A notorious group of hackers is currently causing major disruption globally by deploying the devastating Medusa ransomware. Tracked by Microsoft Threat Intelligence as Storm-1175, these hackers have turned the gap between a security flaw being found and a fix being installed into a high-speed race.
Microsoft researchers found that Storm-1175 specialises in hitting vulnerable perimeter assets, the systems and devices that connect a company’s private network directly to the public internet, that haven’t had their security updates yet.
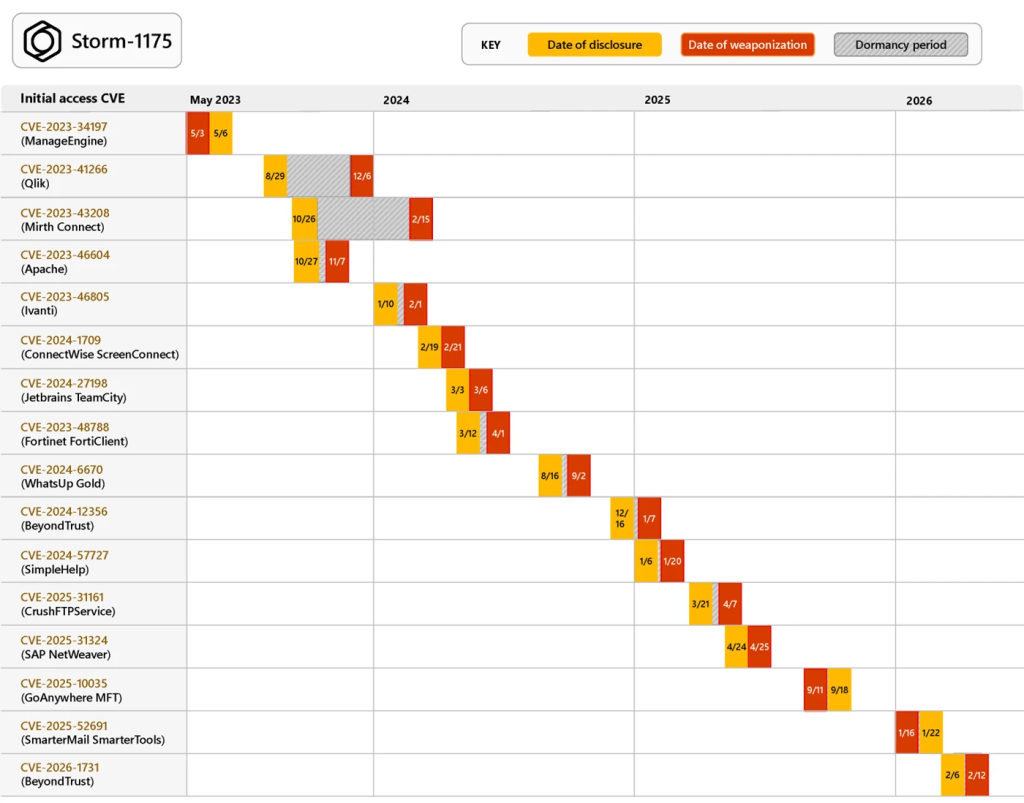
The group, reportedly, focuses on N-day vulnerabilities, which are security flaws that have already been reported to the public. While some hackers hide in a system for months, Storm-1175 often finishes the job in just a few days. In some cases, they have stolen data and locked down a whole network within 24 hours. “Storm-1175 rotates exploits quickly during the time between disclosure and patch availability,” Microsoft researchers noted.
This pace was clear during a recent attack on a SAP NetWeaver system (tracked as CVE-2025-31324). The flaw was announced on April 24, 2025, and by April 25, the group was already using it to launch Medusa ransomware operations. This efficiency has caused big problems for schools, law firms, and hospitals across the United Kingdom, the United States, and Australia.
Further investigation revealed that the group has exploited more than 16 different flaws since 2023, including software like Papercut (CVE-2023-27351) and JetBrains TeamCity (CVE-2024-27198). They are also surprisingly good at using zero-day exploits. In early 2026, they hit a service called SmarterMail (CVE-2026-23760) a full week before anyone knew a flaw existed.
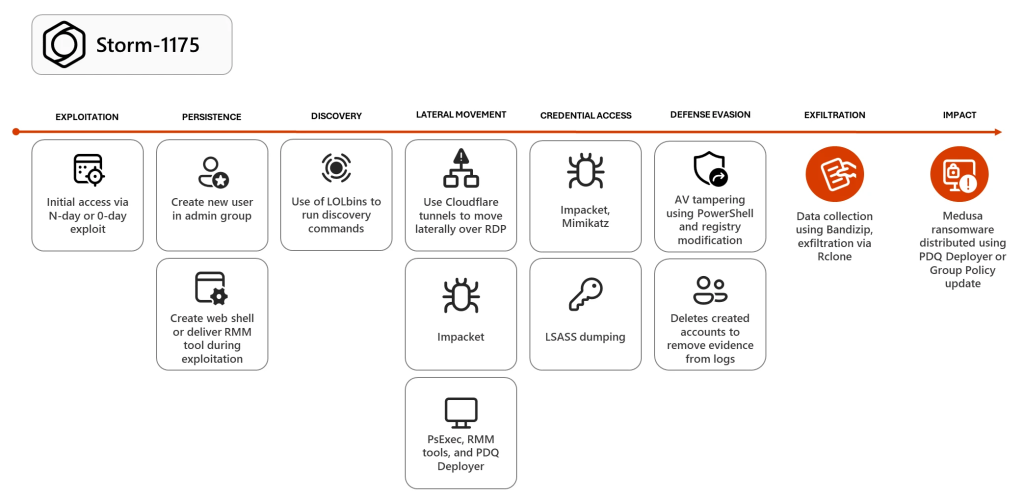
Once they get inside, they hijack everyday office tools like AnyDesk and ConnectWise ScreenConnect to move around without being noticed. Researchers noted in the blog post that they also use a tool called PDQ Deployer to spread the ransomware to every computer at once, while tools like Rclone and Bandizip are used to pack up and steal files.
Storm-1175 is particularly good at security tampering because, after initial access, they often use special permissions to tell the computer’s own antivirus to ignore the C: drive by adding it to an exclusion path. This blinds the system, allowing the ransomware to run without being stopped.
To stay safe, experts suggest that businesses need to be much quicker at installing updates. Using features like Tamper Protection can also stop hackers from turning off the antivirus.
The sophistication of these campaigns sets them apart from typical cybercrime. In a comment shared with Hackread.com, Adrian Culley, a Senior Sales Engineer at SafeBreach, provided his perspective on the growing threat, explaining that Storm-1175 represents a major shift in how hackers operate. He noted that the group’s ability to weaponise new flaws in mere hours creates a dangerous mismatch for businesses that rely on slow, traditional security checks.
“We’re seeing a clear escalation in the speed and coordination of operations tied to Storm-1175, particularly in how quickly newly disclosed and even zero-day vulnerabilities are being operationalized. This group, associated with Medusa ransomware, is moving from initial access to data exfiltration in hours, not days.”
“It’s also important to distinguish this activity from similarly named groups like MedusaLocker, which rely more on opportunistic access methods like RDP brute force. Storm-1175 is operating with a much more deliberate playbook, chaining exploits and leveraging remote management tooling to accelerate lateral movement and impact.”
“The bigger issue this highlights is a growing mismatch between attacker speed and how organizations validate their defenses. Point-in-time assessments and static scanning aren’t built for this pace. Security teams need continuous, real-world validation of how attacks actually progress through their environments, so they can identify and address exposure before it’s exploited.”