Published On : 2026-05-08

Ransomware In Focus
CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple – industries, geography, and technology, that could be relevant to your organization.
Type: Ransomware
Target Technologies: Windows OS, Local File Systems, Network Shares
Target Geography: USA, Brazil, France, Australia, Italy, Israel, Malaysia
Target Sector: Education, Manufacturing/Engineering, Retail, Logistics, NGO/Nonprofit.
Financial Impact: $10,000 to $80,000
Introduction:
CYFIRMA Research and Advisory Team has found BARADAI Ransomware while monitoring various underground forums as part of our Threat Discovery Process.
BARADAI Ransomware
BARADAI ransomware has been identified as a file-encrypting malware strain that restricts access to victim data by encrypting files and appending a distinct extension associated with the threat, rendering affected files inaccessible. Upon execution, the malware targets a wide range of file types across local systems and potentially accessible network resources, disrupting normal operations. It subsequently deploys a ransom note instructing victims on how to proceed with recovery, typically emphasizing that only the attackers possess the required decryption capability. Analysis of available samples and reporting indicates that the ransomware follows a conventional operational model, focusing on data encryption as the primary impact mechanism rather than incorporating advanced or novel techniques. At present, there is no verified public decryption tool available for BARADAI ransomware, and victims are warned that paying the ransom does not guarantee the successful recovery of encrypted data.
Screenshot: File encrypted by the ransomware (Source: Surface Web)
The ransom note associated with the BARADAI ransomware, commonly dropped after the encryption process, informs victims that their files have been encrypted and are no longer accessible without a unique decryption key controlled by the attackers. The message typically provides instructions for contacting the threat actors, often via email or designated communication channels, and includes a victim-specific identifier to facilitate negotiation. It discourages attempts to restore files using third-party tools or manual modification, warning that such actions could lead to permanent data loss. The note follows a standard coercive structure observed in many ransomware families, emphasizing urgency and exclusivity of the decryption solution while offering limited assurance regarding successful recovery upon payment.
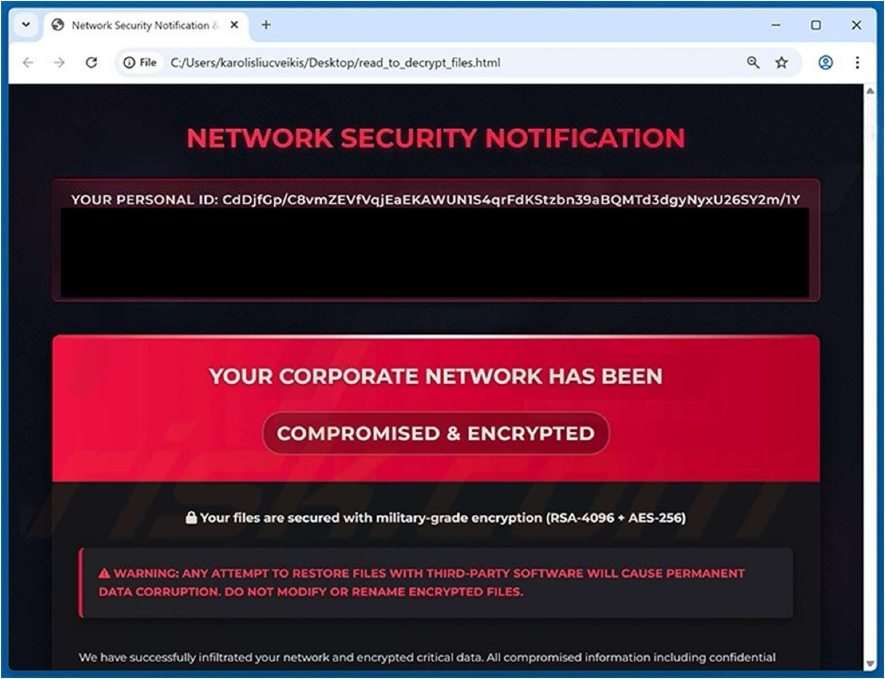
Screenshot: The appearance of the BARADAI’s Ransom Note (Source: Surface Web)
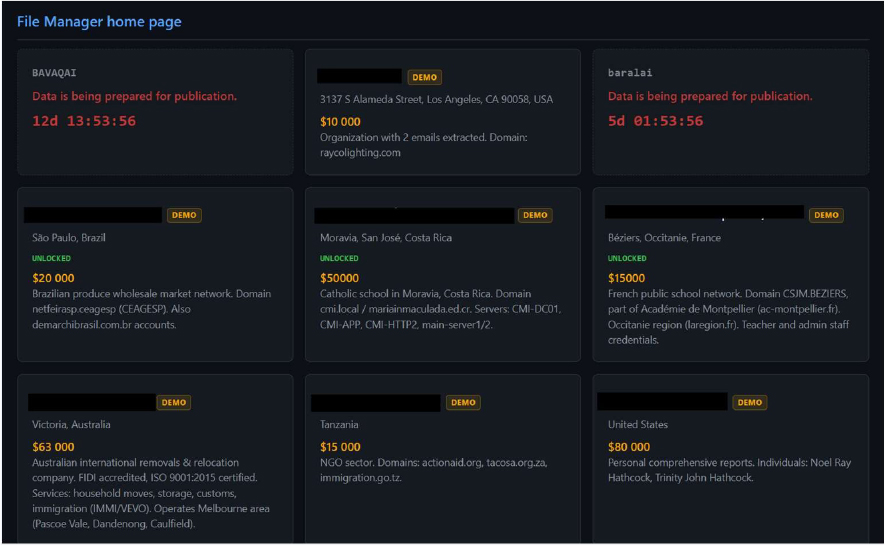
Screenshot: The appearance of BARADAI’s Data Leak site (Source: Surface Web)
Note : BAVACAI Ransomware is also using the same Data Leak Site
The following are the TTPs based on the MITRE Attack Framework
| Tactic | Technique ID | Technique Name |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1129 | Shared Modules |
| Persistence | T1112 | Modify Registry |
| Persistence | T1542 | Pre-OS Boot |
| Persistence | T1542.003 | Pre-OS Boot: Bootkit |
| Persistence | T1547 | Boot or Logon Autostart Execution |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1055 | Process Injection |
| Privilege Escalation | T1134 | Access Token Manipulation |
| Privilege Escalation | T1134.004 | Access Token Manipulation: Parent PID Spoofing |
| Credential Access | T1056 | Input Capture |
| Credential Access | T1056.001 | Input Capture: Keylogging |
| Discovery | T1518 | Software Discovery |
| Discovery | T1614 | System Location Discovery |
| Discovery | T1010 | Application Window Discovery |
| Discovery | T1012 | Query Registry |
| Discovery | T1033 | System Owner/User Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Collection | T1074 | Data Staged |
| Stealth | T1014 | Rootkit |
| Stealth | T1027 | Obfuscated Files or Information |
| Stealth | T1027.002 | Obfuscated Files or Information: Software Packing |
| Stealth | T1027.005 | Obfuscated Files or Information: Indicator Removal from Tools |
| Stealth | T1055 | Process Injection |
| Stealth | T1134 | Access Token Manipulation |
| Stealth | T1134.004 | Access Token Manipulation: Parent PID Spoofing |
| Stealth | T1140 | Deobfuscate/Decode Files or Information |
| Stealth | T1497 | Virtualization/Sandbox Evasion |
| Stealth | T1497.001 | Virtualization/Sandbox Evasion: System Checks |
| Stealth | T1564 | Hide Artifacts |
| Stealth | T1564.003 | Hide Artifacts: Hidden Window |
| Defense Impairment | T1112 | Modify Registry |
| Defense Impairment | T1222 | File and Directory Permissions Modification |
| Command and Control | T1071 | Application Layer Protocol |
| Command and Control | T1105 | Ingress Tool Transfer |
| Command and Control | T1573 | Encrypted Channel |
| Impact | T1486 | Data Encrypted for Impact |
| Impact | T1490 | Inhibit System Recovery |
Relevancy and Insights:
- Persistence: Establishes autorun via CurrentVersionRun registry keys to maintain execution across reboots.
- Configuration Storage: Uses registry paths under HKCUSOFTWARE to store operational or state data.
- Defense Evasion: Interacts with Internet Settings and policy keys, indicating potential security configuration manipulation.
- Execution Control: Leverages cmd.exe for scripted execution of infection and control commands.
- Process Termination: Terminates SQL and related services using taskkill/net stop to unlock files for encryption.
- Service Disruption: Targets enterprise services (e.g., MSSQL) to maximize operational disruption and pressure victims.
- File Encryption Activity: Encrypts files and drops ransom notes (read_to_decrypt_files.html) across directories.
- File Handling Management: Uses Restart Manager keys to manage file locks and ensure encryption success.
- Lateral / Multi-Location Impact: Affects multiple drives and directories, indicating broad file system reach.
- Cleanup / Anti-Forensics: Deletes files and artifacts to hinder recovery and reduce forensic traces.
ETLM Assessment:
CYFIRMA’s analytical assessment suggests that BARADAI ransomware is likely to evolve incrementally within established ransomware tradecraft rather than introducing fundamentally new capabilities. Future activity may focus on improving encryption efficiency, expanding compatibility across file systems, and refining ransom communication to increase payment success rates. There is a plausible likelihood of operators adopting more structured extortion methodologies, potentially incorporating data exfiltration and double extortion tactics, if not already present in future variants. Additionally, threat actors may enhance initial access mechanisms by leveraging common intrusion vectors such as phishing campaigns or exploitation of exposed services, while maintaining an opportunistic targeting strategy. However, based on currently available evidence, there are no confirmed indications of advanced capabilities such as highly targeted intrusions, custom exploit development, or sophisticated evasion frameworks, suggesting near-term evolution will remain aligned with typical commodity ransomware operations.
Sigma rule:
title: Process Creation Using Sysnative Folder tags:
– attack.privilege-escalation
– attack.stealth
– attack.t1055 logsource:
category: process_creation product: windows
detection: selection:
– CommandLine|contains: ‘:WindowsSysnative’
– Image|contains: ‘:WindowsSysnative’ filter_main_ngen:
Image|contains:
– ‘C:WindowsMicrosoft.NETFramework64v’
– ‘C:WindowsMicrosoft.NETFrameworkv’
– ‘C:WindowsMicrosoft.NETFrameworkArmv’
– ‘C:WindowsMicrosoft.NETFrameworkArm64v’ Image|endswith: ‘ngen.exe’ CommandLine|contains: ‘install’
filter_optional_xampp: CommandLine|contains|all:
– ‘”C:Windowssysnativecmd.exe”‘
– ‘xampp’
– ‘catalina_start.bat’
condition: selection and not 1 of filter_main_* and not 1 of filter_optional_* falsepositives:
– Unknown level: medium
(Source: Surface Web)
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
RECOMMENDATIONS
STRATEGIC RECOMMENDATIONS
- Implement competent security protocols and encryption, authentication, or access credentials configurations to access critical systems in your cloud and local environments.
- Ensure that backups of critical systems are maintained, which can be used to restore data in case a need arises.
MANAGEMENT RECOMMENDATIONS
- A data breach prevention plan must be developed considering (a) the type of data being managed by the company; (b) the remediation process; (c) where and how the data is stored; (d) if there is an obligation to notify the local authority.
- Implement a zero-trust security model alongside multifactor authentication (MFA) to reduce the risk of credential compromise.
- Foster a culture of cybersecurity, where you encourage and invest in employee training so that security is an integral part of your organization.
TACTICAL RECOMMENDATIONS
- Update all applications/software regularly with the latest versions and security patches alike.
- Add the Sigma rule for threat detection and monitoring, which will help to detect anomalies in log events, and identify and monitor suspicious activities.
- Establish and implement protective controls by actively monitoring and blocking identified indicators of compromise (IoCs) and reinforcing defensive measures based on the provided tactical intelligence.
Active Malware of the Week
Type: Stealer| Objectives: Data Exfiltration | Target Technology: Windows |
Target Geography: Global
CYFIRMA collects data from various forums based on which the trend is ascertained. We identified a few popular malwares that were found to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the week
This week, “Unix Stealer” is in focus.
Overview of Operation Unix Stealer Malware
The analyzed threat is a credential stealing malware that integrates stealer, trojan, and remote access functionalities within a single infection workflow. Upon execution, it conducts a comprehensive system reconnaissance by enumerating installed applications, running processes, and the operating environment. It proceeds to harvest sensitive information from web browsers, including stored credentials, cookies, browsing history, and certificate data. Additionally, it captures desktop screenshots, extracts the Windows product key, and collects detailed host information to create a complete profile of the compromised system. The acquired data is systematically organized into structured directories before being prepared for exfiltration.
A distinguishing characteristic of this malware is its use of legitimate internet services to disguise malicious network activity. It utilizes public IP lookup APIs to determine the victim’s external network identity and transmits the collected data to attacker-controlled endpoints hosted on trusted platforms. This tactic enables the malware to blend its communications with normal traffic, thereby reducing the likelihood of detection. The malware further conceals its presence by leveraging legitimate Windows components, employing WMI for execution, injecting into system processes, and removing temporary artifacts to minimize forensic evidence.
From a behavioral perspective, the malware demonstrates advanced evasion and anti-analysis techniques. It performs checks to detect debugging or analysis environments, employs obfuscation methods, and creates as well as deletes temporary files to avoid traceability. It also modifies registry entries and service configurations to maintain persistence while remaining covert. By targeting browser credential repositories and system identity information, while operating under the guise of legitimate system activity, the malware achieves effective data exfiltration and sustained persistence, posing a significant threat to both enterprise and individual systems.
Attack Methods
The sample examined demonstrates a coordinated credential-harvesting and host-reconnaissance methodology consistent with contemporary multi-stage information stealers. Upon execution, the payload initiates WMI-based system profiling by querying classes such as Win32_OperatingSystem, Win32_Processor, Win32_VideoController, and Win32_ComputerSystem, while enumerating network interfaces through GetAdaptersAddresses to uniquely fingerprint the host. Multiple anti-analysis safeguards are invoked early, including debugger detection, virtualization checks, and deliberate sleep delays to evade sandbox timing. The malware deploys short-lived binaries within the %TEMP% directory, injects into ephemeral processes, and leverages trusted Windows processes (notably svchost.exe and wmiprvse.exe) to obscure its execution chain and reduce behavioral visibility.
Credential acquisition forms the primary objective of the operation. The stealer systematically navigates Chromium- and Firefox-based browser profile directories, accessing SQLite databases, such as Cookies, History, Web Data, cert9.db, key4.db, and places.sqlite. These artifacts are copied into randomized staging paths under %TEMP% and %PUBLIC%, where file attributes are modified to minimize suspicion. Browser credential repositories, autofill datasets, certificate stores, and session tokens are parsed offline. In parallel, the malware compiles a structured inventory of installed browsers, software, running processes, Windows product keys, user agent strings, and user account metadata into organized text outputs. A live desktop screenshot is also captured and bundled to provide operators with contextual visibility into the compromised environment.
For command-and-control and data exfiltration, the operator employs application-layer communication over reputable platforms instead of dedicated attacker infrastructure. The malware first queries an external IP intelligence service to determine victim geolocation, then exfiltrates the aggregated archive via HTTPS POST requests to a Discord webhook endpoint. By relying on Discord’s trusted TLS profile and content delivery footprint, the traffic blends with legitimate activity and is less likely to trigger basic egress controls. Observed DNS activity, JA3 TLS fingerprints, and SNI metadata support this camouflage approach. Embedded memory strings indicate optional integrations with Telegram APIs and public code repositories, suggesting the capability to pivot communication channels if primary routes are restricted.
Persistence and evasion are strengthened through selective registry modifications, AutoStart execution mechanisms, and trust provider manipulation. Evidence reduction is achieved through self-deletion of temporary artifacts and indicator removal techniques. The malware also inspects registry locations associated with cryptocurrency wallet software, indicating opportunistic targeting beyond browser data. Process injection into transient executables, termination of auxiliary processes, and command-line masquerading under service host contexts collectively diminish forensic traceability. Overall, the attack method reflects a mature stealer architecture focused on credential extraction, environmental intelligence gathering, covert exfiltration through legitimate services, and robust resistance to analysis.
The following are the TTPs based on the MITRE Attack Framework for Enterprise
| Tactic | Technique ID | Technique Name |
| Execution | T1129 | Shared Modules |
| Persistence | T1112 | Modify Registry |
| Persistence | T1543 | Create or Modify System Process |
| Privilege Escalation | T1055 | Process Injection |
| Stealth | T1027 | Obfuscated Files or Information |
| Stealth | T1036 | Masquerading |
| Stealth | T1070 | Indicator Removal |
| Stealth | T1497 | Virtualization/Sandbox Evasion |
| Stealth | T1564 | Hide Artifacts |
| Credential Access | T1003 | OS Credential Dumping |
| Credential Access | T1555 | Credentials from Password Stores |
| Discovery | T1057 | Process Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1518 | Software Discovery |
| Collection | T1005 | Data from Local System |
| Collection | T1119 | Automated Collection |
| Command and control | T1071 | Application Layer Protocol |
| Command and control | T1105 | Ingress Tool Transfer |
| Command and control | T1573 | Encrypted Channel |
| Impact | T1485 | Data Destruction |
INSIGHTS
A key insight from the observed behavior is the malware’s deliberate emphasis on contextual assessment prior to initiating data collection. Rather than immediately extracting information, it first develops an understanding of the host environment, installed software, and user context. This structured progression indicates a preference for informed execution, ensuring that the target system is suitable while minimizing the risk of exposure within monitored or controlled environments.
Another notable aspect is the malware’s ability to operate in a manner that closely resembles legitimate system and user activity. By leveraging trusted system processes, accessing routinely used application data, and communicating through widely recognized online services, its actions align with normal operational patterns. This intentional alignment with expected behavior demonstrates a calculated effort to reduce suspicion and avoid drawing attention during its operation.
Additionally, the nature of the collected artifacts highlights that the objective extends beyond simple credential theft toward assembling a broader representation of the victim’s digital environment. The aggregation of system information, browser data, user details, and visual context suggests an interest in understanding how the system is utilized, rather than focusing solely on isolated secrets. This comprehensive collection approach reflects an effort to construct a detailed operational profile of the compromised host.
ETLM ASSESSMENT
From an ETLM standpoint, the progression of threats that closely mirror routine digital behavior suggests a future in which the boundary between legitimate activity and concealed compromise becomes increasingly indistinct. As organizations continue to adopt cloud services, browser-based workflows, and widely trusted communication platforms for daily operations, these same channels may inadvertently serve as carriers for discreet malicious activity that blends into normal traffic patterns. Employees’ dependence on interconnected applications, saved sessions, and synchronized data across devices may further expand the surface through which such threats can silently observe and collect contextual information. Over time, this convergence between ordinary work practices and covert misuse of trusted systems is likely to create an environment where recognizing subtle irregularities becomes more challenging, shaping a threat landscape in which visibility is reduced not by the absence of evidence, but by the overwhelming presence of seemingly legitimate activity.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems. (Source: Surface Web)
YARA Rules
rule UnixStealer_Family_Detection
meta:
description = “Detection of UnixStealer family using embedded artifacts and hash strings”
author = “CYFIRMA” date = “2026-05-05”
strings:
/* Unique artifact strings */
$a1 = “UnixStealer.txt”
$a2 = “InstalledBrowsers.txt”
$a3 = “UserAgents.txt”
$a4 = “ProductKey.txt”
$a5 = “Screenshot.jpg”
$a6 = “discord.com/api/webhooks/”
$a7 = “ip-api.com/line/?fields=”
$a8 = “cert9.db”
$a9 = “key4.db”
$a10 = “places.sqlite”
/* Hash values as string artifacts */
$h1 = “28ff1dd6d34df59813c8d440e70cad170bd75b9b44a817a2e378d3013122503d” ascii
$h2 = “58165345738044d0f11554f8b8907830c537a1c9f9cb7c7e1015836d73b15f02” ascii
$h3 = “24846cde9f6e334cc47d202040aa01e1fff9104f74b79c28a4a305e241b15377” ascii
condition:
6 of ($a*) or any of ($h*)
Recommendations
Strategic Recommendations
- Establish organization-wide visibility over browser-based workflows, synchronized user data, and use of third-party communication platforms as part of enterprise risk governance.
- Integrate credential protection, data privacy, and endpoint monitoring objectives into long-term security strategies rather than treating them as isolated controls.
- Promote a security culture where routine digital behavior is periodically reviewed for hidden risk exposure, especially where employees rely on saved sessions and local application data.
- Align security policies with the reality that trusted public platforms can be misused as covert communication channels without appearing suspicious.
- Ensure leadership oversight of data handling practices across endpoints, particularly where personal, browser, and system data converge.
Management Recommendations
- Enforce strict policies on browser data storage, password saving practices, and synchronization across personal and organizational devices.
- Monitor the use of external communication services within the organization to understand normal versus abnormal usage patterns.
- Maintain updated inventories of installed software, browsers, and user applications across endpoints to reduce blind spots.
- Encourage periodic user awareness initiatives focused on safe handling of credentials and session data in everyday workflows.
- Coordinate between IT, security teams, and department heads to ensure that endpoint usage patterns are understood in the operational context.
Tactical Recommendations
- Enable monitoring for unusual access to browser profile directories, credential stores, and certificate databases by non-browser processes.
- Track short-lived executables and unexpected activity within temporary directories on endpoints.
- Observe network requests to external IP lookup services and webhook-style communication endpoints from non-standard processes.
- Log and review instances of system tools being invoked in unusual execution contexts.
- Maintain detailed endpoint logs to correlate file access, process activity, and network communication during investigations.
- Implement proactive security controls by monitoring and blocking identified IOCs, leveraging YARA rules for detection, and strengthening defenses based on actionable tactical intelligence.
CYFIRMA’s Weekly Insights
1. Weekly Attack Types and Trends
Key Intelligence Signals:
- Attack Type: Ransomware Attacks, Malware Implant, Spear-Phishing, Vulnerabilities & Exploits, Data Leaks.
- Objective: Unauthorized Access, Data Theft, Data Encryption, Financial Gains, Espionage.
- Business Impact: Data Loss, Financial Loss, Reputational Damage, Loss of Intellectual Property, Operational Disruption.
- Ransomware – Qilin Ransomware, Brain Cipher Ransomware| Malware – UnixStealer
- Qilin Ransomware – One of the ransomware groups.
- Brain Cipher Ransomware – One of the ransomware groups.
Please refer to the trending malware advisory for details on the following: - Malware – UnixStealer
Behavior – Most of these malwares use phishing and social engineering techniques as their initial attack vectors. Apart from these techniques, exploitation of vulnerabilities, defense evasion, and persistence tactics are being observed.
2. Threat Actor in Focus
Silver Fox: Evolution of Multi-Stage Intrusion Capabilities and Backdoor Deployment
- Threat Actor: Silver Fox aka Void Arachne
- Attack Type: Domain Impersonation, Malware Implant, SEO Poisoning, Spear-Phishing, Bring your own device (BYOD), Exploitation of Vulnerabilities, Social Engineering.
- Objective: Monetary Benefits, Cyber espionage, Identity theft, Credential compromise.
- Suspected Target Technology: Sogou AI, Telegram, WPS Office, Youdao, and DeepSeek, Browsers, Social Media (Google Chrome, WatchDog Anti-malware, Windows, Zemana Anti-Malware SDK.
- Suspected Target Geography: Brunei, Cambodia, China, East Timor, Hong Kong, India, Indonesia, Japan, Laos, Malaysia, Myanmar, Philippines, Singapore, Taiwan, Thailand, Vietnam, Russia, South Africa.
- Suspected Target Industries: Critical Infrastructure, Defense, Education, Finance, Government, Manufacturing, Research, Telecommunications, Industrial, Consulting, Retail, Transportation sectors.
- Business Impact: Compromised user accounts, Data Theft, Operational Disruption, Reputational Damage.
About the Threat Actor
The threat actor Silver Fox has been active since at least 2019–2020 and continues to evolve its tooling and targeting strategies, demonstrating an aggressive approach toward organizations. The group has also expanded its operational footprint, extending its activities across multiple countries in the APAC region.
TTPs based on MITRE ATT&CK Framework
| Tactic | ID | Technique |
| Initial Access | T1566.001 | Phishing: Spear phishing Attachment |
| Initial Access | T1566.002 | Phishing: Spear phishing Link |
| Execution | T1204.002 | User Execution: Malicious File |
| Execution | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Execution | T1059.003 | Command and Scripting Interpreter: Windows Command Shell |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Persistence | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Persistence | T1546 | Event Triggered Execution |
| Privilege Escalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Privilege Escalation | T1546 | Event Triggered Execution |
| Stealth | T1497 | Virtualization/Sandbox Evasion |
| Stealth | T1027 | Obfuscated Files or Information |
| Discovery | T1016 | System Network Configuration Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1497 | Virtualization/Sandbox Evasion |
| Collection | T1113 | Screen Capture |
| Collection | T1115 | Clipboard Data |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
| Command and Control | T1105 | Ingress Tool Transfer |
| Exfiltration | T1041 | Exfiltration Over C2 Channel |
Latest Developments Observed
The threat actor is suspected of leveraging the ABCDoor backdoor to target organizations across the industrial, consulting, retail, and transportation sectors in Russia and India. Phishing emails are used as the primary initial access vector, with the apparent objective of gaining unauthorized access and exfiltrating sensitive information.
ETLM Insights
Void Arachne (aka Silver Fox) is a financially motivated cybercriminal threat actor focused on large-scale malware distribution and access monetization.
Operationally, the threat actor demonstrates a structured, deception-driven intrusion model that prioritizes user-driven execution over technical exploitation, enabling scalable compromise while blending into legitimate user behavior.
The threat actor’s operations reflect a deliberate approach:
- Search and Content Manipulation: Using SEO poisoning and themed channels to present malicious installers as legitimate software.
- Software Bundling: Embedding malware within trusted application packages to exploit user intent and reduce suspicion.
- Trend-Based Lures: Aligning delivery with high-interest themes such as AI tools and VPN services to increase engagement.
- Scalable Payload Delivery: Deploying commodity malware to establish access and support data theft or monetization.
Void Arachne is likely to continue refining its content-driven distribution model and expanding the use of AI-enabled lures to enhance scale and effectiveness. This approach sustains its role as a persistent threat, with risks related to widespread malware infections, unauthorized access, and data compromise.
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
YARA Rules
rule SilverFox_ABCDoor_RustSL_ValleyRAT
meta:
description = “Detects Silver Fox (Void Arachne) activity including RustSL loader, ABCDoor, and ValleyRAT artifacts”
author = “CYFIRMA” date = “2026-05-05”
threat_actor = “Silver Fox (Void Arachne)”
strings:
/* RustSL markers */
$rsl1 = “<RSL_START>” ascii
$rsl2 = “<RSL_END>” ascii
$rsl3 = “RSL_STEG_2025_KEY” ascii
/* Debug / persistence */
$dbg1 = “Phantom Persistence Module” ascii
$dbg2 = “RegisterApplicationRestart” ascii
$dbg3 = “Shutdown signal -> Abort shutdown” ascii
/* ABCDoor artifacts */
$abc1 = “AppClientABC” ascii
$abc2 = “appclient” ascii
$abc3 = “pythonw.exe -m appclient” ascii
$abc4 = “HKCU\Software\CarEmu” ascii
$abc5 = “InstallChannel” ascii
$abc6 = “FirstInstallTime” ascii
/* File paths */
$path1 = “\AppData\Local\appclient” ascii
$path2 = “\ProgramData\Tailscale” ascii
$path3 = “applogs\device.log” ascii
$path4 = “exception_logs.zip” ascii
/* Network indicators */
$net1 = “ip-api.com” ascii
$net2 = “ipinfo.io” ascii
$net3 = “ipwho.is” ascii
$net4 = “geoplugin.net” ascii
/* ValleyRAT */
$valley1 = “上线模块.dll” wide
$valley2 = “登录模块.dll” wide
/* Execution */
$cmd1 = “pythonw.exe -m appclient” ascii
$cmd2 = “Invoke-WebRequest” ascii
$cmd3 = “curl.exe -L -o” ascii
condition:
uint16(0) == 0x5A4D and (
(2 of ($rsl*) and 2 of ($abc*)) or
(3 of ($abc*) and 2 of ($path*)) or (2 of ($dbg*) and 1 of ($rsl*)) or
(2 of ($valley*) and 1 of ($cmd*)) or (2 of ($net*) and 2 of ($abc*)) //
)
Recommendations
Strategic Recommendations
- Incorporate Digital Risk Protection (DRP) as part of the overall security posture to proactively defend against impersonations and phishing attacks.
- Assess and deploy alternatives for an advanced endpoint protection solution that provides detection/prevention for malware and malicious activities that do not rely on signature-based detection methods.
- Block exploit-like behaviour. Monitor endpoints memory to find behavioural patterns that are typically exploited, including unusual process handle requests. These patterns are features of most exploits, whether known or new. This will be able to provide effective protection against zero-day/critical exploits and more by identifying such patterns.
Management Recommendations
- Invest in user education and implement standard operating procedures for the handling of financial and sensitive data transactions commonly targeted by impersonation attacks. Reinforce this training with context-aware banners and in-line prompts to help educate users.
- Develop a cyber threat remediation program and encourage employee training to detect anomalies proactively.
Tactical Recommendations
- For better protection coverage against email attacks (like spear phishing, business email compromise, or credential phishing attacks), organizations should augment built-in email security with layers that take a materially different approach to threat detection.
- Protect accounts with multi-factor authentication. Exert caution when opening email attachments or clicking on embedded links supplied via email communications, SMS, or messaging.
- Apply security measures to detect unauthorized activities, protect sensitive production, and process control systems from cyberattacks.
- Add the YARA rules for threat detection and monitoring, which will help to detect anomalies in log events, identify, and monitor suspicious activities
3. Major Geopolitical Developments in Cybersecurity
Iranian Cyber Attacks and Infrastructure Strikes Disrupt Regional Security and Global Supply Chains
A pro-Iranian hacking collective, identified by researchers as an arm of the Iranian Ministry of Intelligence, claims to have exfiltrated and leaked sensitive personal data belonging to over 2,300 American service members stationed in the Persian Gulf. The stolen information reportedly includes home addresses, family details, shopping history, and daily activities. Cybersecurity experts and former high-ranking intelligence officials suggest that this activity follows a pattern of opportunistic targeting rather than sophisticated strategic planning. Researchers liken the current state of these regional cyber capabilities to that of criminal organizations that seize low-hanging fruit and then launch aggressive information operations to exaggerate the scale and impact of the breach.
Simultaneously, regional conflict is causing significant tremors in the global electronics supply chain. Recent kinetic strikes against a major petrochemical complex have halted the production of high-purity polyphenylene ether (PPE) resin. Because this single facility accounts for approximately 70% of the world’s supply of this specific resin – a critical component for printed circuit board laminates – the disruption has led to surging prices for raw materials like epoxy resin, glass fiber, and copper foil, while significantly lengthening lead times for essential hardware. Global manufacturers are currently facing severe inventory shortages and are unable to source the materials necessary to maintain standard production cycles for essential circuit boards.
ETLM Assessment:
The current crisis in Iran shows no signs of a swift resolution, as the cycle of kinetic and digital warfare continues to escalate following the massive joint strikes launched in early 2026. With diplomatic negotiations stalled and regional tensions at a breaking point, additional military strikes by the United States appear increasingly probable as a means to degrade the regime’s nuclear and military infrastructure. In direct response to these pressures, Iranian-aligned cyber actors – specifically state-sponsored groups operating under the guise of hacktivist personas – are expected to intensify their retaliatory campaigns. These operations will likely transition from opportunistic data leaks and disinformation to more aggressive, destructive attacks targeting critical Western infrastructure and military logistics, aiming to project power and exact a high economic and psychological cost on their adversaries.
Cyber Espionage Targets Diplomatic Communications Amid Regional Tensions
Chinese state-sponsored actors successfully breached the Cuban embassy in Washington, D.C., monitoring the communications of dozens of diplomats during a period of heightened geopolitical friction and a potential naval blockade. The intrusion, which began earlier this year, compromised the email accounts of nearly 70 officials, including high-ranking diplomatic leadership. This campaign occurred alongside significant regional instability, including military actions in neighboring territories and severe energy shortages caused by halted oil deliveries.
The attackers gained access by exploiting two vulnerabilities in outdated email server software that had remained unpatched for five years. Once the security was bypassed, the intruders exfiltrated the entire contents of inboxes belonging to political and intelligence personnel.
This breach reflects a growing trend where state-level actors utilize aging software flaws to conduct mass exploitation, allowing them to gather intelligence on global events in real-time. In a separate but concurrent operation, the same group exploited a vulnerability in a widely used web development framework to compromise 5,000 servers globally within days of the flaw being identified.
Additional monitoring revealed that the same hacking collective targeted several other foreign ministries and government bodies in the region using infrastructure and techniques consistently linked to specific state-sponsored espionage groups. While much of the activity was highly targeted, researchers noted that the group also engaged in opportunistic theft, hitting a wide range of public and private servers, including health services and investment firms.
Experts warn that the rapid exploitation of publicly known vulnerabilities is expected to accelerate as adversaries integrate artificial intelligence into their operations. Modern AI models are now capable of autonomously identifying and leveraging these flaws at a speed and scale previously unseen. While some organizations are being encouraged to use these same AI tools to find and fix weaknesses defensively, the persistent reliance on legacy software remains a primary entry point for sophisticated actors.
ETLM Assessment:
Despite the ideological alignment and historic partnership between Beijing and Havana, China’s decision to breach Cuban diplomatic communications likely stems from a need for unfiltered intelligence during a volatile period of regional instability. In the world of high-stakes espionage, “friendly” states are often targeted because their internal deliberations provide a candid, unvarnished window into the intentions of mutual adversaries – in this case, the United States. By monitoring Cuban diplomats as they navigated a U.S. naval blockade and regional energy crises, China could gain real-time insights into U.S. back-channel negotiations and Caribbean contingency plans that Havana might not fully share. Ultimately, for a global power like China, the strategic necessity of avoiding geopolitical surprises outweighs the diplomatic risk of spying on an ally.
4. Rise in Malware/Ransomware and Phishing
Qilin Ransomware Impacts Tokyo Hoso Kogyo Corporation
- Attack Type: Ransomware
- Target Industry: Construction
- Target Geography: Japan
- Ransomware: Qilin Ransomware
- Objective: Data Theft, Data Encryption, Financial Gains
- Business Impact: Financial Loss, Data Loss, Reputational Damage
Summary:
CYFIRMA observed in an underground forum that a company from Japan, Tokyo Hoso Kogyo Corporation (https[:]//www[.]tokyohoso[.]co[.]jp/), was compromised by Qilin Ransomware. Tokyo Hoso Kogyo Co., Ltd. is a Japanese construction and civil engineering company specializing in road construction, pavement technologies, and infrastructure development. The compromised data consists of confidential and sensitive information related to the organization. The total size of the compromised data is approximately 30 GB.
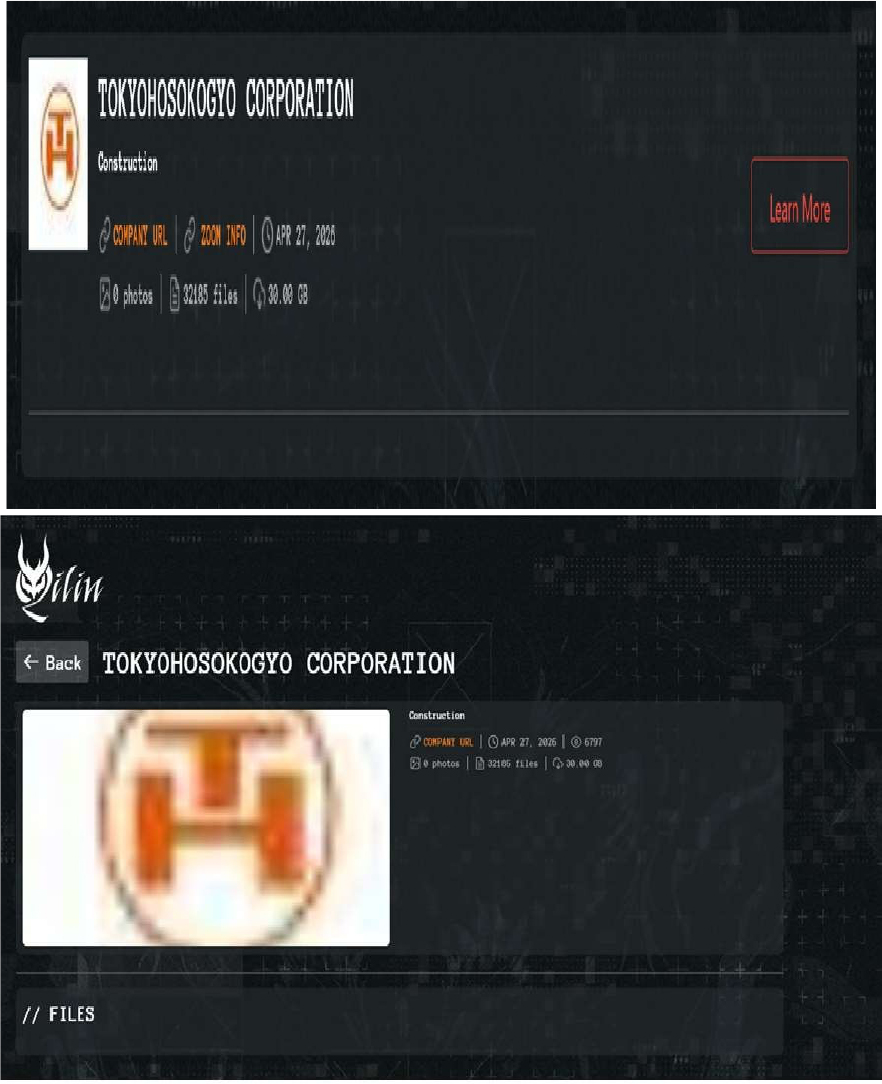
Source: Dark Web
Relevancy & Insights:
- The Qilin Ransomware group operates a Ransomware-as-a-Service (RaaS) model, allowing affiliates to carry out attacks while Qilin provides infrastructure and malware tools.
- The Qilin Ransomware group primarily targets countries such as the United States of America, Canada, France, the United Kingdom, and Italy.
- The Qilin Ransomware group primarily targets industries, including Manufacturing, Professional Goods & Services, Consumer Goods & Services, Healthcare, and Information Technology.
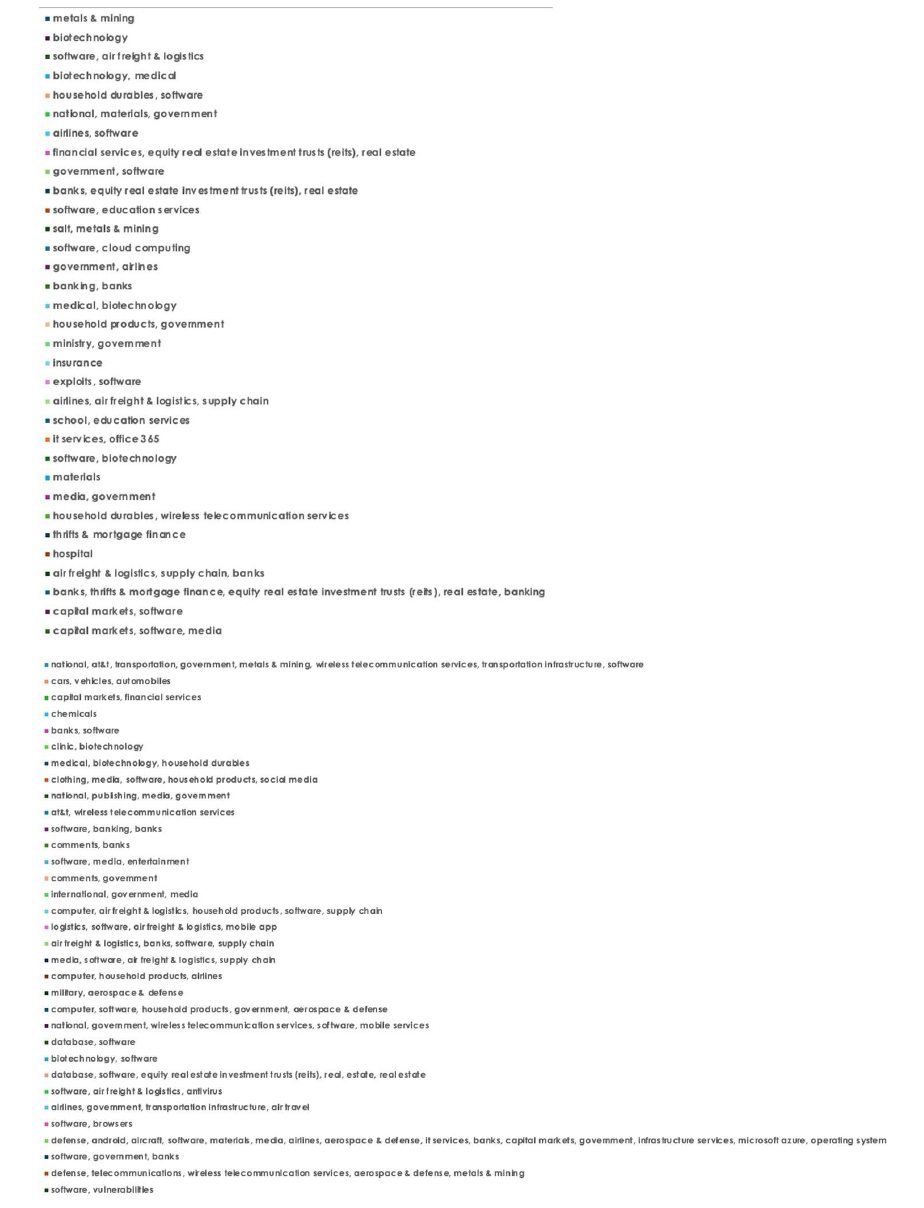
- Based on the Qilin Ransomware victims list from 1st Jan 2025 to 05th May 2026, the top 5 Target Countries are as follows:
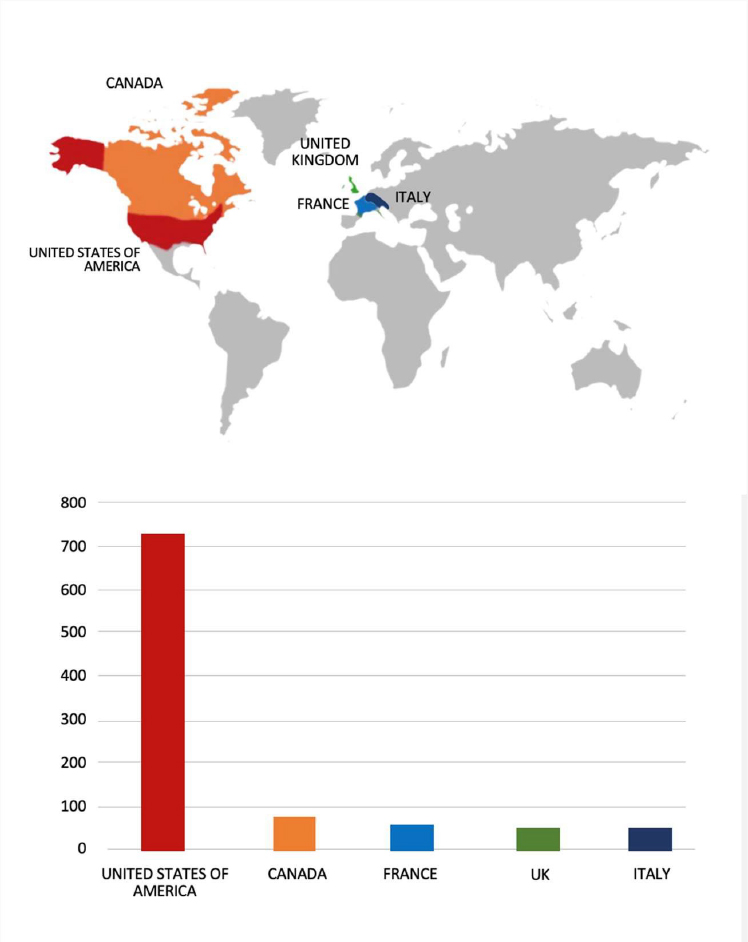
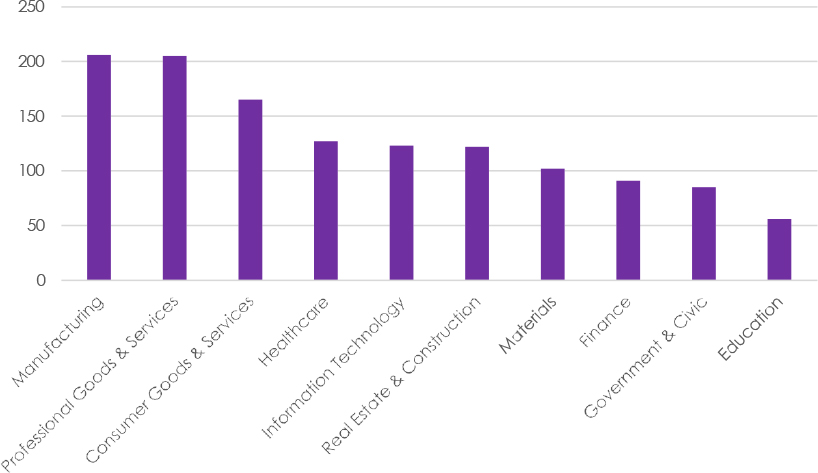
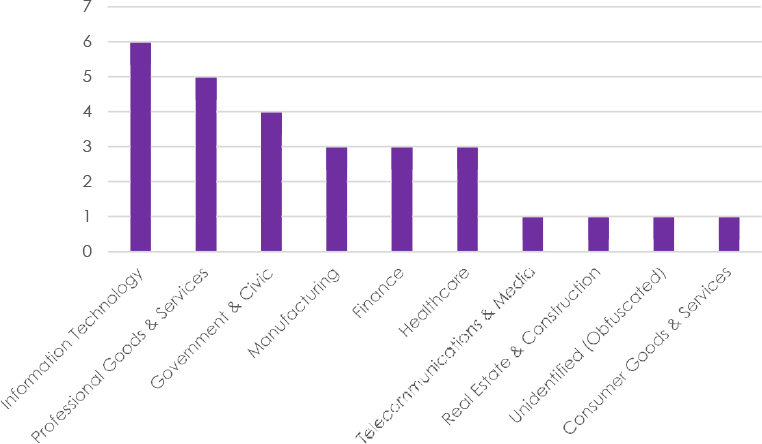
- The Top 10 Industries most affected by the Qilin Ransomware victims list from 1st Jan 2025 to 05th May 2026 are as follows:
ETLM Assessment:
According to CYFIRMA’s assessment, Qilin ransomware poses a significant threat to organizations of all sizes. Its evolving tactics, including double extortion (data encryption and leak threats), cross-platform capabilities (Windows and Linux, including VMware ESXi), and a focus on speed and evasion, make it a particularly dangerous actor.
Brain Cipher Ransomware Impacts Kisnet Co., Ltd
- Attack Type: Ransomware
- Target Industry: Telecommunications, Information Technology (IT) Services
- Target Geography: Japan
- Ransomware: Brain Cipher Ransomware
- Objective: Data Theft, Data Encryption, Financial Gains
- Business Impact: Financial Loss, Data Loss, Reputational Damage
Summary:
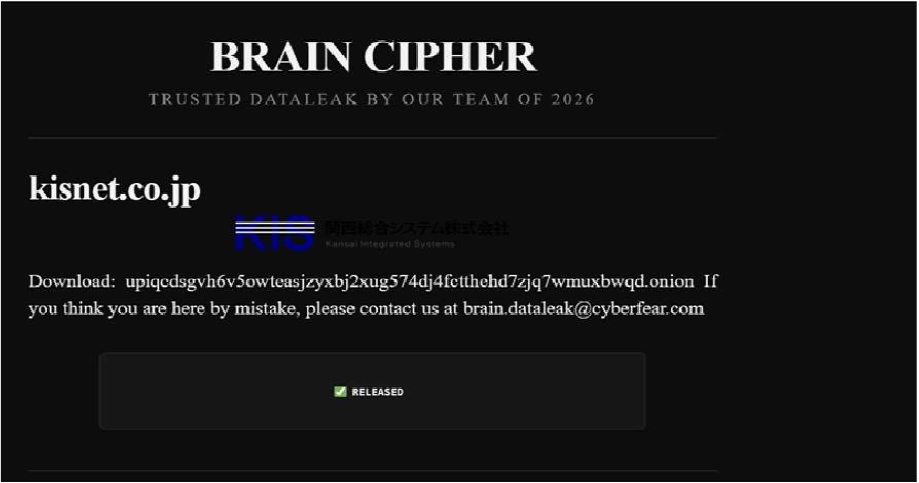
CYFIRMA observed in an underground forum that a company from Japan, Kisnet Co., Ltd (https[:]//kismet[.]co.jp/), was compromised by Brain Cipher Ransomware. Kisnet Co., Ltd., a Japanese internet service provider based in Japan. It operates in the telecommunications and ISP sector, offering broadband and network connectivity services to residential and business customers. The compromised data consists of confidential and sensitive information related to the organization.
Source: Dark Web
Relevancy & Insights:
- Brain Cipher ransomware was first identified in June 2024. It employs a double-extortion model, where attackers not only encrypt files but also threaten to leak stolen data if the ransom is not paid.
- Brain Cipher ransomware uses strong AES-256 encryption combined with RSA-2048 to secure encryption keys, making file recovery without the key nearly impossible.
- The Brain Cipher Ransomware group primarily targets countries such as Canada, the United States of America, Spain, France, and the United Arab Emirates.
- The Brain Cipher Ransomware group primarily targets industries such as Information Technology, Professional Goods & Services, Government & Civic, Manufacturing, and Finance.
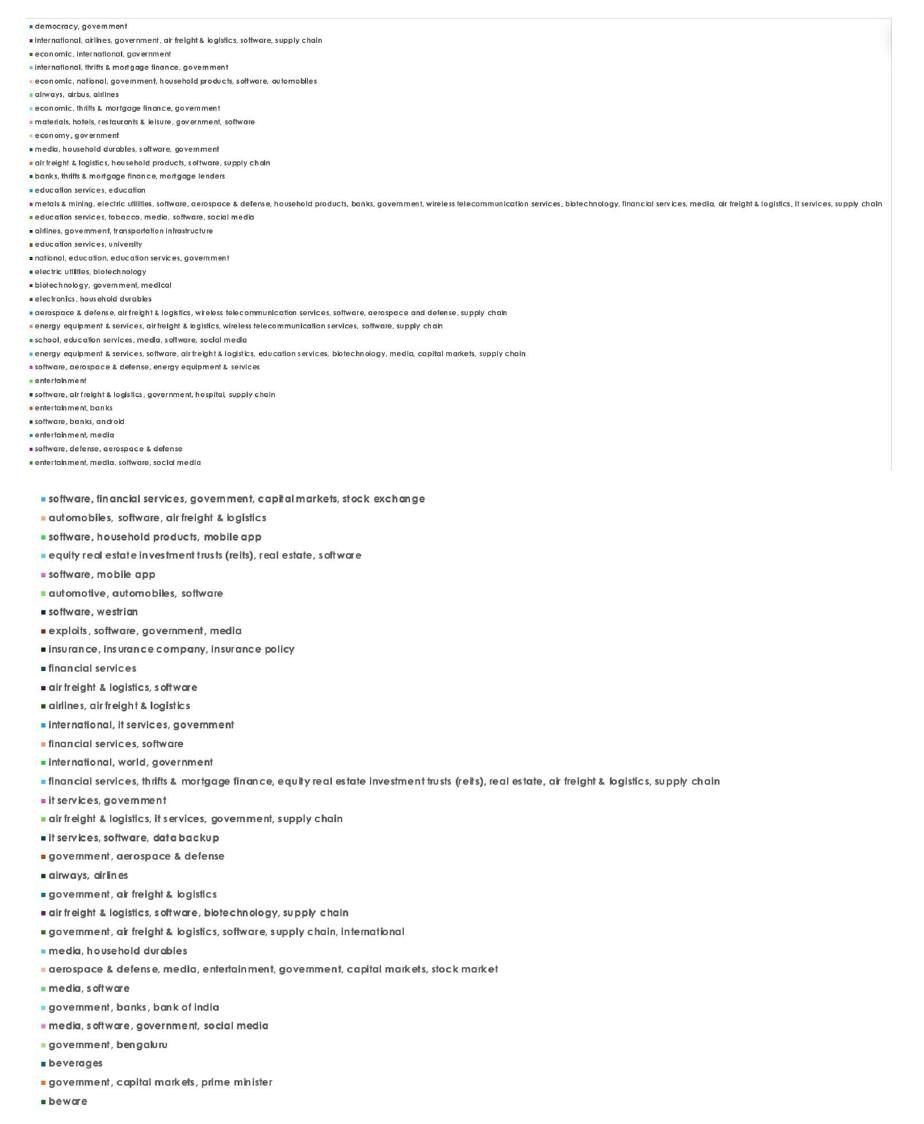
- Based on the Brain Cipher Ransomware victims list from 1st Jan 2025 to 05th May 2026, the top 5 Target Countries are as follows:
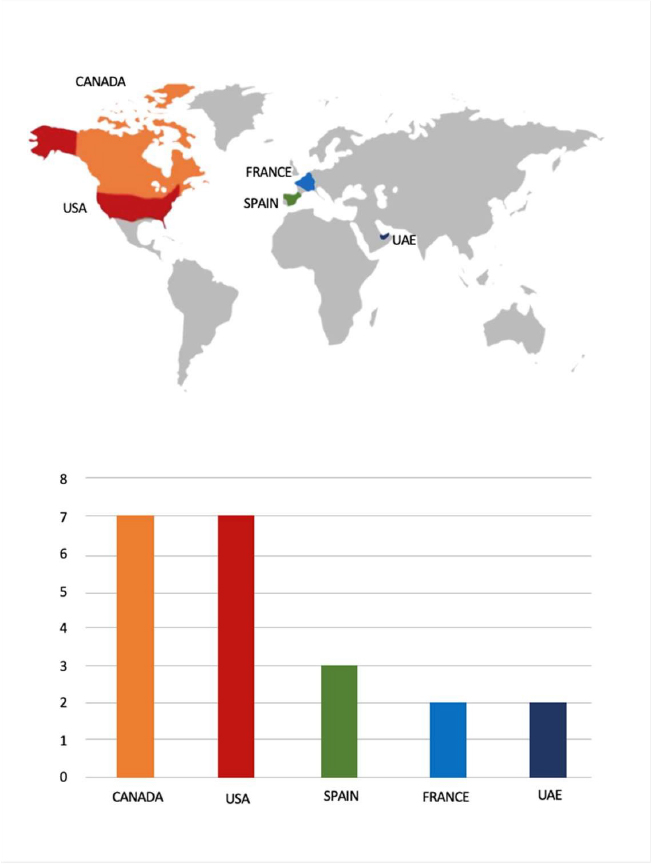
- The Top 10 Industries most affected by the Brain Cipher Ransomware victims list from 1st Jan 2025 to 05th May 2026 are as follows:
ETLM Assessment:
According to CYFIRMA’s assessment, Brain Cipher Ransomware represents a growing threat in the cybersecurity landscape, particularly due to its focus on critical infrastructure and government entities. Organizations must enhance their cybersecurity measures, including robust incident response plans and employee training on recognizing phishing attempts, to mitigate risks associated with this evolving threat. Continuous monitoring and updating of security protocols are essential to defend against such sophisticated attacks.
5. Vulnerabilities and Exploits
Vulnerability in MOVEit Automation
- Attack Type: Vulnerabilities & Exploits
- Target Technology: Managed File Transfer / Enterprise Automation
- Vulnerability: CVE-2026-4670
- CVSS Base Score: 9.8 Source
- Vulnerability Type: Improper Authentication
- Summary: The vulnerability allows a remote attacker to bypass authentication.
Relevancy & Insights:
The vulnerability exists due to authentication bypass in the service backend command port interfaces when handling requests.
Impact:
A remote attacker can send crafted requests to bypass authentication.
Affected Products:
https[:]//community[.]progress[.]com/s/article/MOVEit-Automation-Critical-Security-Alert-Bulletin-April-2026-CVE-2026-4670-CVE-2026-5174
Recommendations:
Monitoring and Detection: Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
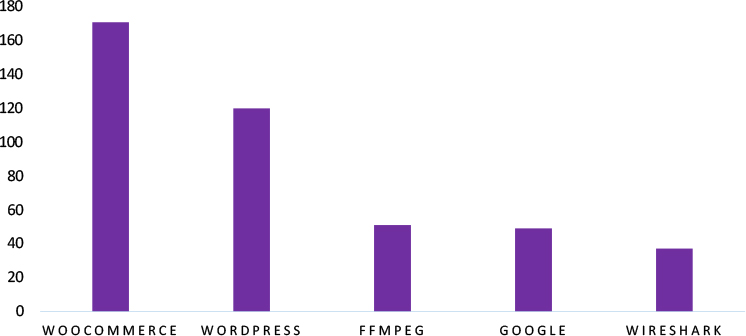
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies due to a range of vulnerabilities. The following are the top 5 most affected technologies.
ETLM Assessment
Vulnerability in MOVEit Automation introduces significant risks to enterprise file transfer and automation infrastructures that rely on secure and automated data exchange. As MOVEit Automation is widely used for handling sensitive data transfers and business workflows, exploitation of this vulnerability could allow unauthorized access to critical systems and disrupt automated operations. Organizations leveraging managed file transfer solutions must ensure timely patching, secure configuration, and continuous monitoring to prevent potential compromise. Addressing this vulnerability is essential to maintaining the integrity, availability, and security of enterprise data transfer and automation environments.
6. Latest Cyber-Attacks, Incidents, and Breaches
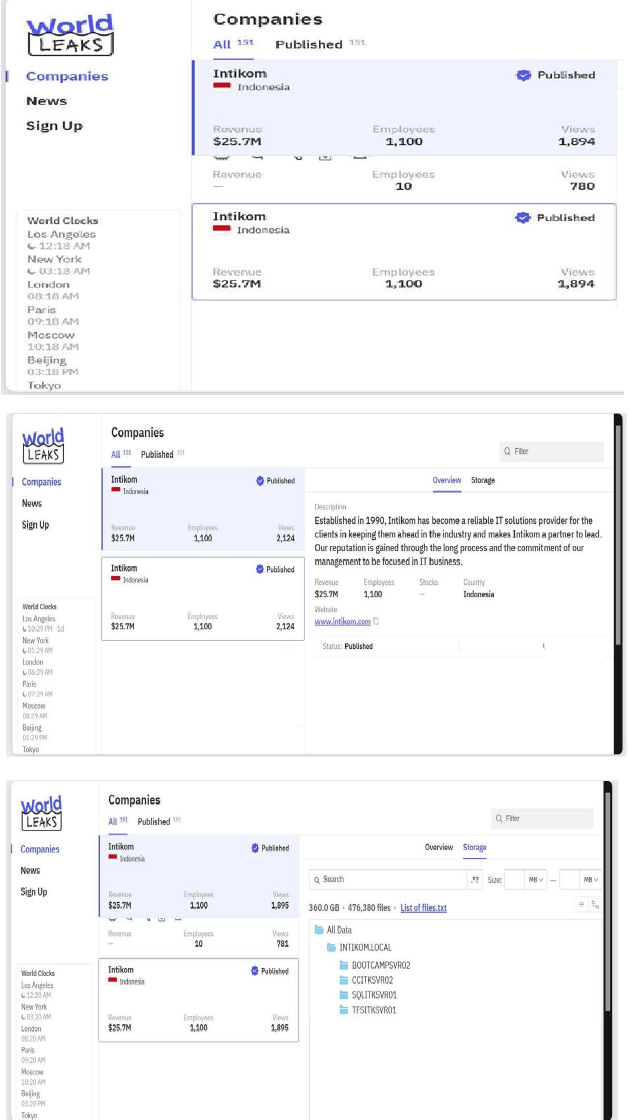
World Leaks Ransomware attacked and published the data of Intikom
- Threat Actor: World Leaks Ransomware
- Attack Type: Ransomware
- Objective: Data Leak, Financial Gains
- Target Technology: Web Applications
- Target Industry: Information Technology Services (IT Services & IT Consulting)
- Target Geography: Indonesia
- Business Impact: Operational Disruption, Data Loss, Financial Loss, Potential Reputational Damage
Summary:
Recently, we observed that World Leaks Ransomware attacked and published the data of Intikom (https[:]//www[.]intikom[.]com/) on its dark web website. Intikom is an Indonesian information technology company that provides IT solutions and services primarily to the banking and financial sector. The company offers system integration, software development, infrastructure management, and managed services. Headquartered in Jakarta, Indonesia, Intikom has been a long-standing technology partner for major Indonesian banks, supporting digital transformation and core banking operations across the country. The image indicates that a significant volume of internal organizational data has been compromised, totaling approximately 360 GB across 476,380 files. The exposed data appears to originate from a corporate network domain labeled INTIKOM.LOCAL, and includes structured data stored across multiple servers, such as BOOTCAMPSVR02, CCITKSVR02, SQLITKSVR01, and TFSITKSVR01. This suggests the breach likely involves a mix of internal documents, databases, project files, source code repositories, and possibly enterprise application data, which may contain sensitive business information, operational records, and potential confidential client or employee-related data.
Source: Dark Web
Relevancy & Insights:
- World Leaks Ransomware group emerged in January 2025 as a rebrand of the Hunters International ransomware operation, shifting its focus from file encryption to solely stealing sensitive data and threatening to leak it unless a ransom is paid.
- The World Leaks ransomware group primarily targets industries, including Healthcare, Manufacturing, Professional Goods & Services, Information Technology, and Real Estate & Construction.
ETLM Assessment:
According to CYFIRMA’s assessment, World Leaks Ransomware represents an emerging and adaptive threat within the cybersecurity landscape, particularly due to its focus on data exfiltration, double-extortion tactics, and targeting of organizations across multiple sectors. The group leverages sophisticated intrusion techniques and publicly exposes stolen data to increase pressure on victims, amplifying both financial and reputational damage. Organizations must strengthen their cybersecurity posture by implementing robust incident response strategies, enforcing strict access controls, and enhancing employee awareness to detect phishing and social engineering attempts. Continuous monitoring, timely patch management, and proactive threat intelligence are critical to mitigating risks and defending against the evolving tactics employed by World Leaks Ransomware.
7. Data Leaks
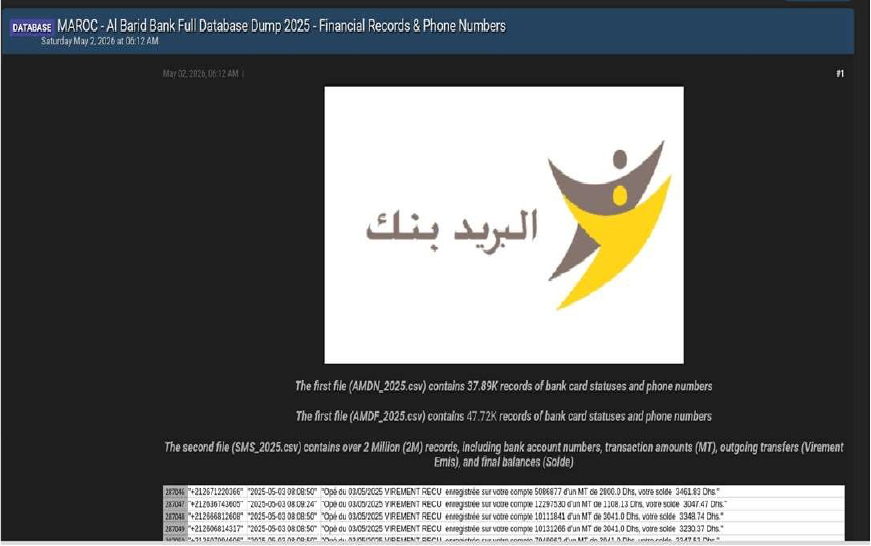
Al Barid Bank Data Advertised on a Leak Site
- Attack Type: Data leak
- Target Industry: Finance
- Target Geography: Morocco
- Objective: Financial Gains
- Business Impact: Data Loss, Reputational Damage
Summary:
The CYFIRMA research team identified a post on a dark web forum by a threat actor using the alias “Sejji,” advertising the sale of an allegedly compromised dataset associated with Al Barid Bank, a Morocco-based financial institution. In the post, the actor claims to have obtained a full database dump containing sensitive financial and customer-related records. The listing suggests that the dataset is recent (labeled 2025) and includes multiple structured files with large volumes of data, indicating a potentially significant breach affecting banking operations and customer information.
According to the threat actor, the leaked dataset is organized into multiple CSV files, each containing different categories of financial and personal data. The actor highlights specific files and their contents, suggesting a high level of access to internal banking systems or associated services. Sample records shared in the post appear to include transaction-related SMS logs and account activity details, reinforcing the credibility of the claim.
Based on the actor’s description, the compromised dataset includes:
- Bank card status records linked with customer phone numbers
- Customer contact information, including mobile numbers
- Large-scale SMS logs containing transactional notifications
- Bank account numbers associated with customers
- Financial transaction details, including transaction amounts (MT)
- Outgoing transfer records (e.g., “Virement Emis”)
- Account balance information following transactions
- Time-stamped transaction activity and notification logs
The actor claims that the dataset is split into multiple files, including:
- “AMDN_2025.csv”, containing approximately 37.89K records of card status and phone numbers
- “AMDF_2025.csv”, containing approximately 47.72K similar records
- “SMS_2025.csv”, containing over 2 million records with detailed financial transaction data and account activity
The presence of SMS-based transaction logs is particularly concerning, as these messages often include sensitive financial details, such as account numbers, transfer confirmations, and updated balances. Exposure of such data could enable fraud, targeted phishing attacks, and unauthorized financial activities.
This incident indicates a potentially severe breach involving highly sensitive financial and personal data. If validated, the leak could pose serious risks to affected customers, including financial fraud, identity theft, and privacy violations. Additionally, the scale and nature of the data suggest broader implications for banking security and regulatory compliance, potentially impacting trust in the institution and the wider financial ecosystem.
The authenticity of this Access sale remains unverified at the time of reporting, as the claim originates solely from the threat actor.
Source: Underground Forums
Agoda Data Advertised on a Leak Site
- Attack Type: Data leak
- Target Industry: Travel & Tourism
- Target Geography: Malaysia
- Objective: Data Theft, Financial Gains
- Business Impact: Data Loss, Reputational Damage
Summary: The CYFIRMA research team identified a post on a dark web forum by a threat actor using the alias “Hackboy,” advertising the sale of an allegedly compromised dataset related to Agoda, a global digital travel service provider. In the post, the actor claims to have exposed a massive database containing approximately 82 million customer records, reportedly linked to users from Malaysia. The listing suggests that the dataset originates from Agoda’s platform, which provides hotel bookings, flights, and travel-related services across a global network. According to the threat actor, the leaked data is structured in JSON format and includes multiple personally identifiable information (PII) fields. The actor also indicates that a middleman or escrow service is accepted for transactions and provides a Telegram contact for negotiation, suggesting the intent to monetize the dataset. Sample records shared in the post appear to validate the structure and type of data being offered, showing detailed customer entries.
Based on the actor’s description, the compromised dataset allegedly includes:
- Full names of customers
- Email addresses
- Phone numbers
- National identification numbers (IC numbers)
- Raw residential address details
- Source-related metadata (e.g., booking or platform origin)
- Extraction timestamps indicating when the data was obtained
- Status fields (e.g., verification or activity status)
The actor claims that the dataset consists of approximately 82 million records, making it a large-scale data exposure. The inclusion of sensitive identifiers such as national ID numbers and detailed addresses significantly increases the potential risk of identity theft, fraud, and targeted social engineering attacks.
At the time of reporting, the authenticity of the breach remains unverified, as the claims are based solely on the threat actor’s post. However, if validated, this incident could represent a major data exposure impacting millions of users, with serious privacy, financial, and reputational implications for both the affected individuals and the organization involved.
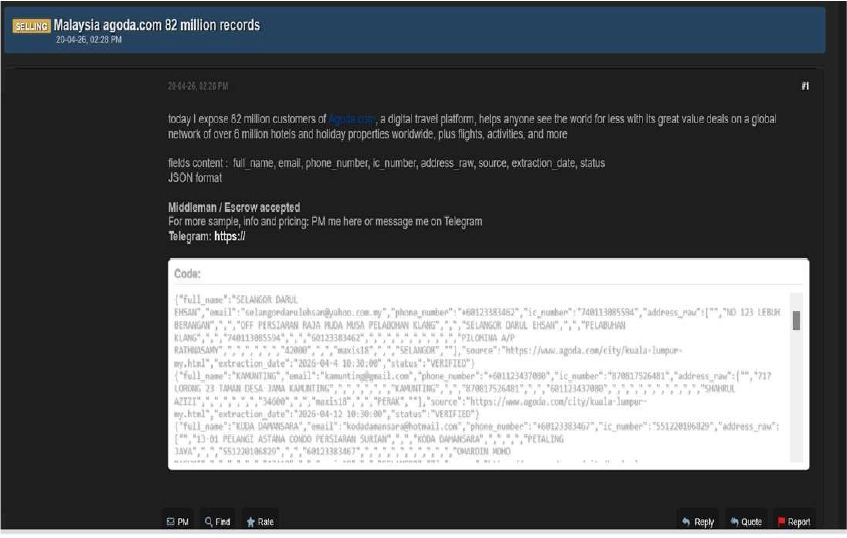
Source: Underground Forums
Relevancy & Insights:
Financially motivated cybercriminals are continuously looking for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to gain access and steal valuable data. Subsequently, the stolen data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor “Hackboy” is assessed as an active and capable entity primarily engaged in data-leak operations, with multiple credible indications linking them to incidents involving unauthorized system access and the dissemination or sale of stolen data on dark web forums. These activities underscore the growing sophistication of cyber threats driven by organized underground networks and highlight the urgent need for organizations to enhance their cybersecurity posture through continuous monitoring, improved threat intelligence, and proactive defensive measures to protect sensitive information and critical infrastructure.
Recommendations: Enhance the cybersecurity posture by:
- Updating all software products to their latest versions is essential to mitigate the risk of vulnerabilities being exploited.
- Ensure proper database configuration to mitigate the risk of database-related attacks.
- Establish robust password management policies, incorporating multi-factor authentication and role-based access to fortify credential security and prevent unauthorized access.
8. Other Observations
The CYFIRMA research team identified a post on a dark web forum by a threat actor using the alias “Anonymous2090,” advertising a free leak of data allegedly obtained from the UAE-based website tyleia[.]ae. In the forum post, the actor claims that the target website was fully compromised, with its databases extracted, complete source code stolen, and the WordPress administrative control panel disrupted. The actor further states that the website was subsequently taken offline following the breach, indicating a potentially destructive impact on the organization’s digital infrastructure.
According to the details shared in the post, the threat actor has made the dataset publicly accessible via a downloadable archive and provided a password for access. The actor claims that the database size is approximately 89.5 MB after decompression. Sample data included in the post suggests that the leaked information is structured and originates from backend database tables such as “information_schema” and “public,” indicating exposure of core database architecture and content.
Based on the previewed records, the compromised dataset appears to include sensitive user and administrative information, which may enable further exploitation if misused. The exposed data includes:
- User account details such as user IDs, usernames, and display names
- Email addresses associated with user and admin accounts
- Hashed passwords and authentication-related fields (e.g., activation keys)
- User roles and privileges, including administrative-level access indicators
- Registration timestamps and account status information
- Metadata entries containing configuration details and user preferences
- WordPress-related settings and backend configuration data
- Possible API keys, tokens, or integration-related information within database fields
Additionally, the presence of administrative records and backend configuration data suggests that the breach extends beyond standard user information and may include privileged access components. The exposure of such data could facilitate account takeovers, privilege escalation, or further compromise of associated systems.
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
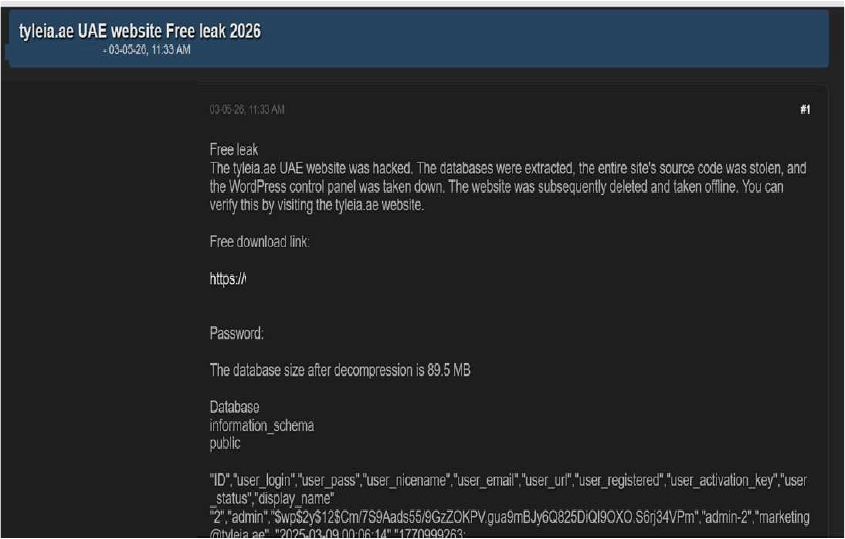
Source: Underground Forums
RECOMMENDATIONS
STRATEGIC RECOMMENDATIONS
- Attack Surface Management should be adopted by organisations, ensuring that a continuous closed-loop process is created between attack surface monitoring and security testing.
- Deploy a unified threat management strategy – including malware detection, deep learning neural networks, and anti-exploit technology – combined with vulnerability and risk mitigation processes.
- Incorporate Digital Risk Protection (DRP) in the overall security posture that acts as a proactive defence against external threats targeting unsuspecting customers.
- Implement a holistic security strategy that includes controls for attack surface reduction, effective patch management, and active network monitoring, through next-generation security solutions and a ready-to-go incident response plan.
- Create risk-based vulnerability management with deep knowledge about each asset. Assign a triaged risk score based on the type of vulnerability and criticality of the asset to help ensure that the most severe and dangerous vulnerabilities are dealt with first.
MANAGEMENT RECOMMENDATIONS
- Take advantage of global Cyber Intelligence, providing valuable insights on threat actor activity, detection, and mitigation techniques.
- Proactively monitor the effectiveness of risk-based information security strategy, the security controls applied, and the proper implementation of security technologies, followed by corrective actions, remediations, and lessons learned.
- Consider implementing Network Traffic Analysis (NTA) and Network Detection and Response (NDR) security systems to compensate for the shortcomings of EDR and SIEM solutions.
- Ensure that detection processes are tested to ensure awareness of anomalous events. Timely communication of anomalies should be continuously evolved to keep up with refined ransomware threats.
TACTICAL RECOMMENDATIONS
- Patch software/applications as soon as updates are available. Where feasible, automated remediation should be deployed since vulnerabilities are one of the top attack vectors.
- Consider using security automation to speed up threat detection, improved incident response, increased visibility of security metrics, and rapid execution of security checklists.
- Build and undertake safeguarding measures by monitoring/ blocking the IOCs and strengthening defences based on the tactical intelligence provided.
- Deploy detection technologies that are behavioral anomaly-based to detect ransomware attacks and help to take appropriate measures.
- Implement a combination of security controls, such as reCAPTCHA (completely Automated Public Turing test to tell Computers and Humans Apart), Device fingerprinting, IP backlisting, Rate-limiting, and Account lockout to thwart automated brute-force attacks.
- Ensure email and web content filtering uses real-time blocklists, reputation services, and other similar mechanisms to avoid accepting content from known and potentially malicious sources.
Situational Awareness – Cyber News
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
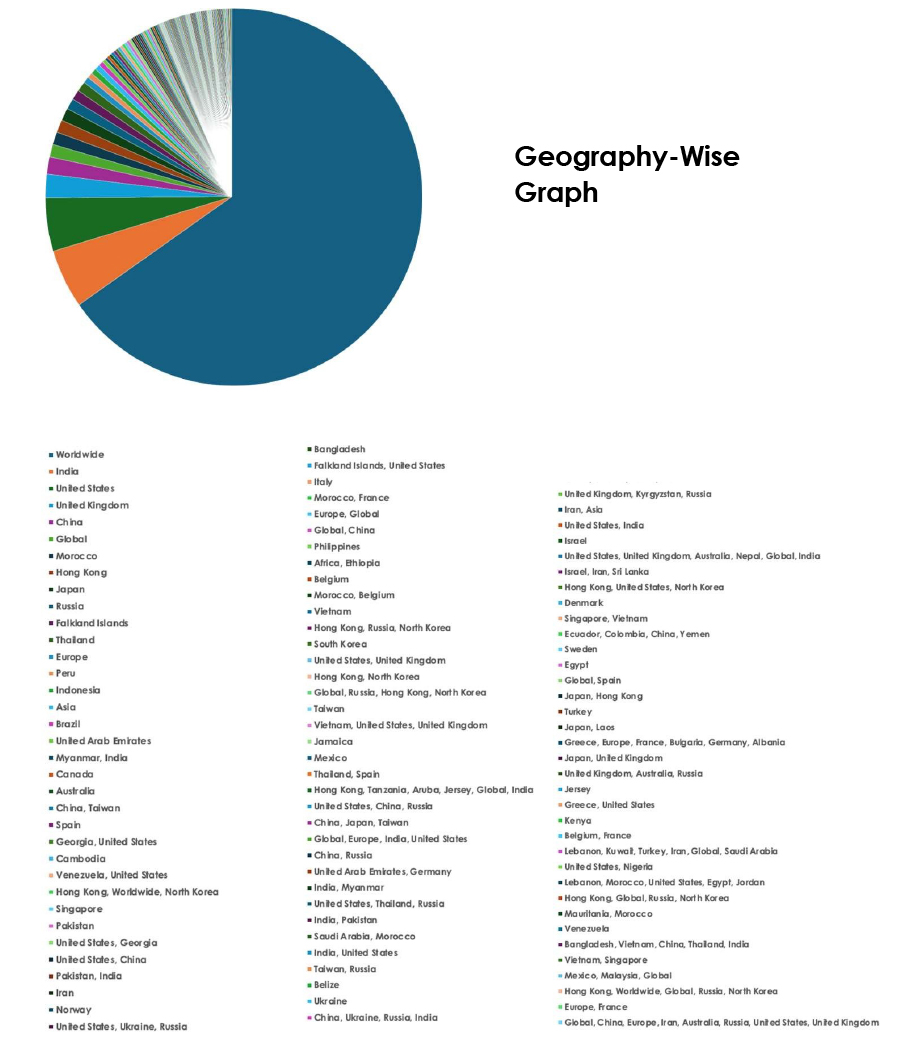
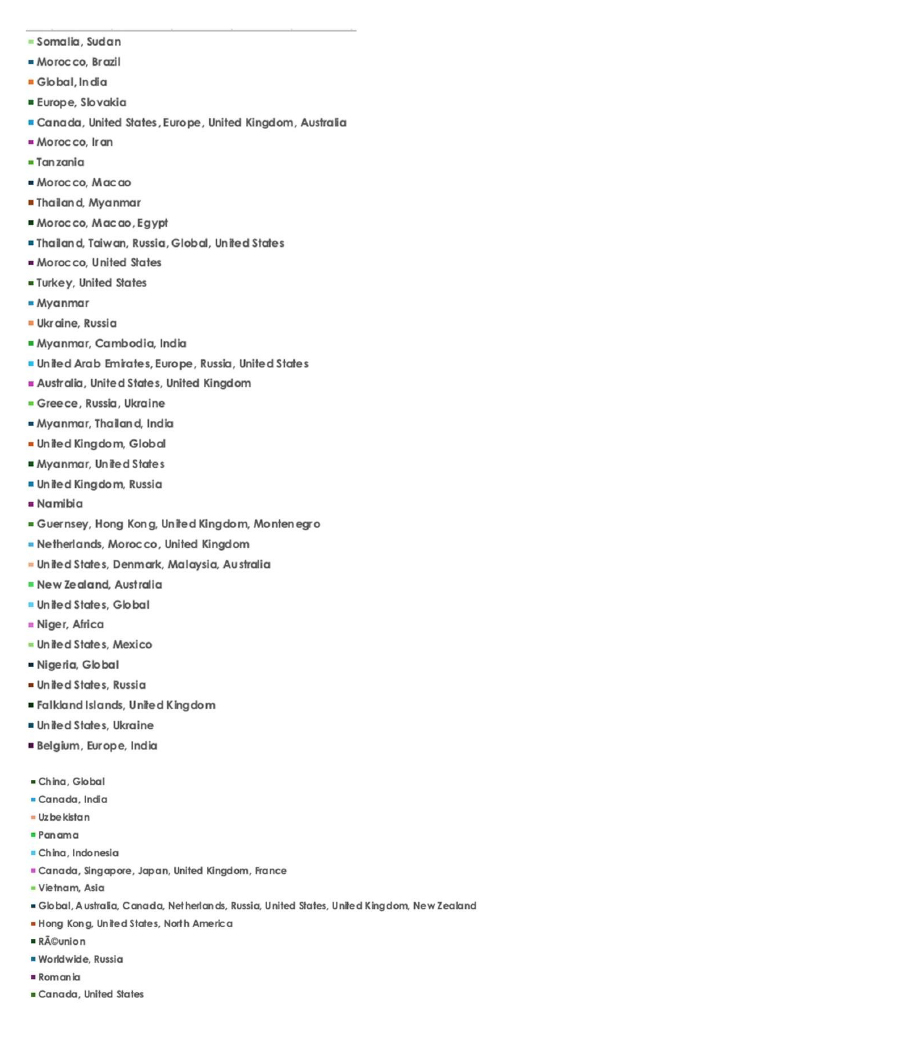
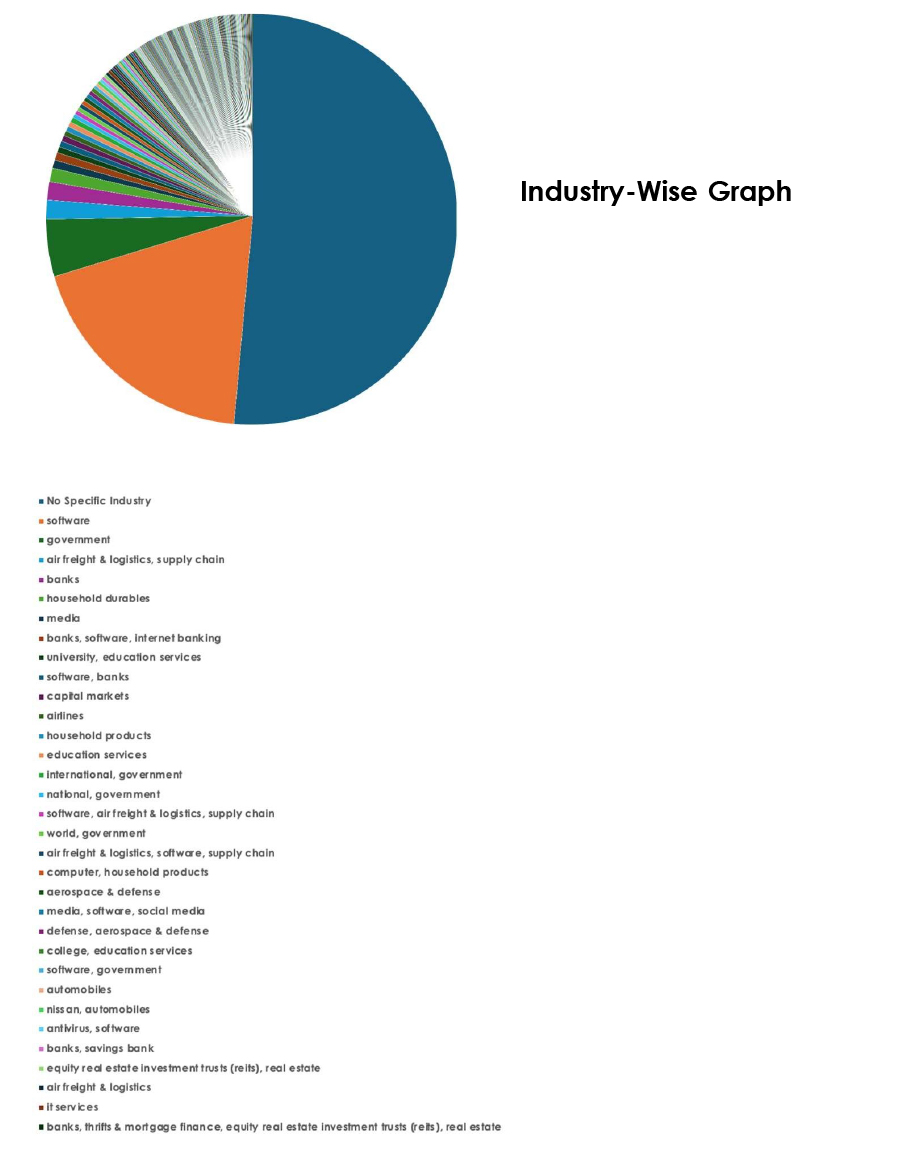
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR.
