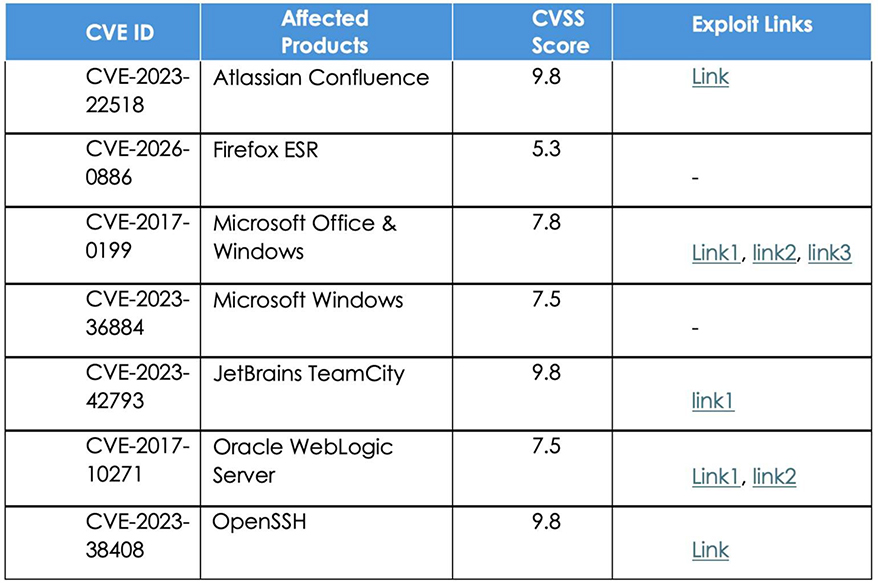
Details on Exploited Vulnerabilities
TTPs based on MITRE ATT&CK Framework
| Tactic | ID | Technique |
| Reconnaissance | T1591 | Gather Victim Org Information |
| Reconnaissance | T1591.004 | Gather Victim Org Information: Identify Roles |
| Reconnaissance | T1589.002 | Gather Victim Identity Information: Email Addresses |
| Reconnaissance | T1593.001 | Search Open Websites/Domains: Social Media |
| Resource Development | T1608.001 | Stage Capabilities: Upload Malware |
| Resource Development | T1608.002 | Stage Capabilities: Upload Tool |
| Resource Development | T1587.001 | Develop Capabilities: Malware |
| Resource Development | T1587.002 | Develop Capabilities: Code Signing Certificates |
| Resource Development | T1583.001 | Acquire Infrastructure: Domains |
| Resource Development | T1583.004 | Acquire Infrastructure: Server |
| Resource Development | T1583.006 | Acquire Infrastructure: Web Services |
| Resource Development | T1584.001 | Compromise Infrastructure: Domains |
| Resource Development | T1584.004 | Compromise Infrastructure: Server |
| ResourceDevelopment | T1585.001 | Establish Accounts: Social Media Accounts |
| ResourceDevelopment | T1585.002 | Establish Accounts: Email Accounts |
| ResourceDevelopment | T1588.002 | Obtain Capabilities: Tool |
| ResourceDevelopment | T1588.003 | Obtain Capabilities: Code Signing Certificates |
| ResourceDevelopment | T1588.004 | Obtain Capabilities: Digital Certificates |
| Initial Access | T1189 | Drive-by Compromise |
| Initial Access | T1566.001 | Phishing: Spear-phishing Attachment |
| Initial Access | T1566.002 | Phishing: Spear-phishing Link |
| Initial Access | T1566.003 | Phishing: Spear-phishing via Service |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell |
| Execution | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Execution | T1106 | Native API |
| Execution | T1204.001 | User Execution: Malicious Link |
| Execution | T1204.002 | User Execution: Malicious File |
| Execution | T1203 | Exploitation for Client Execution |
| Execution | T1059.003 | Command and Scripting Interpreter: Windows Command Shell |
| Execution | T1047 | Windows Management Instrumentation |
| Execution | T1059.005 | Command and Scripting Interpreter: Visual Basic |
| Persistence | T1505.004 | Server Software Component: IIS Components |
| Persistence | T1542.003 | Pre-OS Boot: Bootkit |
| Persistence | T1574.001 | Hijack Execution Flow: DLL |
| Persistence | T1574.013 | Hijack Execution Flow: KernelCallbackTable |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Persistence | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Persistence | T1098 | Account Manipulation |
| Persistence | T1547.009 | Boot or Logon Autostart Execution: Shortcut Modification |
| Privilege Escalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1098 | Account Manipulation |
| Privilege Escalation | T1547.009 | Boot or Logon Autostart Execution: Shortcut Modification |
| Privilege Escalation | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation | T1055.001 | Process Injection: Dynamic-link Library Injection |
| Privilege Escalation | T1574.001 | Hijack Execution Flow: DLL |
| Privilege Escalation | T1574.013 | Hijack Execution Flow: KernelCallbackTable |
| Privilege Escalation | T1134.002 | Access Token Manipulation: Create Process with Token |
| Privilege Escalation | T1053.005 | Scheduled Task/Job: Scheduled Task |
| DefenseEvasion | T1134.002 | Access Token Manipulation: Create Process with Token |
| DefenseEvasion | T1218 | System Binary Proxy Execution |
| DefenseEvasion | T1218.005 | System Binary Proxy Execution: Mshta |
| DefenseEvasion | T1218.010 | System Binary Proxy Execution: Regsvr32 |
| DefenseEvasion | T1218.011 | System Binary Proxy Execution: Rundll32 |
| DefenseEvasion | T1620 | Reflective Code Loading |
| DefenseEvasion | T1070 | Indicator Removal |
| DefenseEvasion | T1070.003 | Indicator Removal: Clear Command History |
| DefenseEvasion | T1070.004 | Indicator Removal: File Deletion |
| DefenseEvasion | T1070.006 | Indicator Removal: Timestomp |
| DefenseEvasion | T1202 | Indirect Command Execution |
| DefenseEvasion | T1036.003 | Masquerading: Rename Legitimate Utilities |
| DefenseEvasion | T1036.004 | Masquerading: Masquerade Task or Service |
| DefenseEvasion | T1036.005 | Masquerading: Match Legitimate Resource Name or Location |
| DefenseEvasion | T1036.008 | Masquerading: Masquerade File Type |
| DefenseEvasion | T1027.002 | Obfuscated Files or Information: Software Packing |
| DefenseEvasion | T1027.007 | Obfuscated Files or Information: Dynamic API Resolution |
| DefenseEvasion | T1027.009 | Obfuscated Files or Information: Embedded Payloads |
| DefenseEvasion | T1027.013 | Obfuscated Files or Information: Encrypted/Encoded File |
| DefenseEvasion | T1542.003 | Pre-OS Boot: Bootkit |
| DefenseEvasion | T1220 | XSL Script Processing |
| DefenseEvasion | T1055.001 | Process Injection: Dynamic-link Library Injection |
| DefenseEvasion | T1497.003 | Virtualization/Sandbox Evasion: Time Based Evasion |
| DefenseEvasion | T1622 | Debugger Evasion |
| DefenseEvasion | T1140 | Deobfuscate/Decode Files or Information |
| DefenseEvasion | T1564.001 | Hide Artifacts: Hidden Files and Directories |
| DefenseEvasion | T1221 | Template Injection Authentication Process: Conditional Access Policies |
| DefenseEvasion | T1574.001 | Hijack Execution Flow: DLL |
| DefenseEvasion | T1574.013 | Hijack Execution Flow: KernelCallbackTable |
| DefenseEvasion | T1497.001 | Virtualization/Sandbox Evasion: System Checks |
| DefenseEvasion | T1553.002 | Subvert Trust Controls: Code Signing |
| DefenseEvasion | T1078 | Valid Accounts |
| DefenseEvasion | T1562.001 | Impair Defenses: Disable or Modify Tools |
| DefenseEvasion | T1562.004 | Impair Defenses: Disable or Modify System Firewall |
| DefenseEvasion | T1656 | Impersonation |
| Credential Access | T1056.001 | Input Capture: Keylogging |
| Credential Access | T1110.003 | Brute Force: Password Spraying |
| Credential Access | T1557.001 | Adversary-in-the-Middle: LLMNR/NBT-NS Poisoning and SMB Relay |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1497.001 | Virtualization/Sandbox Evasion: System Checks |
| Discovery | T1497.003 | Virtualization/Sandbox Evasion: Time Based Evasion |
| Discovery | T1087.002 | Account Discovery: Domain Account |
| Discovery | T1010 | Application Window Discovery |
| Discovery | T1046 | Network Service Discovery |
| Discovery | T1622 | Debugger Evasion |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1012 | Query Registry |
| Discovery | T1614.001 | System Location Discovery: System Language Discovery |
| Discovery | T1016 | System Network Configuration Discovery |
| Discovery | T1049 | System Network Connections Discovery |
| Discovery | T1033 | System Owner/User Discovery |
| Discovery | T1124 | System Time Discovery |
| LateralMovement | T1021.002 | Remote Services: SMB/Windows Admin Shares |
| LateralMovement | T1021.001 | Remote Services: Remote Desktop Protocol |
| LateralMovement | T1021.004 | Remote Services: SSH |
| LateralMovement | T1534 | Internal Spear-phishing |
| Collection | T1056.001 | Input Capture: Keylogging |
| Collection | T1560 | Archive Collected Data |
| Collection | T1560.001 | Archive Collected Data: Archive via Utility |
| Collection | T1560.002 | Archive Collected Data: Archive via Library |
| Collection | T1560.003 | Archive Collected Data: Archive via Custom Method |
| Collection | T1557.001 | Adversary-in-the-Middle: LLMNR/NBT-NS Poisoning and SMB Relay |
| Collection | T1005 | Data from Local System |
| Collection | T1074.001 | Data Staged: Local Data Staging |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
| Command and Control | T1571 | Non-Standard Port |
| Command and Control | T1132.001 | Data Encoding: Standard Encoding |
| Command and Control | T1001.003 | Data Obfuscation: Protocol or Service Impersonation |
| Command and Control | T1573.001 | Encrypted Channel: Symmetric Cryptography |
| Command and Control | T1090.001 | Proxy: Internal Proxy |
| Command and Control | T1090.002 | Proxy: External Proxy |
| Command and Control | T1008 | Fallback Channels |
| Command and Control | T1105 | Ingress Tool Transfer |
| Command and Control | T1104 | Multi-Stage Channels |
| Command and Control | T1102.002 | Web Service: Bidirectional Communication |
| Exfiltration | T1041 | Exfiltration Over C2 Channel |
| Exfiltration | T1567.002 | Exfiltration Over Web Service: Exfiltration to Cloud Storage |
| Exfiltration | T1048.003 | Exfiltration Over Alternative Protocol: Exfiltration Over Unencrypted Non-C2 Protocol |
| Impact | T1561.001 | Disk Wipe: Disk Content Wipe |
| Impact | T1561.002 | Disk Wipe: Disk Structure Wipe |
| Impact | T1489 | Service Stop |
| Impact | T1485 | Data Destruction |
| Impact | T1529 | System Shutdown/Reboot |
| Impact | T1491.001 | Defacement: Internal Defacement |
Latest Developments Observed
The threat actor is observed executing a macOS-focused campaign that relies on social engineering, tricking users into running malicious AppleScript files, disguised as legitimate software updates. This activity reflects new execution patterns, combining user-initiated actions with multi-stage payload delivery to evade built-in macOS security controls. The campaign targets individuals in the cryptocurrency and finance sectors, leading to credential harvesting and large-scale data exfiltration. The primary objective appears to be financial gains through theft of sensitive data and cryptocurrency assets while maintaining low operational visibility.
ETLM Insights
Sapphire Sleet (Lazarus Group) is assessed as a North Korea–aligned cyber threat actor operating as part of a broader, state-directed ecosystem attributed to the Reconnaissance General Bureau (RGB), with objectives spanning financial gains, strategic espionage, and disruptive operations. Rather than functioning as a single entity, the group represents a modular and adaptive structure in which multiple operational units align with shifting national priorities.
Operationally, Lazarus-linked activity reflects a shared and scalable intrusion model, characterized by the reuse of infrastructure, malware, and tradecraft across campaigns. This interconnected approach enables flexible deployment of capabilities, sustained access across diverse targets, and reduced attribution clarity. The group’s ability to coordinate across units and adapt operational focus enhances both persistence and overall campaign effectiveness.
Based on observed behavioral patterns, the group is likely to continue evolving its modular structure while expanding operational scope across financial and strategic domains. This positions Lazarus as a persistent and multi-dimensional threat, with ongoing risks to digital assets, sensitive intelligence, and critical organizational environments.
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
YARA Rules
rule Lazarus_Suspicious_IOCs_Cluster
meta:
description = “Detection of suspicious domains, IPs, CVEs, and files linked to Lazarus-like activity”
author = “CYFIRMA” date = “2026-04-20”
strings:
/* Domains */
$d1 = “sfrclak.com” nocase
$d2 = “360scanner.store” nocase
$d3 = “trustpdfs.com” nocase
$d4 = “markethubuk.com” nocase
$d5 = “mediostresbarbas.com.ar” nocase
/* IPs */
$ip1 = “59.150.105.114”
$ip2 = “52.231.162.138”
$ip3 = “52.160.46.145”
$ip4 = “51.250.75.17”
$ip5 = “184.168.221.57”
/* CVEs */
$cve1 = “CVE-2017-0199”
$cve2 = “CVE-2023-22518”
$cve3 = “CVE-2023-36884”
$cve4 = “CVE-2023-42793”
$cve5 = “CVE-2026-0886”
$cve6 = “CVE-2023-38408”
/* File Names / Hash Indicators */
$f1 = “win32 exe” nocase
$f2 = “20140702.txt.gz” nocase
$f3 = “unblockhostid.exe” nocase
$f4 = “451c23709ecd5a8461ad060f6346930c”
$f5 = “a44812b44591121f3e711223db099043d4d72288e4f436dba2fb935b6d888d40”
$f6 = “.rels” nocase
condition:
any of ($d*) or any of ($ip*) or any of ($cve*) or any of ($f*)
Recommendations
Strategic Recommendations
- Incorporate Digital Risk Protection (DRP) as part of the overall security posture to proactively defend against impersonations and phishing attacks.
- Assess and deploy alternatives for an advanced endpoint protection solution that provides detection/prevention for malware and malicious activities that do not rely on signature-based detection methods.
- Block exploit-like behaviour. Monitor endpoints memory to find behavioural patterns that are typically exploited, including unusual process handle requests. These patterns are features of most exploits, whether known or new. This will be able to provide effective protection against zero-day/critical exploits and more, by identifying such patterns.
Management Recommendations
- Invest in user education and implement standard operating procedures for the handling of financial and sensitive data transactions commonly targeted by impersonation attacks. Reinforce this training with context-aware banners and in- line prompts to help educate users.
- Develop a cyber threat remediation program and encourage employee training to detect anomalies proactively.
Tactical Recommendations
- For better protection coverage against email attacks (like spear phishing, business email compromise, or credential phishing attacks), organizations should augment built-in email security with layers that take a materially different approach to threat detection.
- Protect accounts with multi-factor authentication. Exert caution when opening email attachments or clicking on embedded links supplied via email communications, SMS, or messaging.
- Apply security measures to detect unauthorized activities, protect sensitive production, and process control systems from cyberattacks.
- Add the YARA rules for threat detection and monitoring, which will help to detect anomalies in log events, and identify and monitor suspicious activities.
- Build and undertake safeguarding measures by monitoring/ blocking the IOCs and strengthening defence based on the tactical intelligence provided
3. Major Geopolitical Developments in Cybersecurity
Sweden Accuses Russia of Intensifying Cyber Attacks on Infrastructure
Russian intelligence services have pivoted from simple nuisance tactics to high-stakes sabotage, according to the Swedish Civil Defense Ministry. During a conference in Stockholm, Ministry officials explained that over the past year, pro-Russian groups have moved beyond merely overwhelming websites in Europe with traffic and are now actively attempting to launch destructive cyberattacks against European organizations. This shift highlights a growing anxiety among European officials regarding the safety of critical infrastructure, such as power plants and water treatment facilities, which are increasingly viewed as primary targets for Russian operatives.
ETLM Assessment:
In recent months, the threat has already manifested in several neighboring nations, most notably in Poland, where the government reported that security forces repelled a major wave of Russian intelligence attacks against power plants and renewable energy sites in December 2025. Sweden, Norway, and Denmark – all of which remain firm supporters of Ukraine in its ongoing struggle against Russian aggression – have faced similar cyber-attacks. Swedish officials specifically noted a spring 2025 incident where security systems at a heating plant in Western Sweden successfully thwarted a group linked to Russian intelligence. Stockholm concludes that these combined efforts represent a move toward more reckless and dangerous behavior that could have severe consequences for society at large.
The French personal documents authority breached
The French Interior Ministry confirmed that a significant cyberattack on the National Agency for Secure Documents (ANTS) may have compromised the personal data of numerous citizens. The breach targeted the central portal used for managing sensitive documents like passports, driver’s licenses, and residency permits. While the ministry clarified that administrative attachments and uploaded documents remain secure, hackers likely accessed login credentials, names, dates of birth, and unique account identifiers. In some instances, contact details including phone numbers and physical addresses, were also exposed, though officials maintain the stolen data is insufficient for unauthorized account takeovers.
ETLM Assessment:
This intrusion is the latest in a troubling wave of security failures hitting French public institutions. In early 2026, the Education Ministry reported a similar leak involving student data via the ÉduConnect platform, which followed a massive February breach of the National Bank Accounts File that exposed details tied to 1.2 million accounts. The identity of the attackers and the full scale of the breach remain unknown, and the government has yet to determine whether these recurring incidents across the educational, financial, and civil sectors are linked to a broader coordinated campaign. However, the fact that it targeted identity documents specifically suggests this wasn’t just a random hit by cyber criminals – it was an attack on the very core of a citizen’s relationship with the state. The most likely perpetrators would be the governments of Russia and China. Russian groups like Fancy Bear (APT28) or Sandworm are often the first suspects due to their goal of undermining public trust in Western government institutions and hit back for EUs support of Ukraine; while the Chinese are known for their long-term data collection operations, focused on gaining strategic intelligence.
4. Rise in Malware/Ransomware and Phishing
Qilin Ransomware Impacts HIGASHIYAMA INDUSTRIES Co., Ltd
- Attack Type: Ransomware
- Target Industry: Construction, Wholesale Trade
- Target Geography: Japan
- Ransomware: Qilin Ransomware
- Objective: Data Theft, Data Encryption, Financial Gains
- Business Impact: Financial Loss, Data Loss, Reputational Damage
Summary:
CYFIRMA observed in an underground forum that a company from Japan, HIGASHIYAMA INDUSTRIES Co., Ltd (https[:]//www[.]Higashiyama[.]com/), was compromised by Qilin Ransomware. HIGASHIYAMA INDUSTRIES Co., Ltd. is a Tokyo- based wholesale company focused on construction safety equipment. It provides temporary site solutions, including scaffolding, fencing, site offices, and welfare facilities for construction and civil engineering projects. The exposed dataset appears to include a wide range of sensitive corporate and personal information associated with HIGASHIYAMA INDUSTRIES Co., Ltd., primarily consisting of internal documents and operational records. Based on the visible thumbnails, the compromised data likely contains financial statements, transaction records, invoices, and accounting sheets, along with procurement and logistics details. Additionally, there are indications of employee-related information such as identification documents, personnel records, and possibly resumes or HR forms. Some documents also suggest business correspondence, contractual records, and structured data tables that may include supplier or client information. Overall, the leak reflects a combination of financial, operational, and personally identifiable information (PII), which could pose risks related to financial fraud, identity exposure, and corporate intelligence gathering.
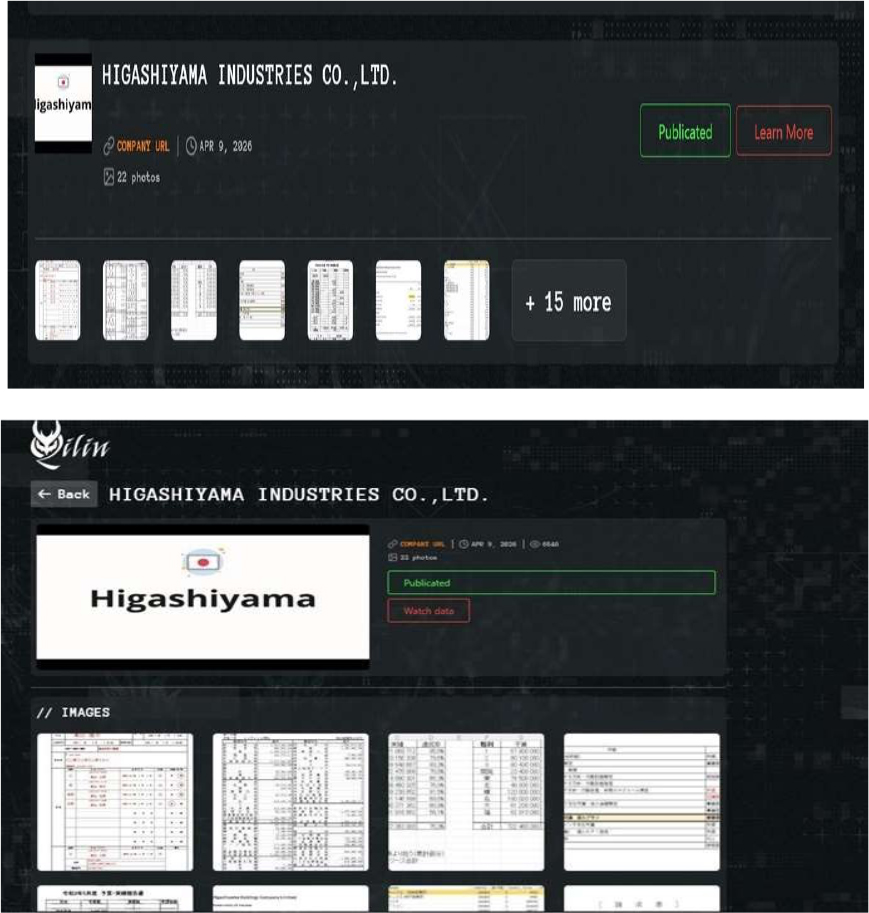
Source: Dark Web
Relevancy & Insights:
- The Qilin Ransomware group operates a Ransomware-as-a-Service (RaaS) model, allowing affiliates to carry out attacks while Qilin provides infrastructure and malware tools.
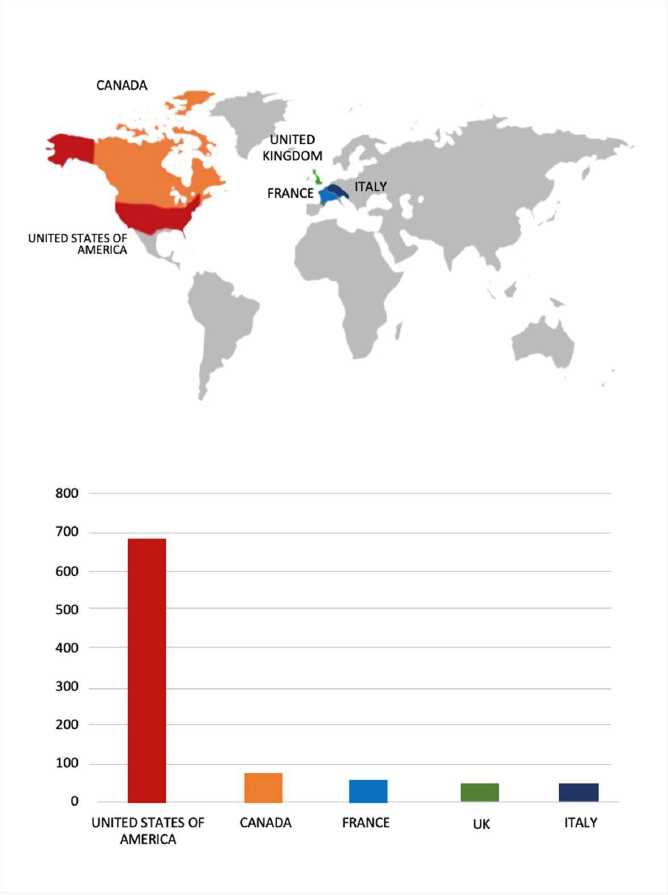
- The Qilin Ransomware group primarily targets countries such as the United States of America, Canada, France, the United Kingdom, and Italy.
- The Qilin Ransomware group primarily targets industries, including Manufacturing, Professional Goods & Services, Consumer Goods & Services, Healthcare, and Real Estate & Construction.
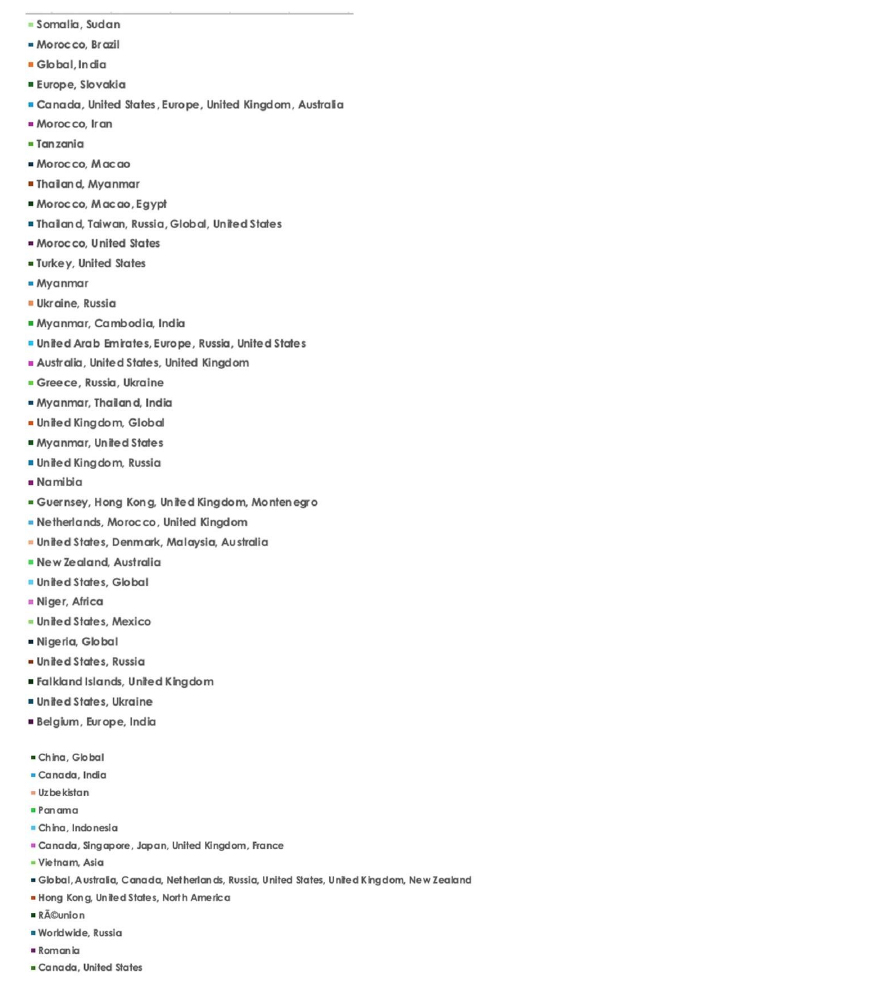
- Based on the Qilin Ransomware victims list from 1st Jan 2025 to 21st April 2026, the top 5 Target Countries are as follows:
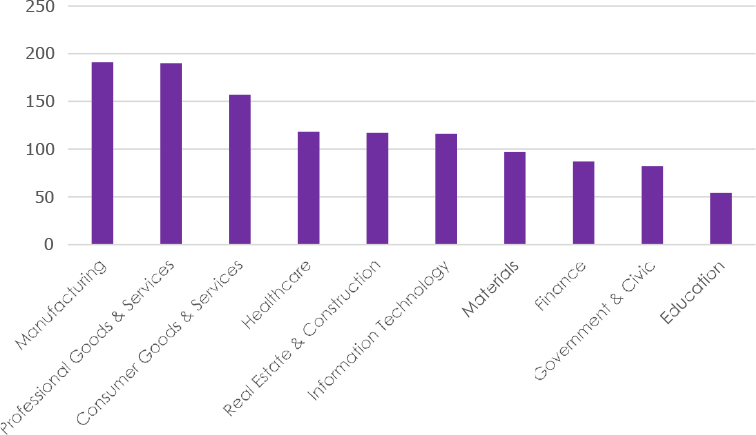
- The Top 10 Industries most affected by the Qilin Ransomware victims list from 1st Jan 2025 to 21st April 2026 are as follows:
ETLM Assessment:
According to CYFIRMA’s assessment, Qilin ransomware poses a significant threat to organizations of all sizes. Its evolving tactics, including double extortion (data encryption and leak threats), cross-platform capabilities (Windows and Linux, including VMware ESXi), and a focus on speed and evasion, make it a particularly dangerous actor.
RansomExx Ransomware Impacts GoTip
- Attack Type: Ransomware
- Target Industry: Information Technology (IT Services)
- Target Geography: Japan
- Ransomware: RansomExx Ransomware
- Objective: Data Theft, Data Encryption, Financial Gains
- Business Impact: Financial Loss, Data Loss, Reputational Damage
Summary: CYFIRMA observed in an underground forum that a company from Japan, GoTip(https[:]//www[.]gotip[.]jp/), was compromised by RansomExx Ransomware. GoTip is a Japanese platform offering a live-streaming enhancement tool that connects viewer tips (donations) to Bluetooth devices owned by creators. It transforms one-way broadcasts into interactive experiences by triggering physical device actions, such as lights or vibrations, based on tip amounts. The service includes mobile apps on Google Play and Apple App Store for creators and fans. The ransomware leak attributed to RansomEXX indicates the compromise of a full database backup associated with GoTip, exposing sensitive backend data structures and user-related records. The leaked content suggests that attacker access includes administrative and user tables containing personally identifiable information (PII) such as email addresses, usernames, and potentially account identifiers, along with authentication-related data like hashed passwords, tokens, and session-related fields. Additionally, the presence of fields linked to payment processing (e.g., Stripe account IDs), financial balances, and payout timestamps indicates exposure of financial and transaction-related data. Metadata such as account status, business types, and activity timestamps (created/updated records) are also included, enabling detailed profiling of users and administrators. The total size of compromised data is approximately 1.13 GB
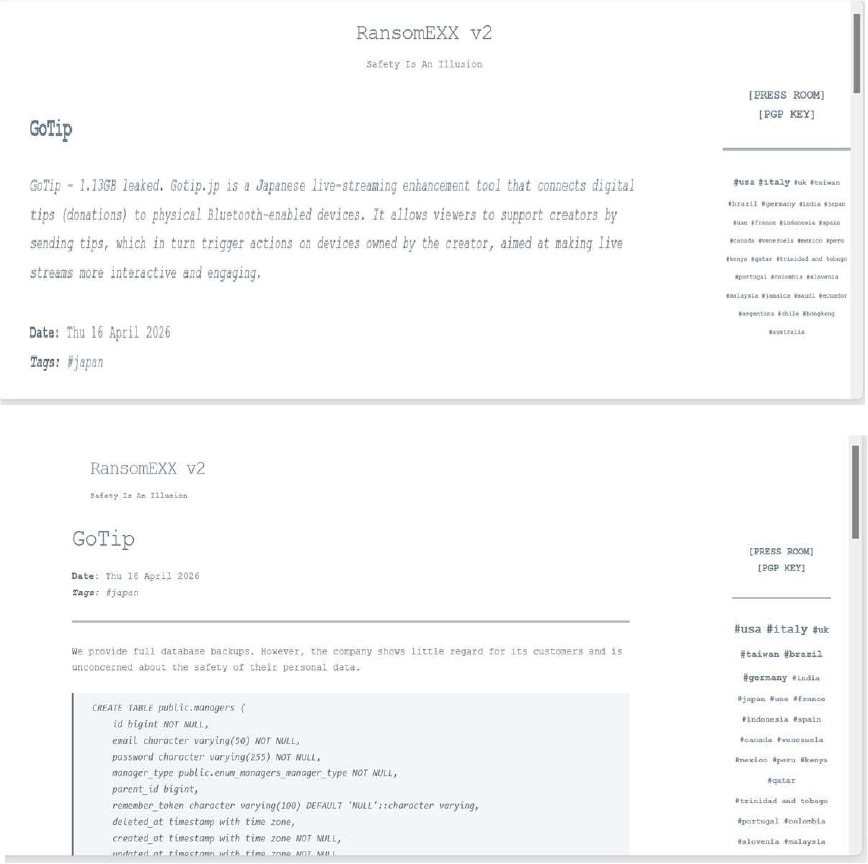
Source: Dark Web
Relevancy & Insights:
- RansomExx is a ransomware family that targeted multiple companies starting in mid- 2020. It shares commonalities with Defray777.
- The RansomExx Ransomware group primarily targets countries such as the United States of America, the United Arab Emirates (UAE), Germany, India, and Canada.
- The RansomExx Ransomware group primarily targets industries, including Professional Goods & Services, Transportation & Logistics, Information Technology, Real Estate & Construction, and Manufacturing.
- Based on the RansomExx Ransomware victims list from 1st July 2020 to 21st April 2026, the top 5 Target Countries are as follows:
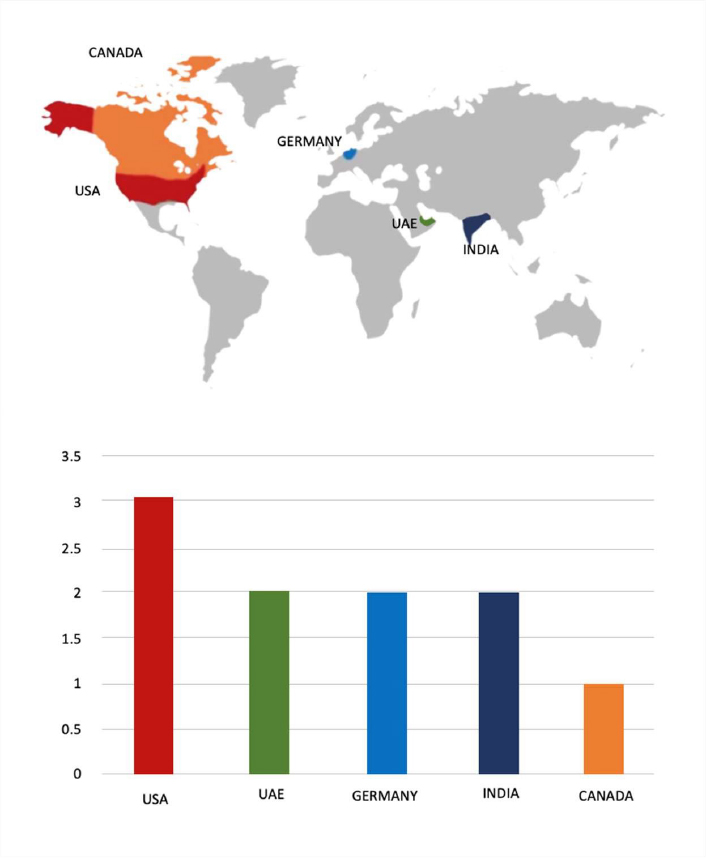
- The Top 10 Industries most affected by the RansomExx Ransomware victims list from 1st July 2020 to 21st April 2026 are as follows:
ETLM Assessment:
According to CYFIRMA’s assessment, Ransomexx ransomware represents a highly targeted and enterprise-focused threat that leverages human-operated intrusion techniques to maximize impact. The group conducts carefully planned attacks by gaining initial access through exposed services or compromised credentials, followed by privilege escalation, lateral movement, and selective deployment of ransomware across critical systems. Ransomexx demonstrates strong capabilities in defense evasion, including disabling security tools and backups prior to encryption, and supports cross-platform operations affecting both Windows and Linux environments. Its focus on high-value organizations, particularly within government and critical infrastructure sectors, combined with its strategic, low-noise operational approach, makes it a significant risk to enterprise cybersecurity, especially for organizations lacking robust monitoring, segmentation, and incident response capabilities.
5. Vulnerabilities and Exploits
Vulnerability in Jellyfin
- Attack Type: Vulnerabilities & Exploits
- Target Technology: Media Server / Streaming Application
- Vulnerability: CVE-2026-35031
- CVSS Base Score: 9.9 Source
- Vulnerability Type: Path Traversal
Summary:
The vulnerability allows a remote user to execute arbitrary code.
Relevancy & Insights:
The vulnerability exists due to path traversal in the subtitle upload endpoint when processing the Format field in subtitle upload requests.
Impact:
A remote user can upload a specially crafted subtitle to write arbitrary files and chain the issue to execute arbitrary code.
Exploitation requires the Upload Subtitles permission.
Affected Products:
https[:]//github[.]com/keraattin/CVE-2026-35031
Recommendations:
Monitoring and Detection: Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
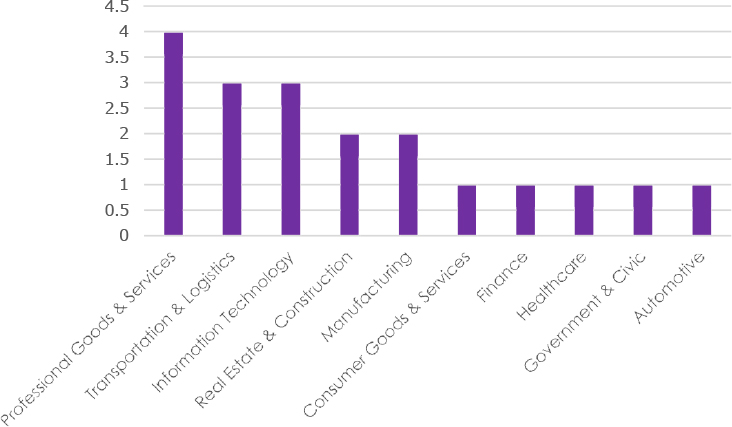
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies due to a range of vulnerabilities. The following are the top 5 most affected technologies
ETLM Assessment
Vulnerability in Jellyfin introduces significant risks to environments utilizing media server platforms for content streaming and management. As Jellyfin is widely deployed in self-hosted and enterprise media infrastructures, exploitation of this vulnerability could allow attackers to access sensitive files and internal system data. This may lead to exposure of credentials and further system compromise. Organizations leveraging such platforms must ensure proper patching, secure configuration, and continuous monitoring to prevent unauthorized access. Addressing this vulnerability is essential to maintaining the confidentiality of stored data and ensuring the security of media management systems across various deployment environments.
6. Latest Cyber-Attacks, Incidents, and Breaches
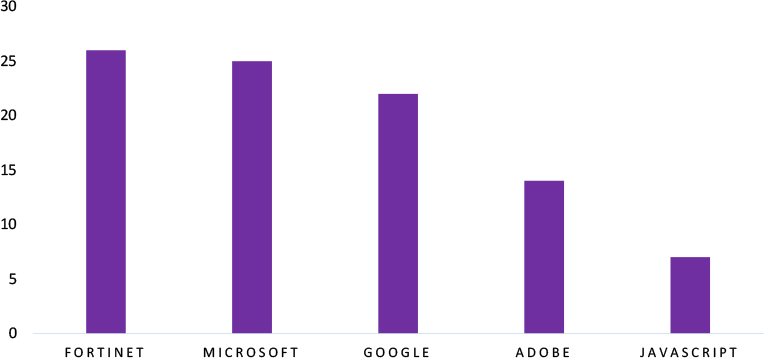
Lynx Ransomware attacked and published the data of Stonehenge Co Ltd
- Threat Actor: Lynx Ransomware
- Attack Type: Ransomware
- Objective: Data Leak, Financial Gains
- Target Technology: Web Applications
- Target Industry: Construction
- Target Geography: Thailand
- Business Impact: Operational Disruption, Data Loss, Financial Loss, Potential Reputational Damage
Summary:
Recently, we observed that Lynx Ransomware attacked and published the data of Stonehenge Co Ltd (https[:]//Stonehenge[.]co[.]th/) on its dark web website. Stonehenge Co Ltd is a company that operates in the Commercial & Residential Construction industry. The ransomware incident involving Stonehenge Co., Ltd., attributed to the Lynx ransomware group, indicates a compromise of sensitive corporate data likely exfiltrated prior to encryption as part of a double-extortion strategy. Based on available intelligence and leak-site previews, the compromised data appears to include internal business documents, confidential files, and financial records categorized as sensitive corporate information. Additionally, directory listings and file samples suggest exposure of operational data such as project-related documents, structured datasets, and potentially employee or administrative records.
Source: Dark Web
Relevancy & Insights:
- The Lynx Ransomware is confirmed to use a hybrid encryption approach, with AES-128 in CTR mode for fast file encryption and Curve25519 Donna for robust asymmetric key exchange, ensuring files are only recoverable with the attacker’s private key.
- Lynx provides a comprehensive platform for affiliates, including tools for managing victims, negotiating ransoms, and sharing access with sub-affiliates.
ETLM Assessment:
According to CYFIRMA’s assessment, Lynx ransomware has emerged as a significant threat in the cybersecurity landscape, leveraging advanced encryption and double extortion tactics to target small and medium-sized businesses. Its structured affiliate program and versatile ransomware toolkit make it a formidable force in the RaaS ecosystem.
7. Data Leaks
Dubai Health Authority Data Advertised on a Leak Site
- Attack Type: Data leak
- Target Industry: Healthcare Services
- Target Geography: The United Arab Emirates (UAE)
- Objective: Financial Gains
- Business Impact: Data Loss, Reputational Damage
Summary: The CYFIRMA research team identified a post on a dark web forum by a threat actor using the alias “Dark_habibi”, advertising the sale of allegedly compromised data from the Dubai Health Authority (UAE).
The post claims that the dataset contains a total of 836 files, which appear to include highly sensitive personal, medical, and governmental information. Based on the actor’s description, the exposed data may impact individuals across multiple nationalities and includes both personal identification records and institutional documents.
According to the threat actor, the leaked dataset includes:
- Passports belonging to individuals of various nationalities
- Emirates IDs and visa-related documents
- Certifications (academic, professional, and medical)
- Architectural diagrams and blueprints of clinics, hospitals, and medical facilities
- Personal signatures
- Government policy documents
- Internal reports, contracts, and other sensitive materials
The actor has also shared a sample of the data via a file-sharing platform and is offering the complete dataset for sale at a fixed price of $300. Additionally, contact details were provided for further communication.
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
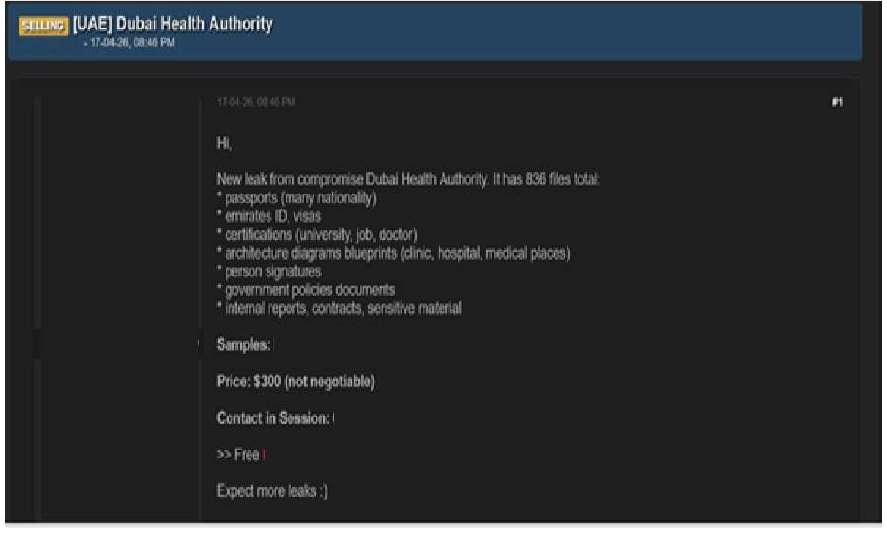
Source: Underground Forums
Japan Golf Company Data Advertised on a Leak Site
- Attack Type: Data leak
- Target Industry: Sporting Goods Retail (E-Commerce)
- Target Geography: Japan
- Objective: Data Theft, Financial Gains
- Business Impact: Data Loss, Reputational Damage
Summary: The CYFIRMA research team identified a post on a dark web forum by a threat actor using the alias “Logggedout,” advertising the sale of an allegedly compromised database linked to a Japan-based golf-related company (source referenced as itoborusa[.]com). The post indicates that the breach occurred on 17 April 2026 and claims the dataset contains over 1.7 million records. Based on the actor’s description and shared samples, the exposed data appears to include detailed transactional and customer-related information, potentially impacting a large number of individuals and business operations.
According to the threat actor, the leaked dataset includes:
- Customer and transaction IDs
- Product names, quantities, and pricing details
- Order and shipment information, including delivery status
- Customer contact details such as email addresses
- Shipping addresses and associated logistics data
- Payment-related references and transaction metadata
- Internal order processing and operational fields
The actor has provided sample records showcasing structured transactional data, likely extracted from an e-commerce or order management system. The dataset is being offered for sale at a price of $200, with additional details such as a transaction (qTox) ID and session key shared for direct communication. This incident suggests a significant exposure of commercial and customer data, which could lead to privacy risks, fraud, or further exploitation if acquired by malicious actors.
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
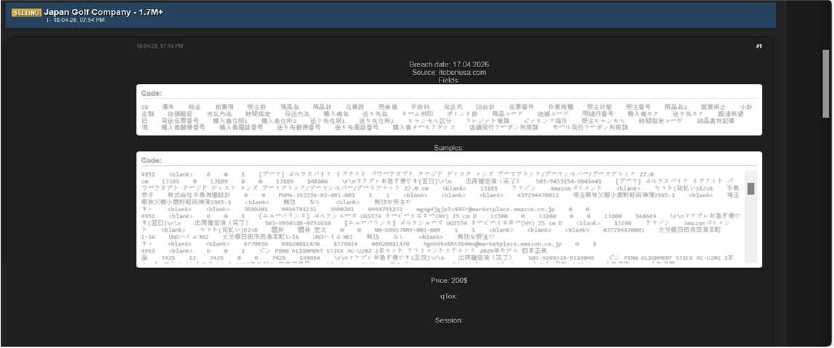
Source: Underground Forums
Relevancy & Insights:
Financially motivated cybercriminals are continuously looking for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to gain access and steal valuable data. Subsequently, the stolen data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor “Logggedout” is assessed as an active and capable entity focused on data-leak operations, with credible sources linking them to multiple incidents involving unauthorized system access and the distribution or sale of stolen data on dark web platforms. These activities highlight the evolving cyber threat landscape driven by underground criminal networks and emphasize the need for organizations to strengthen cybersecurity through continuous monitoring, enhanced threat intelligence, and proactive defenses to safeguard sensitive data and critical systems.
Recommendations: Enhance the cybersecurity posture by:
- Updating all software products to their latest versions is essential to mitigate the risk of vulnerabilities being exploited.
- Ensure proper database configuration to mitigate the risk of database-related attacks.
- Establish robust password management policies, incorporating multi-factor authentication and role-based access to fortify credential security and prevent unauthorized access.
8. Other Observations
The CYFIRMA research team identified a post on a dark web forum by a threat actor using the alias “Anonymous2090”, claiming responsibility for hacking a Thailand-based travel and tourism website.
According to the post, the actor alleges that they successfully compromised the website, exfiltrated its entire database, and subsequently took the platform offline. The threat actor has shared a download link to the allegedly stolen data, indicating that it is being distributed freely rather than sold.
Based on the information provided in the forum post, the exposed dataset appears to include multiple backend databases associated with the website’s infrastructure.
The actor also shared a database listing, suggesting the presence of the following:
- Primary application database (e.g., “data_tour”)
- System-related databases such as “information_schema”, “mysql”, and “performance_schema”
- Administrative database (e.g., “phpmyadmin”)
- Additional project-related databases such as “query_zego”, “test”, and “tour_system”
The inclusion of these databases indicates potential exposure of both user-related data and backend configuration details. While the exact volume and nature of compromised records are not specified, such databases typically contain sensitive information, which may include:
- User account details (names, emails, phone numbers)
- Authentication data (usernames, hashed passwords)
- Booking and travel-related records
- Administrative credentials and system configurations
The actor also provided a password for accessing the dataset, further suggesting intentional public dissemination of the stolen information.
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
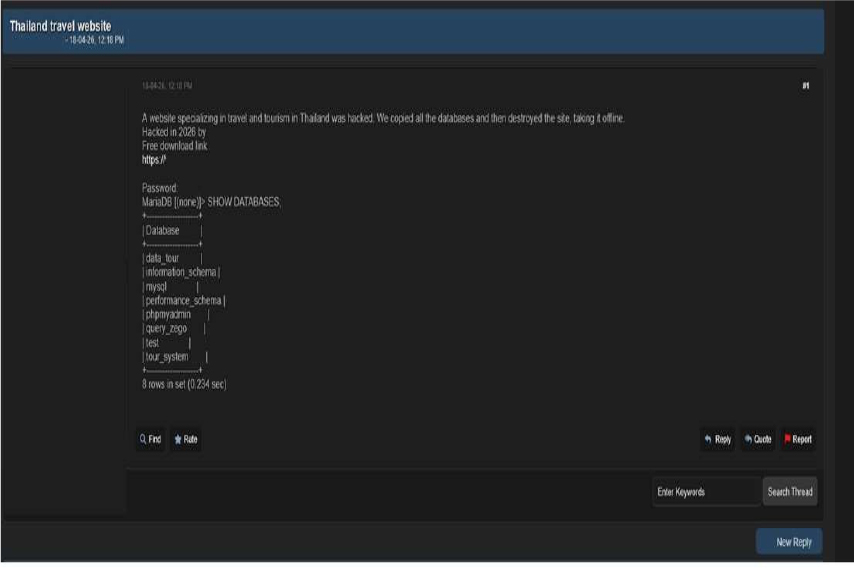
Source: Underground Forums
RECOMMENDATIONS
STRATEGIC RECOMMENDATIONS
- Attack Surface Management should be adopted by organisations, ensuring that a continuous closed-loop process is created between attack surface monitoring and security testing.
- Deploy a unified threat management strategy – including malware detection, deep learning neural networks, and anti-exploit technology – combined with vulnerability and risk mitigation processes.
- Incorporate Digital Risk Protection (DRP) in the overall security posture that acts as a proactive defence against external threats targeting unsuspecting customers.
- Implement a holistic security strategy that includes controls for attack surface reduction, effective patch management, and active network monitoring, through next-generation security solutions and a ready-to-go incident response plan.
- Create risk-based vulnerability management with deep knowledge about each asset. Assign a triaged risk score based on the type of vulnerability and criticality of the asset to help ensure that the most severe and dangerous vulnerabilities are dealt with first.
MANAGEMENT RECOMMENDATIONS
- Take advantage of global Cyber Intelligence, providing valuable insights on threat actor activity, detection, and mitigation techniques.
- Proactively monitor the effectiveness of risk-based information security strategy, the security controls applied, and the proper implementation of security technologies, followed by corrective actions, remediations, and lessons learned.
- Consider implementing Network Traffic Analysis (NTA) and Network Detection and Response (NDR) security systems to compensate for the shortcomings of EDR and SIEM solutions.
- Ensure that detection processes are tested to ensure awareness of anomalous events. Timely communication of anomalies should be continuously evolved to keep up with refined ransomware threats.
TACTICAL RECOMMENDATIONS
- Patch software/applications as soon as updates are available. Where feasible, automated remediation should be deployed since vulnerabilities are one of the top attack vectors.
- Consider using security automation to speed up threat detection, improved incident response, increased the visibility of security metrics, and rapid execution of security checklists.
- Build and undertake safeguarding measures by monitoring/ blocking the IOCs and strengthening defences based on the tactical intelligence provided.
- Deploy detection technologies that are behavioral anomaly-based to detect ransomware attacks and help to take appropriate measures.
- Implement a combination of security controls, such as CAPTCHA (completely Automated Public Turing test to tell Computers and Humans Apart), Device fingerprinting, IP backlisting, Rate-limiting, and Account lockout to thwart automated brute-force attacks.
- Ensure email and web content filtering uses real-time blocklists, reputation services, and other similar mechanisms to avoid accepting content from known and potentially malicious sources.
Situational Awareness – Cyber News
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
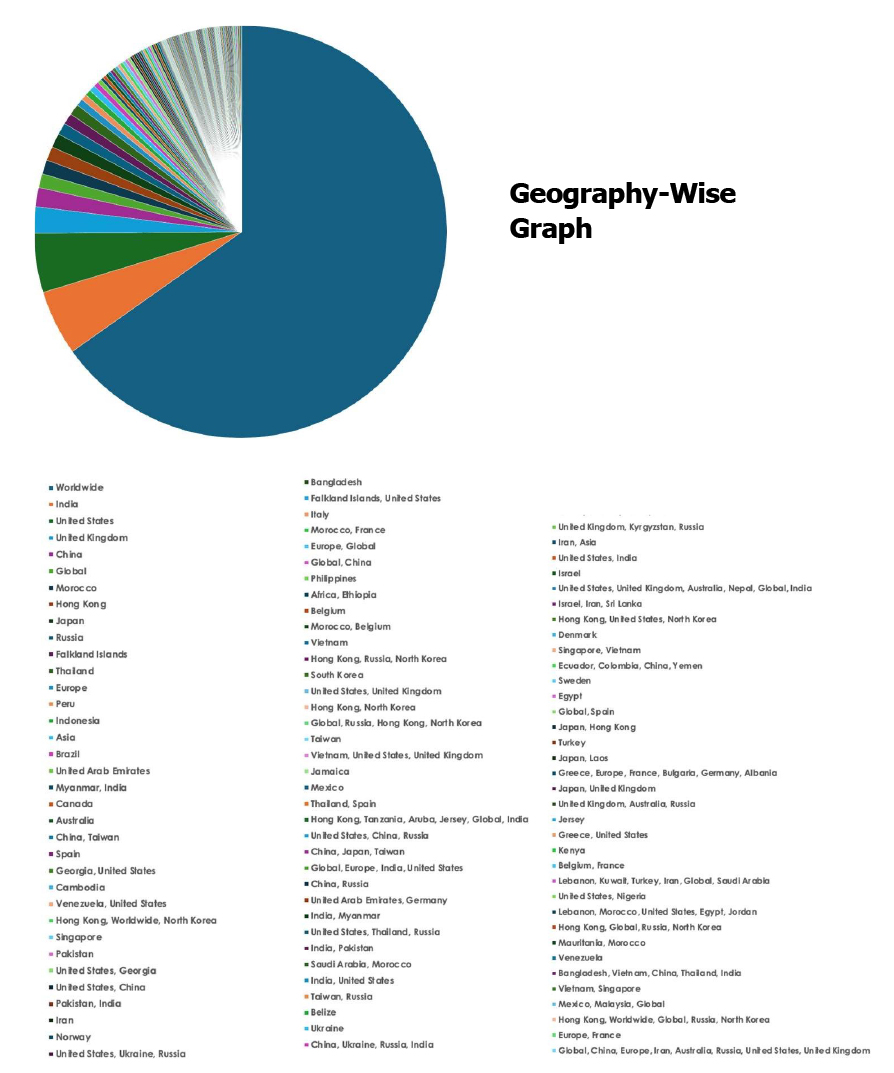
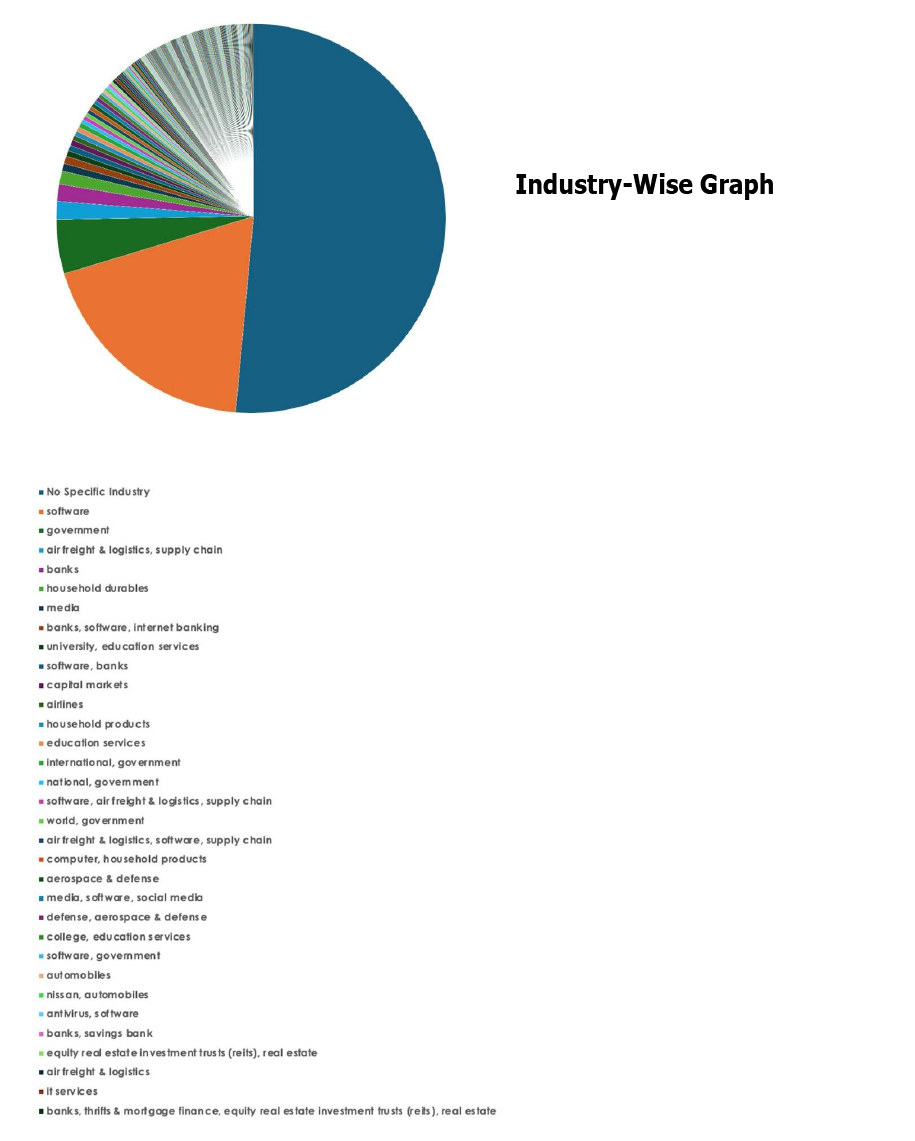
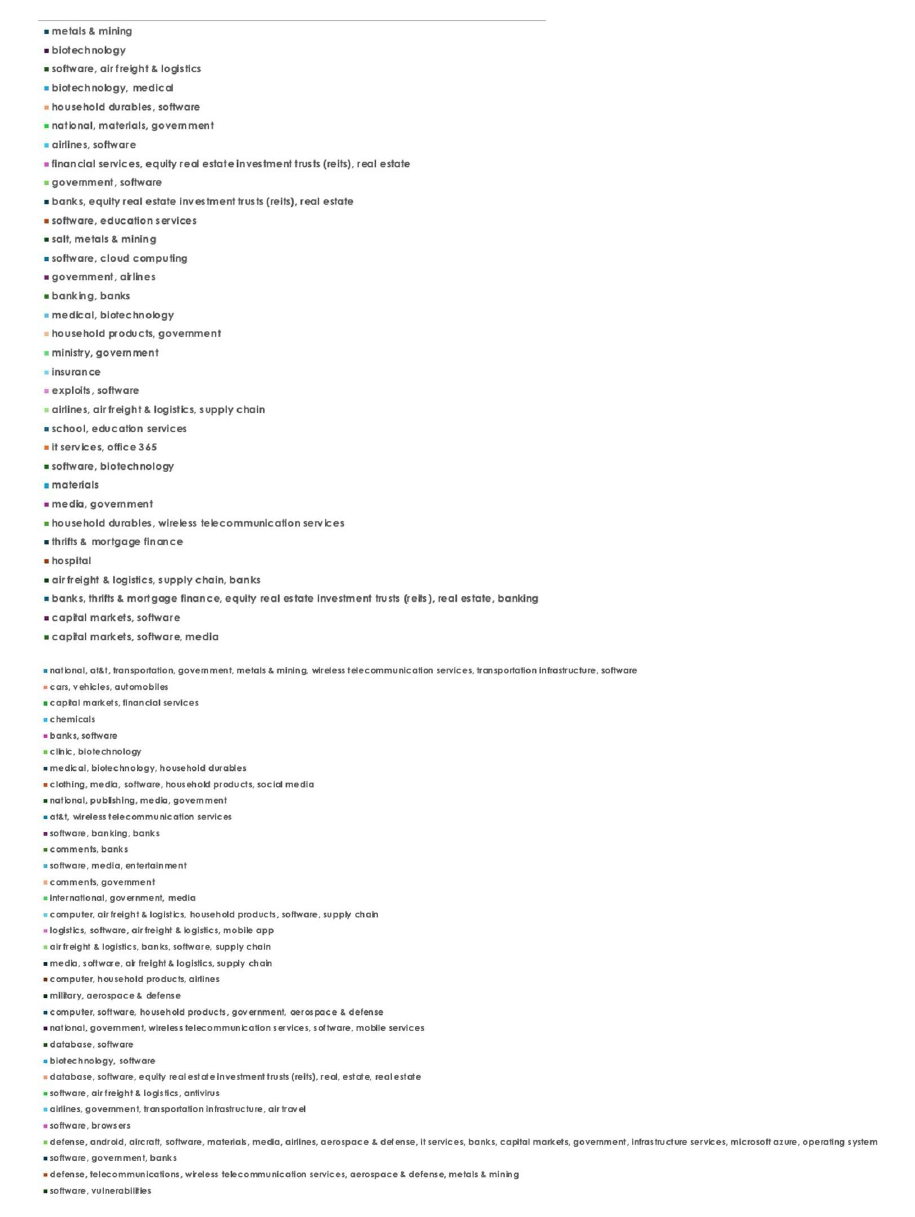
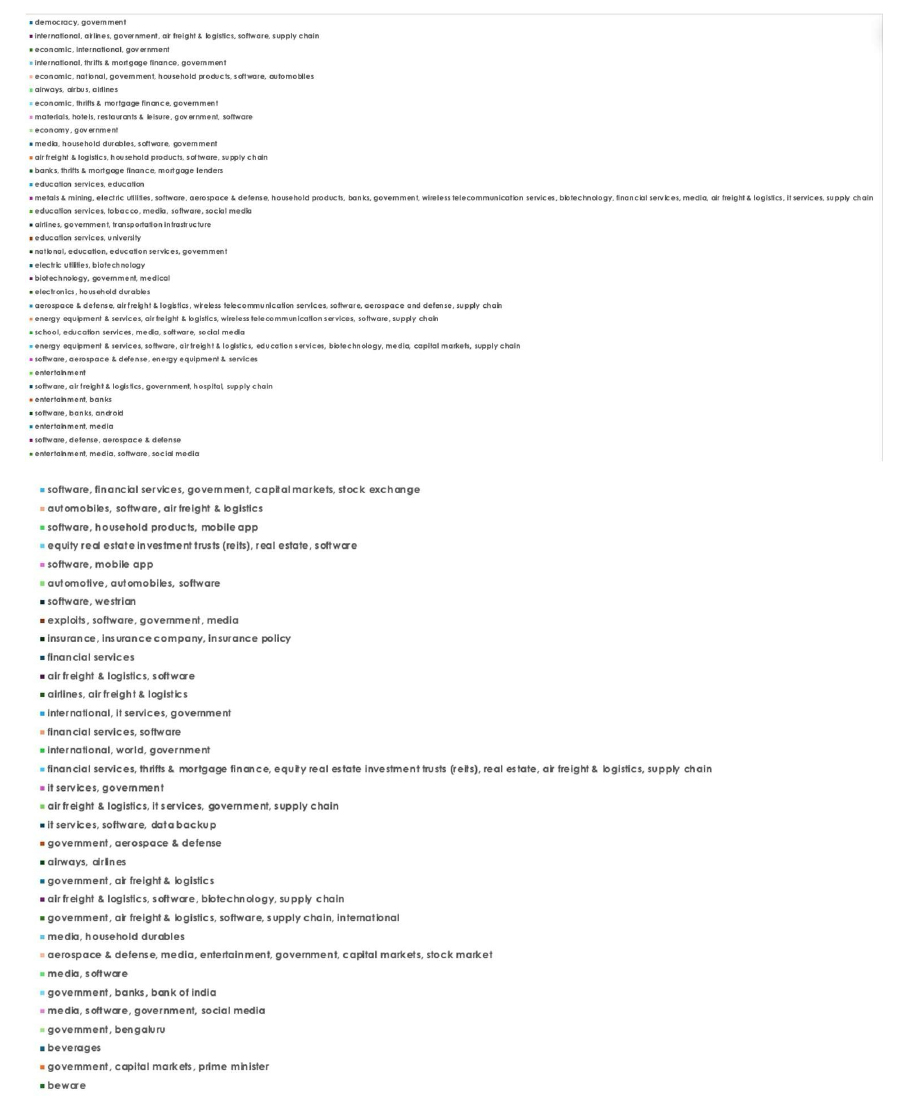
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR.
