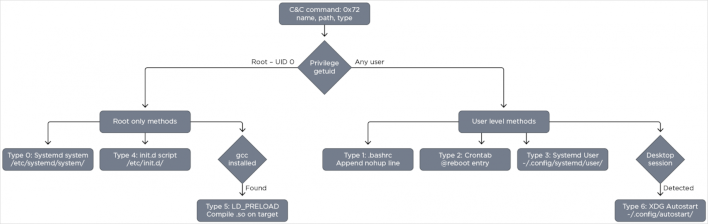
Researchers at Trend Micro have identified a frightening new Linux rootkit, dubbed Quasar Linux (QLNX,) and developers should be especially concerned. Per the report (which we spotted throughBleeping Computer‘s coverage,) QLNX is a Linux implant “designed for stealth and long-term persistence” that hides in memory and uses seven distinct persistence mechanisms. When combined, its persistence mechanisms make it difficult to actually “kill” QLNX, since any one of the seven can restart the process the instant it stops running.
Beyond stealth and persistence functionality, QLNX is also a dangerous, multi-faceted piece of malware. Process injection, peer-to-peer-networking, surveillance functionalities, credential harvesting, and filesystem monitoring are all within QLNX’s capabilities. Since it’s primarily being targeted at development environments (particularly across GitHub, AWS, Kubernetes, and more,) the intent seems to be to integrate QLNX into otherwise innocent apps and server hosts and perform supply-chain attacks by publishing malicious packages. We’ve seen that kind of attack before, when hackers hijacked Notepad++’s update servers. If combined with an exploit like Copy Fail, there’s potential for serious, wide-spread exploitation.
So, what can be done to mitigate QLNX attacks?Bleeping Computer‘scoverageis succinct, but for additional details Trend Micro’sdocumentationlists the official Indicators of Compromise (IOCs.) The seven filenames are as follows: Quaser-implant, libsecurity_utils.so.1, pam_security.so, hide_src_39ZzHo.c, pam_src_51YyC3.c, libpam_cache.so, and pcs_a3kf9x.c.
Trend Micro advises readers to use its Trend Vision One platform, but other mitigation tools armed with the correct updates should also be able to effectively wipe those files and help secure your systems. Just be sure to check again afterward in case a persistence mechanism kicks in, or reinfection occurs through some other vector. As always, we strongly advise readers to practice cybersecurity best practices, but especially in enterprise environments where data security is paramount. Best practices include two-factor authentication, keeping employees informed regarding phishing scams and other possible vectors of infection, acquiring files only from known, trusted sources, and using secured password managers.
Image Credit: BleepingComputer, Trend Micro