For most of us, Telegram is just a handy app for personal and group chats. But for the cybersecurity world, it has become something much more concerning. According to a detailed analysis by the research firm CYFIRMA, the app has turned into the primary “office” for hackers, effectively moving the shady dealings of the old Dark Web into a much faster and easier-to-reach space.
Previously, if you wanted to buy stolen data, you had to access the Tor network, which, as we know it, has been a constant target for police. When one of those old forums got shut down, the criminals lost everything. However, CYFIRMA’s latest research suggests that Telegram has fixed that problem for them.
According to their blog post, groups like IndoHaxSec now use it as a backup system. If their main channel gets banned, they simply point their followers to a new one. It takes minutes, and their business never really stops. This resilience makes it almost impossible for authorities to fully pull the plug.
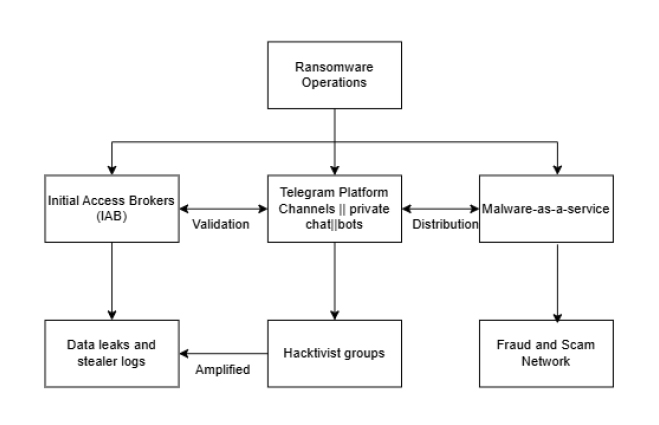
The Telegram app isn’t just for chatting anymore; it’s a fully automated shopping mall for crime because hackers now use bots (programmed scripts) to do the heavy lifting. These bots can search through millions of stolen passwords or process payments in seconds. Here is what is actually being traded on these channels:
- Initial Access (The Key to the Office): Brokers sell direct entry into big companies. They don’t just claim they have it; they show live proof, like screenshots of a company’s VPN portal or their private Azure and AWS cloud dashboards.
- Malware-as-a-Service (MaaS): Cybercriminals can buy a subscription to viruses. These tools, like stealers and loaders, are updated regularly just like legitimate software.
- Log Clouds: These are massive, searchable databases of stealer logs that are collections of usernames and passwords harvested from infected computers worldwide.
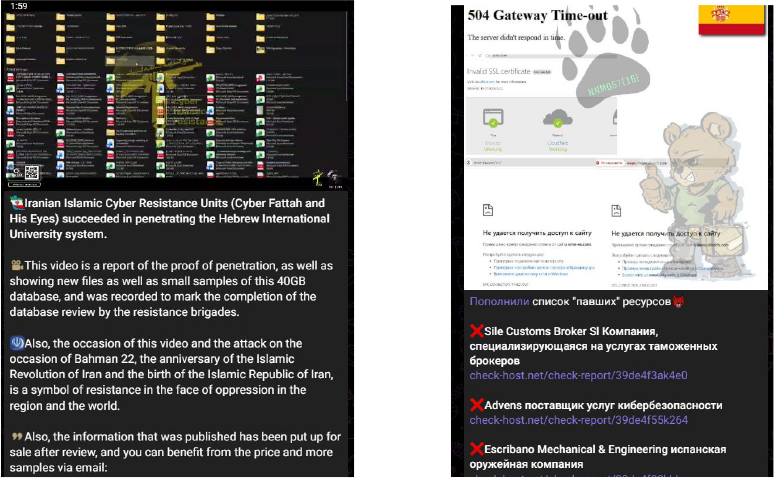
- The Shame Game: Ransomware groups use public channels to bully companies. They post leak countdowns and samples of private files to force a payout.
“For financially motivated actors, Telegram functions as a scalable storefront and customer support hub. For hacktivists, it serves as a mobilization and propaganda amplifier. For state-aligned operations, it offers a rapid distribution channel for narratives and leaks. In many cases, telegram complements and increasingly replaces traditional Tor-based ecosystems by removing technical friction while maintaining operational flexibility,” researchers noted.
It isn’t all about money, though. CYFIRMA researchers found that groups like NoName057 and the Cyber Fattah team use the app to rally digital soldiers. They announce targets for DDoS attacks, where they flood a website with so much junk traffic that it crashes, and then brag about the results instantly.
Telegram has reported a major rise in the amount of user data it shares with law enforcement agencies worldwide. According to transparency data reviewed by researchers and journalists, the platform provided identifying information such as phone numbers and IP addresses to authorities hundreds of times in 2024.
In the United States alone, Telegram fulfilled around 900 law-enforcement requests affecting more than 2,200 users. At the same time, UK authorities received data on 142 cases affecting 293 users, a sharp jump from earlier reporting periods, which showed only single-digit requests.
Despite this increased cooperation with investigators, cybercriminal activity on Telegram continues to expand. This suggests that while data sharing may help investigators track suspects after incidents occur, it has not significantly slowed the growth of cybercrime communities operating on the platform.
Nevertheless, this research is highly concerning because it shows that Telegram has made cybercrime much more professional and accessible, turning a once-hidden underground world into a high-speed, automated industry.