Published On : 2026-03-13

Ransomware of the week
CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple – industries, geography, and technology – that could be relevant to your organization.
Type: Ransomware (MedusaLocker family variant).
Target Geography: No specific geographic focus identified; incidents observed globally. Target Sectors: Manufacturing, healthcare, education, professional services, technology, government, and financial organizations.
Target Technologies: Windows OS, enterprise networks, Remote Desktop Protocol (RDP), network file shares, and Active Directory environments.
Introduction:
CYFIRMA Research and Advisory Team has found Chip Ransomware while monitoring various underground forums as part of our Threat Discovery Process.
Chip Ransomware
Chip ransomware has been identified as a file-encrypting malware strain associated with the Medusa Locker ransomware family. The malware encrypts victim files using a combination of AES and RSA encryption algorithms and appends the “.chip1” extension (the number may vary) to affected files, preventing access to the original data. Once executed, the malware generates a ransom note titled “Recovery_README.html” and alters the system environment to notify victims that their files have been encrypted. The message claims that files have been modified rather than damaged and warns victims not to rename or attempt to recover encrypted files using third-party tools, stating that such actions may permanently corrupt the data. The operators further assert that only they possess the capability to restore the encrypted files and indicate that sensitive information may have been collected during the intrusion, potentially to be disclosed if ransom demands are not met. Currently, no publicly available or verified decryption tool exists for this variant, and there is no confirmed assurance that paying the ransom will result in successful data recovery.

Screenshot: File encrypted by the ransomware (Source: Surface Web)
The ransom note associated with Chip ransomware informs victims that their files have been encrypted and renamed with the “.chip1” extension, indicating that access to the data has been restricted. The note states that the files were encrypted using a combination of AES and RSA encryption algorithms and claims that only the attackers possess the capability to restore the affected data. It warns victims not to rename or modify encrypted files and cautions against attempting recovery using third-party tools, asserting that such actions could permanently damage the data. The message also applies psychological pressure by imposing a limited response window, indicating that the ransom demand may increase if contact is not established within a specified timeframe. Additionally, it claims that sensitive data may have been collected during the intrusion and could be disclosed if the ransom is not paid. Overall, the message follows common ransomware coercion tactics designed to create urgency and discourage independent recovery, while offering no verifiable guarantee that file access will be restored after payment.
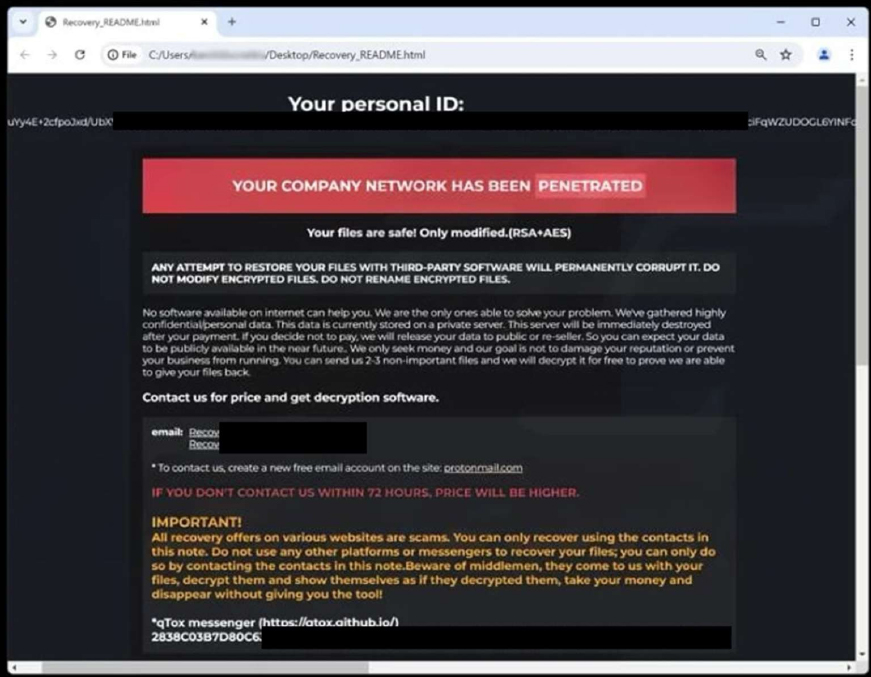
Screenshot: The appearance of Chip’s Ransom Note (Source: Surface Web)

Screenshot: The appearance of Chip’s desktop wallpaper (Source: Surface Web)
The following are the TTPs based on the MITRE Attack Framework
| Tactic | Technique ID | Technique Name |
| Execution | T1129 | Shared Modules |
| Persistence | T1547 | Boot or Logon Autostart Execution |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1134 | Access Token Manipulation |
| Privilege Escalation | T1134.004 | Access Token Manipulation: Parent PID Spoofing |
| Privilege Escalation | T1547 | Boot or Logon Autostart Execution |
| Privilege Escalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1027.005 | Obfuscated Files or Information: Indicator Removal from Tools |
| Defense Evasion | T1134 | Access Token Manipulation |
| Defense Evasion | T1134.004 | Access Token Manipulation: Parent PID Spoofing |
| Defense Evasion | T1140 | Deobfuscate/Decode Files or Information |
| Defense Evasion | T1222 | File and Directory Permissions Modification |
| Defense Evasion | T1497 | Virtualization/Sandbox Evasion |
| Defense Evasion | T1497.001 | Virtualization/Sandbox Evasion: System Checks |
| Defense Evasion | T1564 | Hide Artifacts |
| Defense Evasion | T1564.003 | Hide Artifacts: Hidden Window |
| Credential Access | T1056 | Input Capture |
| Credential Access | T1056.001 | Input Capture: Keylogging |
| Discovery | T1010 | Application Window Discovery |
| Discovery | T1012 | Query Registry |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1497 | Virtualization/Sandbox Evasion |
| Discovery | T1497.001 | Virtualization/Sandbox Evasion: System Checks |
| Discovery | T1614 | System Location Discovery |
| Collection | T1056 | Input Capture |
| Collection | T1056.001 | Input Capture: Keylogging |
Relevancy and Insights:
- The ransomware primarily targets Windows OS, which is utilised by enterprises in a variety of diligence.
- Persistence: The ransomware exhibits continuity mechanisms to ensure its survival and ongoing vicious conditioning within the compromised terrain. This could involve creating autostart entries or modifying system settings to maintain a base and grease unborn attacks.
ETLM Assessment
CYFIRMA’s assessment indicates that the Chip ransomware, associated with the MedusaLocker ransomware family, is likely to continue operating as an extortion- driven malware threat that relies on established ransomware techniques rather than introducing significantly new tactics. The malware already demonstrates core ransomware behaviors, including file encryption, ransom messaging, and warnings discouraging independent recovery attempts, indicating an operational focus on denying access to data in order to pressure victims into payment. If activity continues, the operators may further refine elements of their execution workflow, improve the consistency of their ransom communications, and maintain the use of data-exposure claims to strengthen extortion pressure. However, the current behavior largely aligns with existing ransomware playbooks used by established ransomware families, suggesting that future developments will most likely involve incremental operational adjustments rather than major technical innovations. As a result, the threat is expected to remain focused on opportunistic targeting and data-encryption-based extortion, with limited evidence indicating the introduction of substantially new capabilities.
Sigma rule:
title: New RUN Key Pointing to Suspicious Folder tags:
– attack.privilege-escalation
– attack.persistence
– attack.t1547.001 logsource:
category: registry_set product: windows
detection: selection_target:
TargetObject|contains:
– ‘SoftwareMicrosoftWindowsCurrentVersionRun’
– ‘SoftwareWOW6432NodeMicrosoftWindowsCurrentVersionRun’
– ‘SoftwareMicrosoftWindowsCurrentVersionPoliciesExplorerRun’ selection_suspicious_paths_1:
Details|contains:
– ‘:Perflogs’
– :ProgramData’
– ‘:WindowsTemp’
– ‘:Temp’
– ‘AppDataLocalTemp’
– ‘AppDataRoaming’
– ‘:$Recycle.bin’
– ‘:UsersDefault’
– ‘:Userspublic’
– ‘%temp%’
– ‘%tmp%’
– ‘%Public%’
– ‘%AppData%’ selection_suspicious_paths_user_1:
Details|contains: ‘:Users’ selection_suspicious_paths_user_2:
Details|contains:
– ‘Favorites’
– ‘Favourites’
– ‘Contacts’
– ‘Music’
– ‘Pictures’
– ‘Documents’
– ‘Photos’ filter_main_windows_update:
TargetObject|contains: ‘MicrosoftWindowsCurrentVersionRunOnce’ Image|startswith: ‘C:WindowsSoftwareDistributionDownload’ Details|contains|all:
– ‘rundll32.exe ‘
– ‘C:WINDOWSsystem32advpack.dll,DelNodeRunDLL32’ Details|contains:
– ‘AppDataLocalTemp’
– ‘C:WindowsTemp’ filter_optional_spotify:
Image|endswith:
– ‘C:Program FilesSpotifySpotify.exe’
– ‘C:Program Files (x86)SpotifySpotify.exe’
– ‘AppDataRoamingSpotifySpotify.exe’ TargetObject|endswith:
‘SOFTWAREMicrosoftWindowsCurrentVersionRunSpotify’ Details|endswith: ‘Spotify.exe –autostart –minimized’
condition: selection_target and (selection_suspicious_paths_1 or (all of selection_suspicious_paths_user_* )) and not 1 of filter_main_* and not 1 of filter_optional_*
falsepositives:
– Software using weird folders for updates level: high
(Source: Surface Web)
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
RECOMMENDATIONS
STRATEGIC RECOMMENDATIONS
- Implement competent security protocols and encryption, authentication, or access credentials configurations to access critical systems in your cloud and local environments.
- Ensure that backups of critical systems are maintained, which can be used to restore data in case a need arises.
MANAGEMENT RECOMMENDATIONS
- A data breach prevention plan must be developed considering, (a) the type of data being managed by the company; (b) the remediation process; (c) where and how the data is stored; (d) if there is an obligation to notify the local authority.
- Implement a zero-trust security model alongside multifactor authentication (MFA) to reduce the risk of credential compromise.
- Foster a culture of cybersecurity, where you encourage and invest in employee training so that security is an integral part of your organization.
TACTICAL RECOMMENDATIONS
- Update all applications/software regularly with the latest versions and security patches alike.
- Add the Sigma rule for threat detection and monitoring, which will help to detect anomalies in log events, identify and monitor suspicious activities.
- Establish and implement protective controls by actively monitoring and blocking identified indicators of compromise (IoCs) and reinforcing defensive measures based on the provided tactical intelligence
Active Malware of the Week
Type: Information stealer| Objectives: Data Exfiltration | Target Technology: IOS |
Target Geography: Europe
CYFIRMA collects data from various forums based on which the trend is ascertained. We identified a few popular malwares that were found to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the week
This week, “Amos Stealer” is in focus.
Overview of Operation Amos Stealer Malware
The AMOS Stealer campaign targeting macOS devices distributes its malicious payload through a disk image file named Clearl_AI.dmg, which is presented as a legitimate software installer. When the disk image is opened, it contains an application bundle named Clearl AI.app along with several supporting folders and files typically found in macOS disk images. This structure is designed to resemble a normal macOS application package, thereby reducing suspicion from users during installation. By disguising the malware as a legitimate application, attackers rely on social engineering techniques to convince users to execute the malicious file.
Once the application is launched, the malware operates quietly in the background while interacting with legitimate macOS processes and services. It establishes encrypted network communication with external infrastructure and performs actions intended to evade security detection. During execution, the malware accesses various system configuration files and creates hidden files within user directories, which may assist in collecting system-related information and maintaining its activity on the infected machine. By trusted domains, encrypted connections, and masquerading techniques, the threat attempts to conceal its operations while enabling attackers to gather sensitive data from compromised macOS systems.
Attack Method
The attack begins with the distribution of a malicious macOS disk image named Clearl_AI.dmg, which is presented as a legitimate application installer. When the disk image is opened, it reveals an application bundle called Clearl_AI.app along with several supporting folders that are commonly found in standard macOS installation packages. This familiar structure helps the malicious package appear authentic and reduces the likelihood that a user will suspect any abnormal activity. Once the user runs the application, the embedded executable inside the bundle is launched and begins interacting with the macOS operating system.
After execution, the malware performs several background operations while blending into normal system activity. It initiates several processes that resemble legitimate macOS services and interacts with system components responsible for authentication, preferences, and background services. During this stage, the malware accesses multiple system configuration files and directories associated with protected cloud storage and system preferences. It also creates or modifies files within user-specific directories to store operational data and maintain its activity within the system environment.
In addition to these local activities, malware establishes outbound communication with remote servers using encrypted network connections. These communications allow the compromised system to exchange data with external infrastructure while reducing the visibility of the traffic. The use of encrypted channels and trusted-looking network interactions helps the malware conceal its command-and-control activity within normal internet traffic. By combining social engineering, masquerading techniques, and encrypted communications, the attackers can maintain covert access to the infected macOS system while continuing to collect information from the device.
The following are the TTPs based on the MITRE Attack Framework for Enterprise
| Tactic | Technique ID | Technique Name |
| Execution | T1204.002 | User Execution: Malicious File |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| T1036.001 | Masquerading: Invalid Code Signature | |
| T1553.002 | Subvert Trust Controls: Code Signing | |
| Command and control | T1071 | Application Layer Protocol |
| T1573 | Encrypted Channel |
INSIGHTS
- The distribution approach relies significantly on user trust and visual legitimacy. By packaging the malware within a disk image that closely resembles a standard macOS installer, the attackers create an appearance of authenticity. This method encourages users to execute the file voluntarily, enabling the malicious activity to begin without relying on complex technical exploits.
- The malware’s behavior indicates a deliberate effort to blend with normal system operations. Instead of causing noticeable disruptions, it interacts with commonly used macOS services and directories. This allows the malicious activity to remain subtle and less likely to attract attention while operating within the system environment.
- The campaign also demonstrates an attempt to maintain operational legitimacy within the infected device. By interacting with trusted system processes and legitimate-looking network resources, the malware attempts to appear consistent with routine system activity. This approach helps the threat remain less visible while continuing its underlying operations.
ETLM ASSESSMENT
From an ETLM perspective, AMOS Stealer suggests a future where macOS- targeted threats increasingly mimic legitimate system operations, making malicious activity harder to distinguish from normal processes. Techniques that replicate familiar installation workflows and exploit trusted system components are likely to evolve into more sophisticated social engineering strategies, making deceptive prompts appear fully consistent with standard user interactions. Concurrently, stealthy payloads and encrypted communication channels may be embedded more seamlessly within routine applications and cloud-integrated services. This combination of subtle user manipulation and covert control could allow malware to operate almost invisibly, complicating detection and response efforts. For organizations and employees, the long-term impact may be a gradual erosion of trust in standard macOS processes, as even routine system elements could be leveraged to conceal advanced cyber intrusions.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems.
YARA Rules
rule AMOS_Stealer_Hashes
meta:
description = “Detection rule for AMOS Stealer macOS variant based solely on file hashes”
author = “CYFIRMA” date = “2026-03-10”
strings:
/* Malware Sample Hashes */
$hash_1 =
“7896a1429d7916e6c06fb160491d7a997ee56368dd11e074e33fd0682f1f7108”
$hash_2 =
“5efe3d6ff69002f2cf82683f2d866264d0836b9f02e8b52719ecbd6fecf72a62”
condition:
any of ($hash_*)
Recommendations
Strategic Recommendations
- Develop a comprehensive macOS security strategy that includes proactive monitoring for emerging threats targeting Apple environments.
- Implement organization-wide security awareness programs to educate employees on social engineering techniques and the risks of installing unverified applications.
- Adopt a layered defense approach that integrates endpoint protection, network monitoring, and threat intelligence to reduce the risk of sophisticated malware campaigns.
Management Recommendations
- Ensure timely patching and updates for all macOS systems and critical software to mitigate exploitation through legitimate-appearing installers.
- Establish clear policies on software installation and enforce verification procedures before permitting execution of applications from external sources.
- Conduct regular security audits and penetration tests to evaluate the organization’s readiness against targeted macOS malware attacks.
Tactical Recommendations
- Deploy endpoint detection tools capable of identifying suspicious macOS applications, obfuscated binaries, and anomalous system behavior.
- Monitor system processes and user directories for unauthorized or hidden files, especially those resembling known malware artifacts like Clearl_AI.app or homeenergyd.
- Utilize threat intelligence feeds and hash-based detection to quickly identify and isolate malicious files, including variants of AMOS Stealer.
- Establish incident response playbooks specific to macOS infections, including containment, eradication, and forensic investigation procedures.
CYFIRMA’s Weekly Insights
1. Weekly Attack Types and Trends
Key Intelligence Signals:
- Attack Type: Ransomware Attacks, Spear Phishing, Vulnerabilities & Exploits, Data Leaks.
- Objective: Unauthorized Access, Data Theft, Data Encryption, Financial Gains, Espionage.
- Business Impact: Data Loss, Financial Loss, Reputational Damage, Loss of Intellectual Property, Operational Disruption.
- Ransomware – Qilin Ransomware, The Gentlemen Ransomware| Malware – Amos Stealer
- Qilin Ransomware – One of the ransomware groups.
- The Gentlemen Ransomware – One of the ransomware groups. Please refer to the trending malware advisory for details on the following:
- Malware – Amos Stealer
Behavior – Most of these malwares use phishing and social engineering techniques as their initial attack vectors. Apart from these techniques, exploitation of vulnerabilities, defense evasion, and persistence tactics are being observed.
2. Threat Actor in Focus
China-Linked UAT-9244 Expands Telecom Intrusions Using New Malware Toolset
- Threat Actor: UAT-9244 aka Salt Typhoon
- Attack Type: DLL Sideloading, Keylogging, Living off the Land (LoTL), Malware Implant, Spear-Phishing, Exploitation of Vulnerabilities.
- Objective: Espionage, Data Exfiltration.
- Suspected Target Technology: Cisco, Citrix NetScaler Gateway, Fortinet, IoT, Ivanti, Microsoft Exchange Server, PAN-OS, Sonicwall, Sophos, Windows, VPS, Android Apps
- Suspected Target Geography: Argentina, Bangladesh, Brazil, Burkina Faso, Canada, Egypt, Ethiopia, France, Germany, Guatemala, India, Indonesia, Israel, Japan, Lithuania, Malaysia, Mexico, Netherlands, Pakistan, Philippines, Saudi Arabia, Singapore, South Africa, Swaziland, Taiwan, Thailand, UK, USA, Vietnam, Afghanistan, Australia
- Suspected Target Industries: Chemicals, Cloud Systems, Defense, Education, Engineering, Finance, Government, Healthcare, Hospitality, Law firms, NGOs, Supply Chain, Technology, Telecommunications, Transportation, IT
- Business Impact: Data Theft, Operational Disruption, Reputational Damage
About the Threat Actor
The threat actor Salt Typhoon, active since at least 2020, is a highly sophisticated advanced persistent threat (APT) group believed to be operated by China’s Ministry of State Security (MSS). The group has been linked to high-profile cyber espionage campaigns, with a particular focus on U.S. intelligence agencies’ targets and the exfiltration of critical corporate IP. Salt Typhoon is observed carrying out campaigns in multiple nations globally and is widely regarded as a strategic asset aligned with China’s broader “100-Year Strategy” to expand its global influence and technological dominance.
Some of its tactics, techniques, and procedures (TTPs) overlap with those used by FamousSparrow, suggesting a possible connection. The group is also suspected to have links with the nation-state threat actor APT41 and is assessed to operate with significant resources and advanced cyber-espionage capabilities.
Details on Exploited Vulnerabilities
| CVE ID | Affected Products | CVSS Score | Exploit Links |
| CVE-2021-26855 | Microsoft Exchange Server | 9.8 | Link1, link2, link3, link4 |
| CVE-2026-22548 | BIG-IP Advanced WAF or ASM | 5.9 | – |
| CVE-2021-45461 | FreePBX Rest Phone Apps | 9.8 | – |
| CVE-2025-0944 | Tailoring Management System 1.0 | 9.8 | – |
| CVE-2025-12480 | Triofox | 9.1 | – |
TTPs based on MITRE ATT&CK Framework
| Tactic | ID | Technique |
| Reconnaissance | T1590.004 | Gather Victim Network Information: Network Topology |
| Resource Development | T1587.001 | Develop Capabilities: Malware |
| Resource Development | T1588.002 | Obtain Capabilities: Tool |
| Initial Access | T1190 | Exploit Public-Facing Application |
| Persistence | T1098.004 | Account Manipulation: SSH Authorized Keys |
| Persistence | T1136 | Create Account |
| Privilege Escalation | T1136 | Create Account |
| Defense Evasion | T1562.004 | Impair Defenses: Disable or Modify System Firewall |
| Defense Evasion | T1070.002 | Indicator Removal: Clear Linux or Mac System Logs |
| Credential Access | T1110.002 | Brute Force: Password Cracking |
| Credential Access | T1040 | Network Sniffing |
| Discovery | T1040 | Network Sniffing |
| Lateral Movement | T1021.004 | Remote Services: SSH |
| Collection | T1602.002 | Data from Configuration Repository: Network Device Configuration Dump |
| Command and Control | T1572 | Protocol Tunneling |
| Exfiltration | T1048.003 | Exfiltration Over Alternative Protocol: Exfiltration Over Unencrypted Non-C2 Protocol |
Latest Developments Observed
Recent analysis revealed that UAT-9244 deployed multiple malware implants, including the TernDoor backdoor, the PeerTime peer-to-peer backdoor, and the BruteEntry brute-force scanning tool during its operations. The campaign targeted telecommunications providers and related infrastructure across South America, impacting Windows, Linux, and network edge devices. The activity likely aims to establish persistent access within telecom networks to facilitate long-term intelligence gathering and cyber-espionage operations.
ETLM Insights
UAT-9244, suspected to be an affiliate of Salt Typhoon, is assessed as a state-aligned cyber espionage threat actor primarily focused on long-term intelligence collection and sustained access to sensitive networks rather than financially driven cybercrime. The group’s activities suggest a strategic emphasis on compromising telecommunications infrastructure, government entities, and organizations that possess critical strategic or technological information. Operationally, the threat actor emphasizes stealth and persistence, frequently exploiting publicly exposed vulnerabilities to gain initial access before employing backdoors and credential- based techniques to facilitate lateral movement within compromised environments. Its tradecraft, including the use of covert access mechanisms, carefully managed infrastructure, and credential abuse, reflects a deliberate strategy to maintain a low-profile presence within victim networks for extended intelligence gathering. Based on observed targeting patterns and operational behavior, the actor is expected to continue expanding espionage campaigns against telecommunications providers, government networks, and other strategic sectors worldwide while further refining persistence and access techniques. Consequently, Salt Typhoon and its affiliates remain a persistent threat to critical infrastructure and government-linked organizations, posing ongoing risks to sensitive communications, strategic intelligence, and proprietary technological data.
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
YARA Rules
rule Suspicious_Backdoor_Related_IOCs
meta:
description = “Detects malware artifacts related to suspicious infrastructure and scripts”
author = “CYFIRMA” date = “2026-03-10”
reference = “IOC-based detection rule”
hash_reference = “exa4e835aa0635685e39e7dd112bc5f1b937bbad1b95c7a4fe9c53fcb31da54c79”
strings:
/* Domains */
$domain1 = “updata.mgil01.workers.dev” ascii nocase
$domain2 = “service.oneipsoft.com” ascii nocase
$domain3 = “myoffice.techralsolution.com” ascii nocase
$domain4 = “afddd9d14453d4f9-1e185df7e4-ap-southeast-mnl.timcorpnet.com” ascii nocase
$domain5 = “back-trust-aurora.cluster-ctrjumtpbmf.mnl-east-2.timcorpnet.com” ascii nocase
/* Suspicious script/file indicators */
$file1 = “ps1u_ex200822.ps1” ascii nocase
$file2 = “u_ex200822.ps1” ascii nocase
$file3 = “win32.exe” ascii nocase
$file4 = “win32.dll” ascii nocase
/* Hash indicator (if embedded in scripts/logs) */
$hash1 = “exa4e835aa0635685e39e7dd112bc5f1b937bbad1b95c7a4fe9c53fcb31da54c79” ascii nocase
/* IP indicators */
$ip1 = “13.89.97.154” ascii
$ip2 = “114.119.158.36” ascii
$ip3 = “34.234.200.207” ascii
$ip4 = “54.225.199.17” ascii
$ip5 = “23.23.103.31” ascii
condition:
3 of ($domain*) or 2 of ($file*) or
any of ($ip*) or
$hash1
Recommendations
Strategic Recommendations
- Assess and deploy alternatives for an advanced endpoint protection solution that provides detection/prevention for malware and malicious activities that do not rely on signature-based detection methods.
- Conduct bug bounty programs for proactive vulnerability detection.
- Periodically conduct vulnerability assessments to help minimize gaps.
Management Recommendations
- Regularly reinforce awareness of unauthorized attempts with end-users across the environment and emphasize the human weakness in mandatory information security training sessions.
- A data breach prevention plan must be developed, considering,
- the type of data being handled by the company;
- the treatment given;
- where and how the data is stored;
- if there is an obligation to notify the local authority.
- Maintain a product vulnerability response program.
Tactical Recommendations
- Create risk-based vulnerability management with deep knowledge about each asset. Assign a triaged risk score based on the type of vulnerability and criticality of the asset to help ensure that the most severe and dangerous vulnerabilities are dealt with first.
- Ensure robust encryption for critical data, alongside strong policies to govern the storage, usage, and transmission of such data.
- Patch software/applications as soon as updates are available. Where feasible, automated remediation should be deployed since vulnerabilities are one of the top attack vectors.
- Add the YARA rules for threat detection and monitoring, which will help to detect anomalies in log events, identify and monitor suspicious activities.
- Build and undertake safeguarding measures by monitoring/ blocking the IOCs and strengthening defence based on the tactical intelligence provided.
3. Major Geopolitical Developments in Cybersecurity
GPS jamming in the Strait of Hormuz, Iranian hacktivists harass the region
Researchers report that GPS jamming has disrupted navigation for more than 1100 ships in the Strait of Hormuz since the first military strikes against Iran by the end of February. Maritime analysts note that interference with GPS and Automatic Identification System (AIS) signals has caused vessels to appear in incorrect locations on navigation maps, including on land, at airports, and even within sensitive facilities. While GPS interference has long occurred in the region, analysts are now tracking over twenty new AIS jamming clusters across waters near the UAE, Qatar, Oman, and Iran. Shipping traffic through the Strait of Hormuz has slowed as a result, with some Western- affiliated tankers reportedly disabling their tracking signals or reversing course.
Separately, cloud service providers have reported that Iranian drone strikes damaged several data center facilities in the United Arab Emirates and Bahrain, leading to widespread disruptions of cloud services. According to company statements, the strikes caused structural damage, disrupted power supply systems, and triggered fire- suppression systems that led to additional water damage. Operators say they are working with local authorities to restore services while prioritizing staff safety.
Meanwhile, analysts monitoring cyber activity have observed increased pro-Iranian hacktivist operations following the start of the hostilities. The activity has been dominated by a small number of groups responsible for the majority of attacks in the first days of the conflict. Distributed denial-of-service (DDoS) attacks have targeted telecommunications providers and technology organizations in Israel, as well as government entities and infrastructure-related websites in Saudi Arabia, Qatar, Bahrain, and the United Arab Emirates.
ETLM Assessment:
Iran is likely conducting GPS jamming, cyber activity, and drone strikes as part of a broader retaliatory and deterrence strategy following military strikes against it and escalating regional tensions. By disrupting navigation systems in the Strait of Hormuz – a chokepoint through which about 20% of global oil passes – Iran can signal that it has the capability to threaten global trade and energy flows without immediately launching a full military blockade. These electronic warfare actions also fit Iran’s long- standing anti-access/area-denial strategy, which relies on asymmetric tools such as electronic interference, drones, mines, and small naval forces to complicate operations by stronger adversaries and raise the risks for commercial and military traffic in the region. At the same time, cyber and hacktivist operations help Tehran exert pressure on its adversaries.
Israel bombs Iran’s cyber warfare HQ, Iranian hackers target the USA
The Israeli military says it struck a facility in eastern Tehran that it identified as a key center for Iran’s cyber warfare activities. According to the Israeli military, the compound served as a cyber and electronic operations hub linked to the Islamic Revolutionary Guard Corps.
The extent to which the strike will affect Iran’s cyber capabilities remains uncertain. Iranian cyber operations often rely on affiliated groups and loosely connected actors to conduct attacks on the government’s behalf, which may allow activity to continue despite damage to centralized infrastructure. Some analysts believe the strike could significantly disrupt Iran’s ability to coordinate cyber operations in the near term, though ideologically aligned groups and other partners may still attempt cyber activities targeting Israel or its allies.
Meanwhile, according to the latest research, the Iranian state-sponsored threat actor MuddyWater (also known as “Seedworm” or “Static Kitten”) compromised several US entities in early February 2026, including a bank, an airport, US and Canadian non- profits, and the Israeli operations of a US software company. The threat actor is using a new backdoor dubbed “Dindoor” and a Python backdoor called “Fakeset.”
ETLM Assessment:
The activity continued after U.S. and Israeli military strikes against Iran that began on February 28. It remains unclear whether the conflict has disrupted the operations of the threat group, but its previously established access to networks in the United States and Israel places it in a potentially advantageous position to launch further cyber operations.
4. Rise in Malware/Ransomware and Phishing
Qilin Ransomware Impacts Golden Clay Industries Sdn Bhd
- Attack Type: Ransomware
- Target Industry: Manufacturing
- Target Geography: Malaysia
- Ransomware: Qilin Ransomware
- Objective: Data Theft, Data Encryption, Financial Gains
- Business Impact: Financial Loss, Data Loss, Reputational Damage
Summary:
CYFIRMA observed in an underground forum that a company from Malaysia, Golden Clay Industries Sdn Bhd (www[.]gci[.]com[.]my), was compromised by Qilin Ransomware. Golden Clay Industries Sdn Bhd (GCI) is a Malaysian manufacturing company specializing in clay roofing tiles and building materials used in residential and commercial construction projects. The company is recognized as one of Malaysia’s leading producers of high-quality clay roof tiles and roofing systems. The compromised data includes confidential and sensitive information belonging to the organization.
Source: Dark Web
Relevancy & Insights:
- The Qilin Ransomware group operates a Ransomware-as-a-Service (RaaS) model, allowing affiliates to carry out attacks while Qilin provides infrastructure and malware tools.
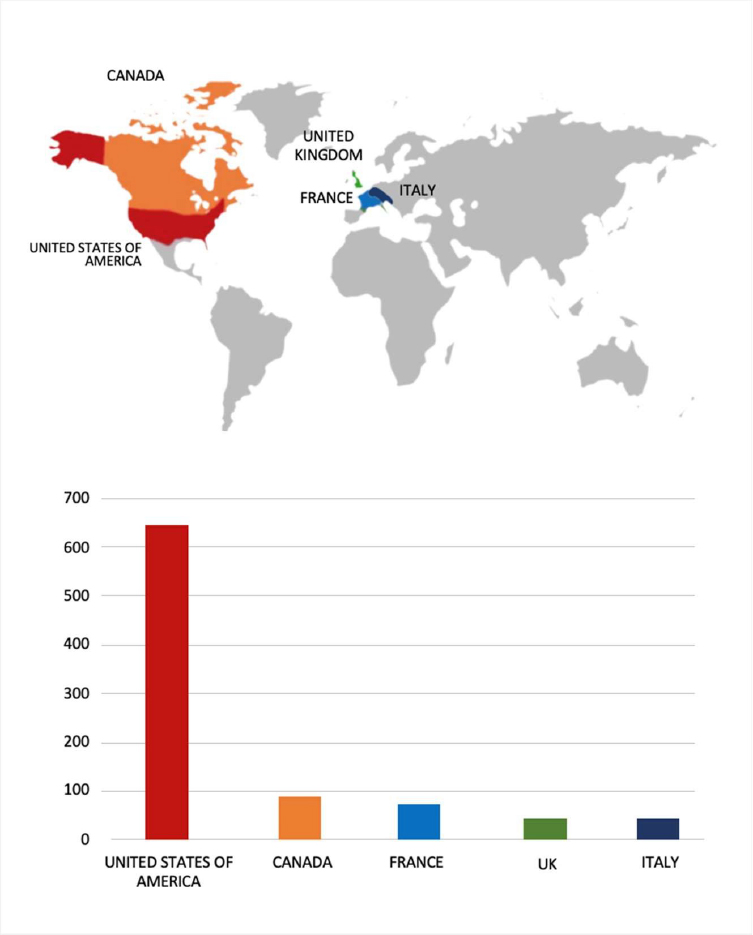
- The Qilin Ransomware group primarily targets countries such as the United States of America, Canada, France, the United Kingdom, and Italy.
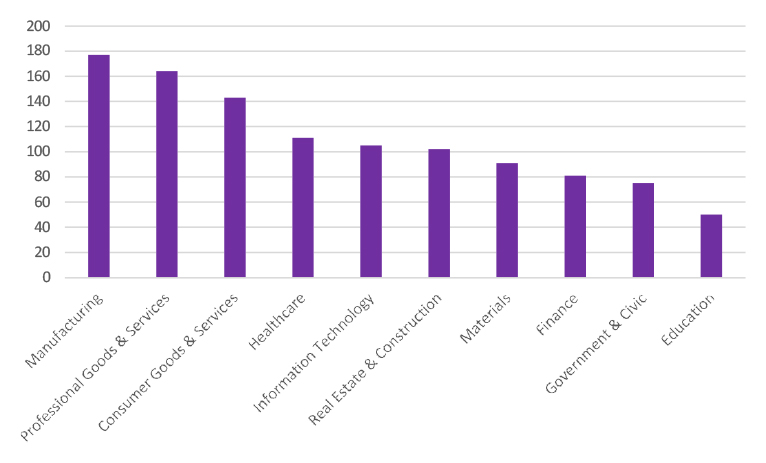
- The Qilin Ransomware group primarily targets industries, including Manufacturing, Professional Goods & Services, Consumer Goods & Services, Healthcare, and Information Technology.
- Based on the Qilin Ransomware victims list from 1st Jan 2025 to 10th March 2026, the top 5 Target Countries are as follows:
- The Top 10 Industries most affected by the Qilin Ransomware victims list from 1st Jan 2025 to 10th March 2026 are as follows:
ETLM Assessment:
According to CYFIRMA’s assessment, Qilin ransomware poses a significant threat to organizations of all sizes. Its evolving tactics, including double extortion (data encryption and leak threats), cross-platform capabilities (Windows and Linux, including VMware ESXi), and a focus on speed and evasion, make it a particularly dangerous actor.
The Gentlemen Ransomware Impacts Reanthong Partcenter
- Attack Type: Ransomware
- Target Industry: Manufacturing
- Target Geography: Thailand
- Ransomware: The Gentlemen Ransomware
- Objective: Data Theft, Data Encryption, Financial Gains
- Business Impact: Financial Loss, Data Loss, Reputational Damage
Summary:
CYFIRMA observed in an underground forum that a company from Thailand, Reanthong Partcenter (www[.]rtvalve[.]com), was compromised by the Gentlemen Ransomware. Sando Tech specialises in the development, design, manufacturing, and sales of machinery. The company offers a range of products, including testing machines, repair services, and consumable parts orders. The data, which has been breached, has not yet appeared on the leak site, indicating that negotiations between the affected party and the ransomware group may be underway. The compromised data includes confidential and sensitive information belonging to the organization.
Source: Dark Web
Relevancy & Insights:
- The Gentlemen is a relatively highly sophisticated ransomware-as-a-service (RaaS) group that emerged in mid-2025.
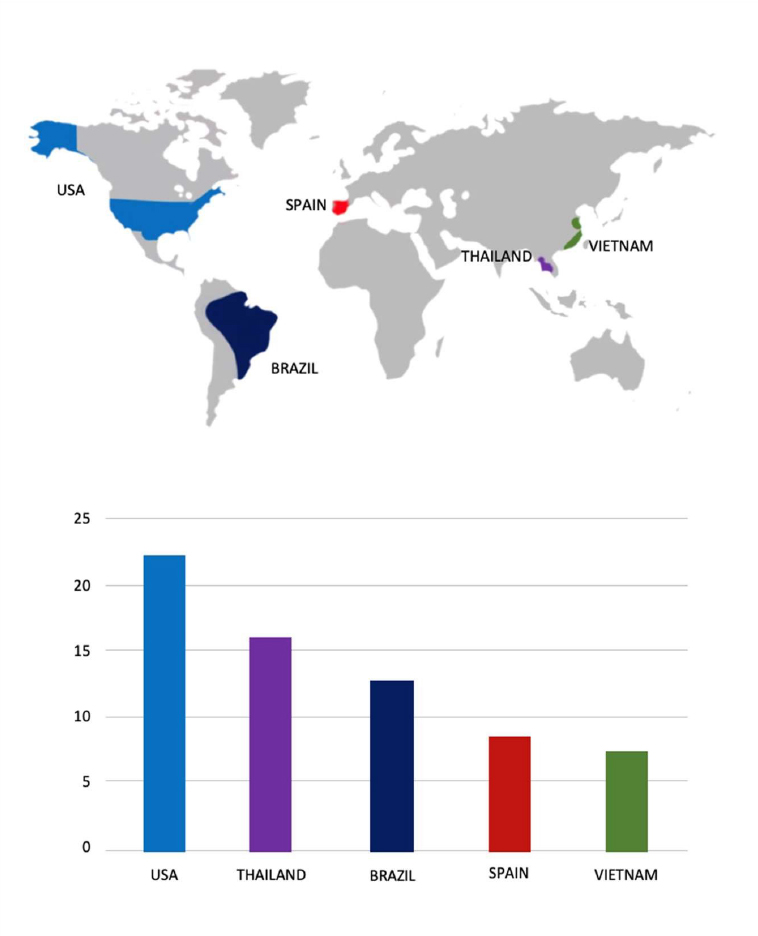
- The Gentlemen Ransomware group primarily targets countries such as the United States of America, Brazil, Thailand, Spain, and Vietnam.
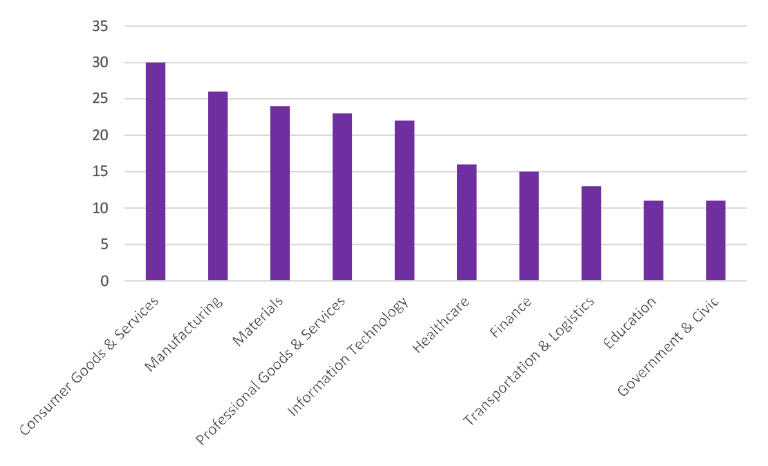
- The Gentlemen Ransomware group primarily targets industries, including Consumer Goods & Services, Manufacturing, Materials, Professional Goods & Services, and Information Technology.
- Based on the Gentlemen Ransomware victims list from 1st July 2025 to 10th March 2026, the top 5 Target Countries are as follows:
- The Top 10 Industries most affected by the Gentlemen Ransomware victims list from 1st July 2025 to 10th March 2026are as follows:
ETLM Assessment:
According to CYFIRMA’s assessment, the Gentlemen Ransomware is a highly adaptive and globally active threat that leverages dual-extortion tactics, combining data theft with file encryption. The group employs advanced evasion and persistence techniques, supports cross-platform and scalable ransomware deployment, and conducts targeted attacks across multiple industries and geographic regions. This combination of capabilities makes it a significant risk to enterprise cybersecurity defenses, particularly for organizations with limited detection and incident-response maturity.
5. Vulnerabilities and Exploits
Vulnerability in Page and Post Clone Plugin for WordPress
- Attack Type: Vulnerabilities & Exploits
- Target Technology: Web Applications / Content Management Systems (WordPress Plugins)
- Vulnerability: CVE-2026-2893
- CVSS Base Score: 6.5 Source
- Vulnerability Type: SQL Injection
Summary:
The vulnerability allows a remote attacker to execute arbitrary SQL queries in the database.
Relevancy & Insights:
The vulnerability exists due to insufficient sanitization of user- supplied data in the “meta_key” parameter in the content_clone() function.
Impact:
A remote user can send a specially crafted request to the affected application and execute arbitrary SQL commands within the application database.
Successful exploitation of this vulnerability may allow a remote attacker to read, delete, or modify data in the database and gain complete control over the affected application.
Affected Products:
https[:]//www[.]wordfence[.]com/threat-intel/vulnerabilities/wordpress- plugins/page-or-post-clone/page-and-post-clone-63-authenticated- contributor-sql-injection-via-meta-key-parameter
Recommendations:
Monitoring and Detection: Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies due to a range of vulnerabilities. The following are the top 5 most affected technologies.
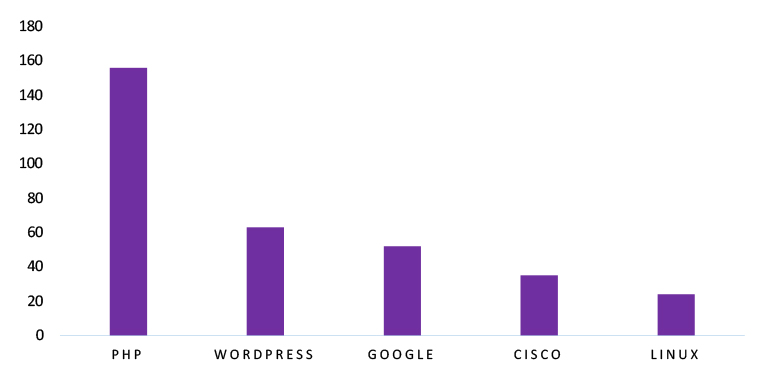
ETLM Assessment
Vulnerability in the Page and Post Clone plugin for WordPress introduces potential risks to websites and web applications that rely on this plugin for content duplication and management. As WordPress powers a significant portion of websites globally, vulnerabilities within its plugin ecosystem can impact various industries, including e-commerce platforms, enterprise portals, government websites, and digital service providers. Ensuring the security of WordPress plugins is crucial for maintaining the integrity of web application databases, protecting sensitive information, and preventing unauthorized data manipulation. Addressing this vulnerability is therefore essential to safeguarding website functionality, maintaining trust in content management systems, and ensuring secure web application operations across different geographic regions and sectors.
6. Latest Cyber-Attacks, Incidents, and Breaches
DragonForce Ransomware attacked and published the data of AHMED MUBARAK DEBT COLLECTION
- Threat Actor: DragonForce Ransomware
- Attack Type: Ransomware
- Objective: Data Leak, Financial Gains
- Target Technology: Web Applications
- Target Industry: Financial Services
- Target Geography: United Arab Emirates
- Business Impact: Operational Disruption, Data Loss, Financial Loss, Potential Reputational Damage
Summary:
Recently, we observed that DragonForce Ransomware attacked and published the data of AHMED MUBARAK DEBT COLLECTION (https[:]//www[.]amdc[.]ae/) on its dark web website. Ahmed Mubarak Debt Collection (AMDC) is a professional debt collection and recovery service provider headquartered in Sharjah, UAE. The company focuses on recovering consumer and corporate debts for organizations while maintaining business relationships between creditors and debtors. The screenshot displays a data leak listing attributed to the DragonForce ransomware group. Based on the visible folder structure and file names, the compromised data appears to include internal system directories, bank-related client information, and user document records. Several directories are labeled with the names of financial institutions such as CBI Bank, Dubai Islamic Bank (DIB), Dubai First Bank, First Abu Dhabi Bank (FAB), Hilal Bank, RAK Bank, and SIB, indicating that the leaked data may contain client case files, debt recovery records, or financial collection information associated with these banking entities.
The presence of system folders such as $RECYCLE.BIN and UsersFolder suggests potential exposure of internal workstation or server data. In addition, multiple files titled “Residency.pdf” with unique numerical identifiers are visible, which likely represent customer residency or identification documents, potentially containing personally identifiable information (PII) used for identity verification during debt collection processes. Overall, the exposed dataset appears to consist of sensitive personal documents, financial case records, and internal operational data related to AMDC’s debt collection activities and its associated banking clients. The total volume of compromised data is estimated to be approximately 107.64 GB.
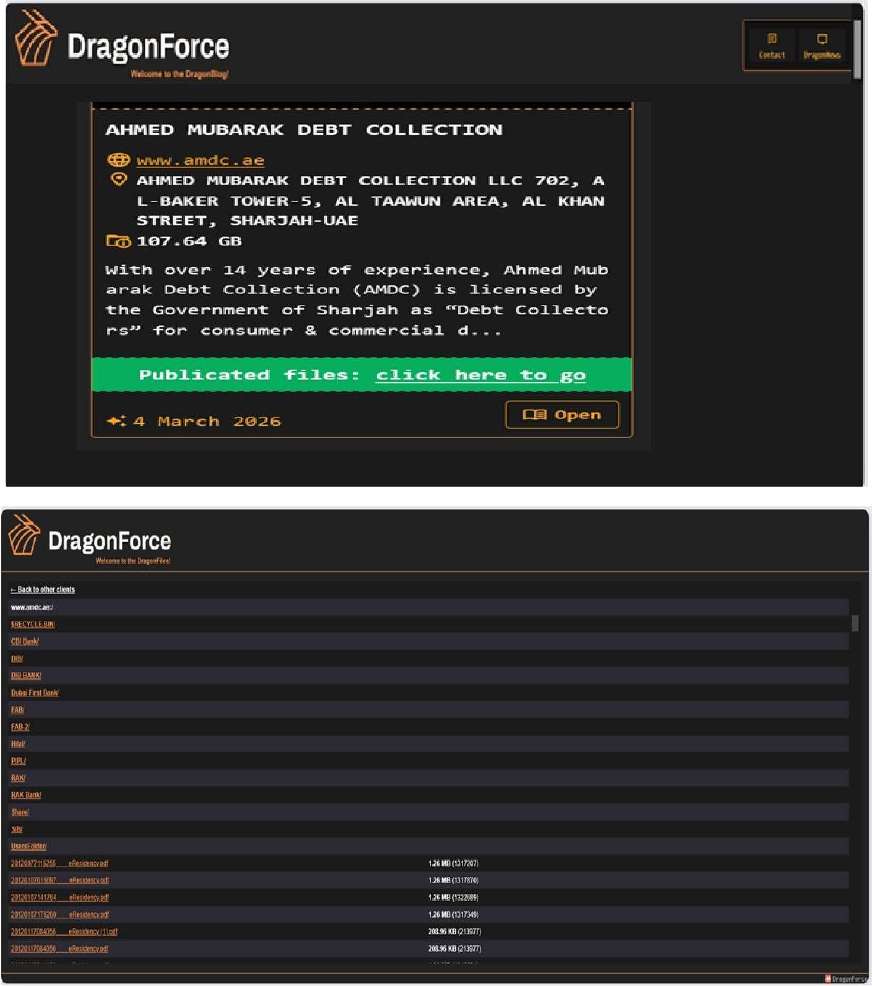
Source: Dark Web
Relevancy & Insights:
- DragonForce Ransomware poses a significant threat as a mature Ransomware- as-a-Service (RaaS) operation active since mid-2023, employing sophisticated double-extortion tactics across Windows, Linux, ESXi, and NAS environments.
- The DragonForce Ransomware group primarily targets industries, such as Professional Goods & Services, Consumer Goods & Services, Manufacturing, Real Estate & Construction, and Information Technology.
ETLM Assessment:
According to CYFIRMA’s assessment, DragonForce represents a significant threat in the ransomware landscape due to its advanced operational methods and extensive use of modified ransomware tools. As it continues to target high-profile organizations globally, ongoing vigilance and proactive cybersecurity strategies will be essential for mitigating risks associated with this formidable threat actor. Organizations should remain alert to the evolving tactics employed by groups like DragonForce to protect their sensitive data and maintain operational integrity.
7. Data Leaks
Shiraume Hospital Patient Data Advertised on a Leak Site
- Attack Type: Data leak
- Target Industry: Healthcare
- Target Geography: Japan
- Objective: Financial Gains
- Business Impact: Data Loss, Reputational Damage
Summary: CYFIRMA’s research team has identified a post on a well-known underground hacking forum published by a threat actor using the alias “NetRunnerPR.” In the post, the actor claims responsibility for a data breach involving Shiraume Hospital, alleging that they successfully gained unauthorized access to the hospital’s network and extracted sensitive patient information.
According to the post, the threat actor claims to have exfiltrated patient PII and medical records from the hospital’s internal systems. The actor also indicated that a full database release has been made available, while earlier messages referenced an initial announcement followed by the eventual release of the complete dataset.
The post includes a large block of database fields and sample records, suggesting that the allegedly stolen data originated from a structured healthcare database. The dataset appears to contain multiple patient-related attributes and medical information fields.
Based on the sample data displayed in the forum post, the allegedly compromised dataset appears to include a wide range of patient information fields, such as:
- Patient identifiers and internal IDs
- Patient height and weight information
- Gender and demographic details
- Patient names and aliases
- Residential address information
- Telephone numbers
- Emergency contact information
- Medical infection indicators and health-related attributes
- Appointment and visit records
- Additional administrative and medical database fields
At the time of analysis, the authenticity of the breach claim remains unverified. The available information originates solely from the threat actor’s forum post, and there has been no official confirmation from the affected organization or relevant authorities.

Source: Underground Forums
John Hay Management Corporation Data Advertised on a Leak Site
- Attack Type: Data leak
- Target Industry: Government
- Target Geography: Philippines
- Objective: Data Theft, Financial Gains
- Business Impact: Data Loss, Reputational Damage
Summary: CYFIRMA’s research team identified a post on a well-known underground hacking forum published by a threat actor operating under the alias “F3TA.” In the post, the actor claims responsibility for a data breach involving John Hay Management Corporation (JHMC), a Philippine government-owned company responsible for managing and overseeing the John Hay Special Economic Zone in Baguio City, Philippines.
According to the forum post, the threat actor alleges that they obtained unauthorized access to the organization’s database and extracted an SQL database dump containing employee-related information. The post advertises the availability of the compromised dataset to other forum members.
Within the post, the actor shared details regarding the size of the leaked SQL database file, reported to be approximately 113.55 MB, along with trimmed sample data intended to demonstrate the authenticity of the compromised dataset.
The shared screenshot displays a structured table containing employee-related data fields, suggesting that the dataset originated from an internal employee management or identity database.
Based on the sample data included in the forum post, the allegedly compromised database may contain the following information:
- Employee names
- Email addresses
- Hashed passwords
- Region information
- Gender details
- Dates of birth
- Employee identification numbers
- Contact numbers
The sample records displayed in the post appear to include multiple employee entries along with associated identifiers and login-related information, indicating potential exposure of organizational staff records.
At the time of analysis, the authenticity of the breach claim remains unverified. The available information originates solely from the threat actor’s forum post, and there has been no official confirmation from John Hay Management Corporation or relevant authorities regarding the alleged compromise.
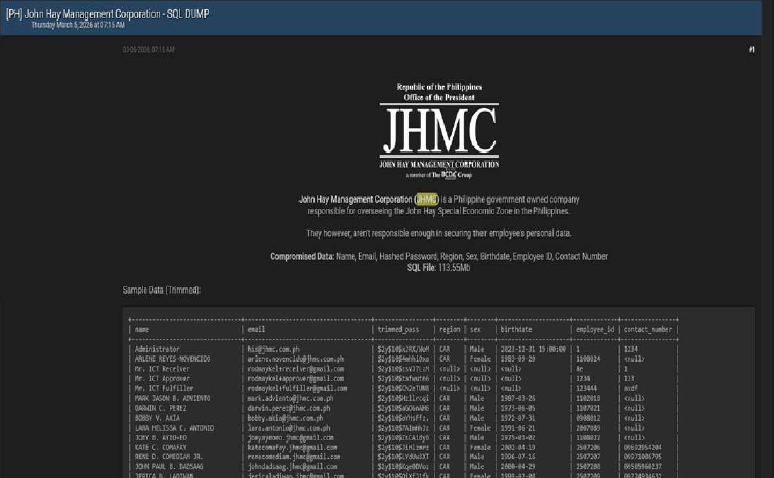
Source: Underground Forums
Relevancy & Insights:
Financially motivated cybercriminals are continuously looking for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to gain access and steal valuable data. Subsequently, the stolen data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor known by the alias “NetRunnerPR” is assessed to be a recently emerged but highly active and capable entity, primarily engaged in data-leak operations. The group’s activity highlights the persistent and fast-evolving cyber threat landscape, driven by underground criminal ecosystems. This development underscores the urgent need for organizations to reinforce their cybersecurity posture through continuous monitoring, improved threat intelligence capabilities, and proactive defensive strategies to protect sensitive information and critical infrastructure.
Recommendations: Enhance the cybersecurity posture by:
- Updating all software products to their latest versions is essential to mitigate the risk of vulnerabilities being exploited.
- Ensure proper database configuration to mitigate the risk of database-related attacks.
- Establish robust password management policies, incorporating multi-factor authentication and role-based access to fortify credential security and prevent unauthorized access.
8. Other Observations
CYFIRMA’s research team identified a post on a well-known underground hacking forum in which a threat actor operating under the alias “Spirigatito” claimed responsibility for a large-scale data breach involving Infutor, a consumer identity management and resolution company
In the post, the threat actor alleges that they successfully compromised Infutor’s systems and obtained a massive dataset containing hundreds of millions of records. The post advertises the availability of the leaked data and includes a brief description of the type of information allegedly compromised.
Infutor is a data and identity resolution company that provides consumer identity intelligence, data enrichment, and verification solutions. The organization helps businesses identify, verify, and understand customers in real time by leveraging large consumer data sets. Infutor operates a global data analytics and risk assessment company serving multiple industries, including insurance, financial services, and marketing.
According to the forum post, the allegedly compromised dataset may include highly sensitive personally identifiable information (PII). The threat actor claims the data contains the following fields:
- Full names
- Dates of birth (DOB)
- Residential addresses
- City, state, and ZIP code information
- Phone numbers
- Social Security Numbers (SSN)
The actor claims the dataset includes approximately 676,798,866 records, allegedly corresponding to hundreds of millions of U.S. citizens, with multiple entries per individual. The post also suggests that the dataset may include records associated with deceased individuals.
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
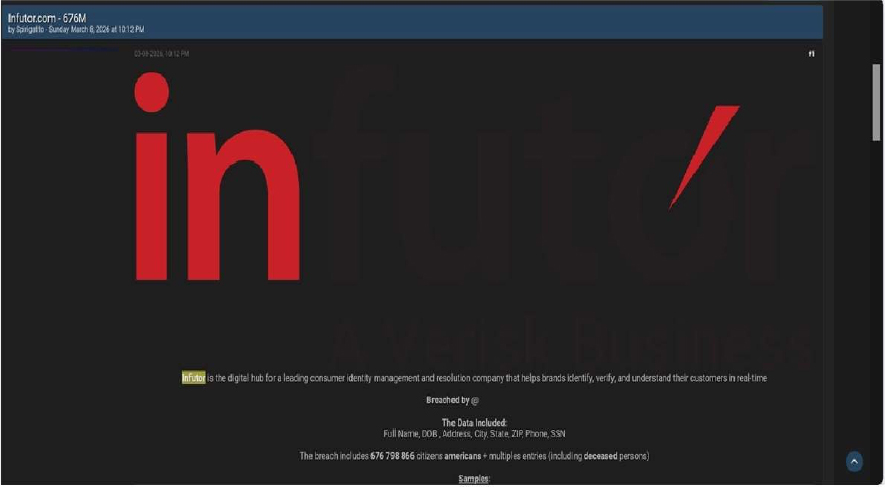
Source: Underground Forums
RECOMMENDATIONS
STRATEGIC RECOMMENDATIONS
- Attack Surface Management should be adopted by organisations, ensuring that a continuous closed-loop process is created between attack surface monitoring and security testing.
- Deploy a unified threat management strategy – including malware detection, deep learning neural networks, and anti-exploit technology – combined with vulnerability and risk mitigation processes.
- Incorporate Digital Risk Protection (DRP) in the overall security posture that acts as a proactive defence against external threats targeting unsuspecting customers.
- Implement a holistic security strategy that includes controls for attack surface reduction, effective patch management, and active network monitoring, through next-generation security solutions and a ready-to-go incident response plan.
- Create risk-based vulnerability management with deep knowledge about each asset. Assign a triaged risk score based on the type of vulnerability and criticality of the asset to help ensure that the most severe and dangerous vulnerabilities are dealt with first.
MANAGEMENT RECOMMENDATIONS
- Take advantage of global Cyber Intelligence, providing valuable insights on threat actor activity, detection, and mitigation techniques.
- Proactively monitor the effectiveness of risk-based information security strategy, the security controls applied, and the proper implementation of security technologies, followed by corrective actions, remediations, and lessons learned.
- Consider implementing Network Traffic Analysis (NTA) and Network Detection and Response (NDR) security systems to compensate for the shortcomings of EDR and SIEM solutions.
- Ensure that detection processes are tested to ensure awareness of anomalous events. Timely communication of anomalies should be continuously evolved to keep up with refined ransomware threats.
TACTICAL RECOMMENDATIONS
- Patch software/applications as soon as updates are available. Where feasible, automated remediation should be deployed since vulnerabilities are one of the top attack vectors.
- Consider using security automation to speed up threat detection, improved incident response, increased the visibility of security metrics, and rapid execution of security checklists.
- Build and undertake safeguarding measures by monitoring/ blocking the IOCs and strengthening defences based on the tactical intelligence provided.
- Deploy detection technologies that are behavioral anomaly-based to detect ransomware attacks and help to take appropriate measures.
- Implement a combination of security controls, such as reCAPTCHA (completely Automated Public Turing test to tell Computers and Humans Apart), Device fingerprinting, IP backlisting, Rate-limiting, and Account lockout to thwart automated brute-force attacks.
- Ensure email and web content filtering uses real-time blocklists, reputation services, and other similar mechanisms to avoid accepting content from known and potentially malicious sources.
Situational Awareness – Cyber News
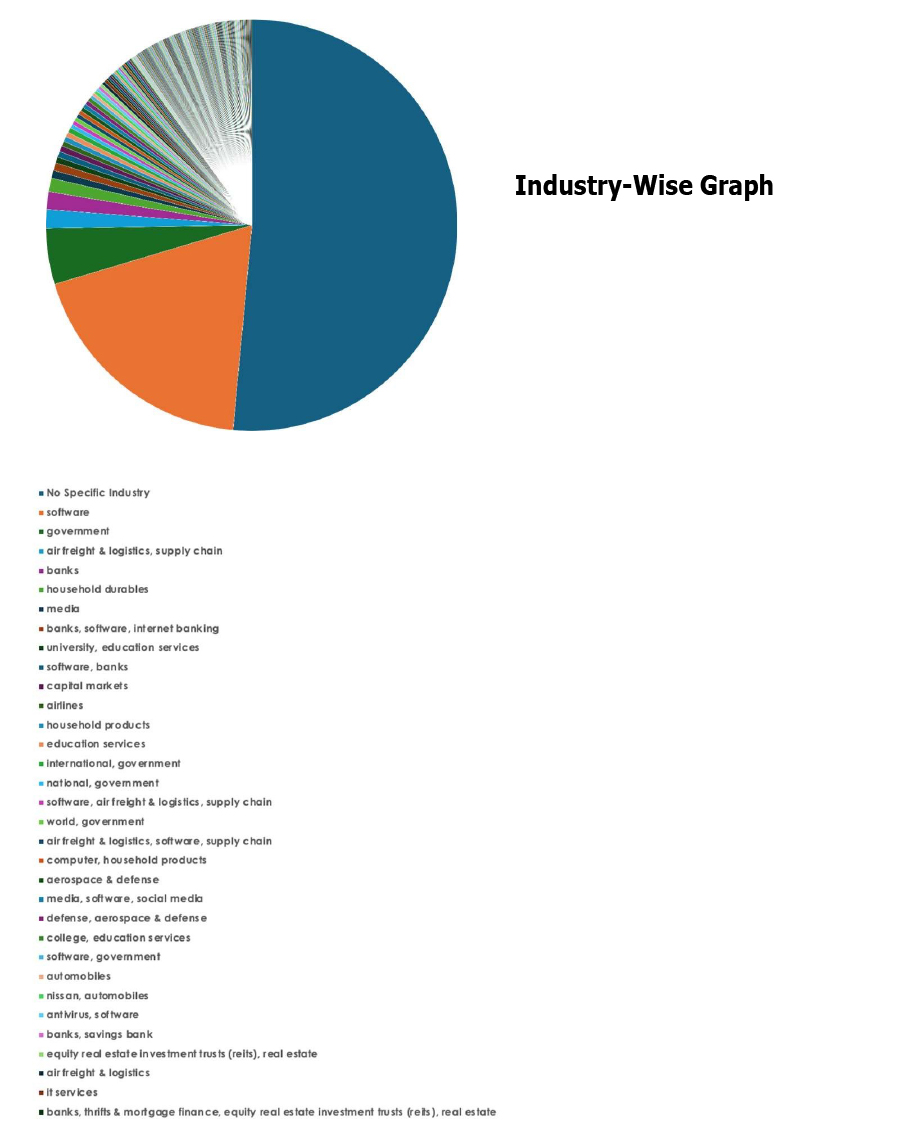
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
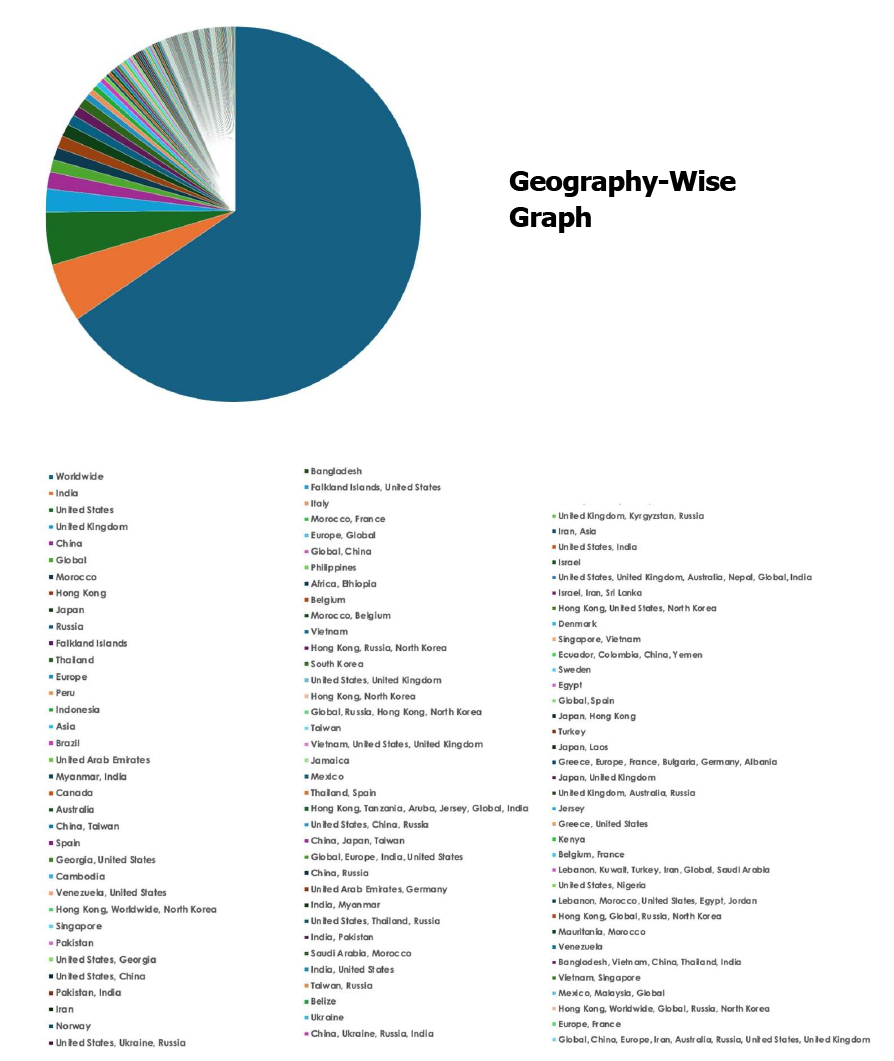
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR.
