A large-scale malware delivery campaign has been targeting developers, gamers, and general users through fake tools hosted on GitHub, Netskope researchers have warned.
These “lures” are highly polished and appear legitimate, occasionally mimicking real projects, thus making them difficult to distinguish from safe software.
A dual-component trojan is delivered
Netskope threat researchers first discovered a trojanized GitHub repository ostensibly offering a Docker image of the OpenClaw AI assistant.
The repo was very convincing. “The README is polished and detailed, with installation instructions for both Linux and Windows and a companion GitHub.io page reinforces the legitimate appearance. Multiple contributors are listed, including a developer with a 568-star repository of their own, who was invited to collaborate during a private pre-launch phase. That developer contributed real, functional code to the scaffolding—Dockerfiles, install scripts, and configuration—possibly in good faith,” the researchers noted.
“Multiple throwaway GitHub accounts added stars and forks to the repositories without any legitimate activity, padding the credibility signal that the commit history alone could not provide.”
But the payload is actually a custom LuaJIT-based trojan designed to evade detection.
It uses a two-part structure – a legitimate runtime for executing Lua scripts (1unc.exe) and an obfuscated, encrypted script (license.txt) – that appear harmless when analyzed separately, but become malicious when executed together.
“This two-component design is deliberate. Standard automated analysis submits files individually. Each component passes and the malicious behavior only emerges when the batch file arms the pair in the right sequence,” the researchers explained.
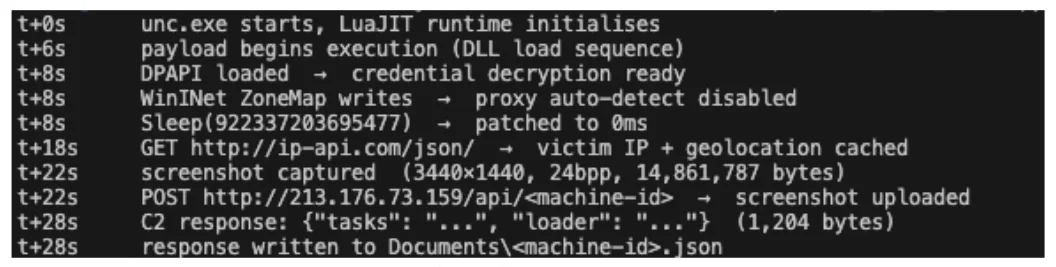
Once active, the malware quickly performs five anti-analysis checks and delays execution to bypass sandboxes. It also captures disables proxy auto-detection, checks the victim’s geolocation, captures a full screenshot of the victim’s desktop and sends it to the attackers, and waits for instructions from the command and control server.
The malware in action (Source: Netskope)
The attackers’ ultimate goal is to deliver an infostealer to the compromised users. To do that, they have distributed over 300 malicious packages disguised as AI developer tools, game cheats, crypto bots, Roblox scripts, and VPN crackers.
Common toolchain reveals AI-assisted malware campaign
The researchers found the same malicious binary in other repositories, operated by other user accounts. Two of these fake tools – a phone number location tracking tool and a tool for unlocking an advanced experience in the online game Fishing Planet – are still “phishing” for victims on GitHub.
All these malicious packages share the same underlying toolchain and infrastructure.
The naming patterns of the fake projects suggest that AI may be used to generate large volumes of convincing content at scale, allowing attackers to rapidly expand their reach across different audiences and platforms. 
“What this campaign represents is a purpose-built gap in the automated analysis pipeline,” the researchers noted.
“It includes two inert components that only become dangerous when executed together, a payload that sleeps for 29,000 years the moment a sandbox starts timing, and a lure factory that rotates audiences while the infrastructure stays constant.”

Subscribe to our breaking news e-mail alert to never miss out on the latest breaches, vulnerabilities and cybersecurity threats. Subscribe here!