Adventures in Cybersecurity
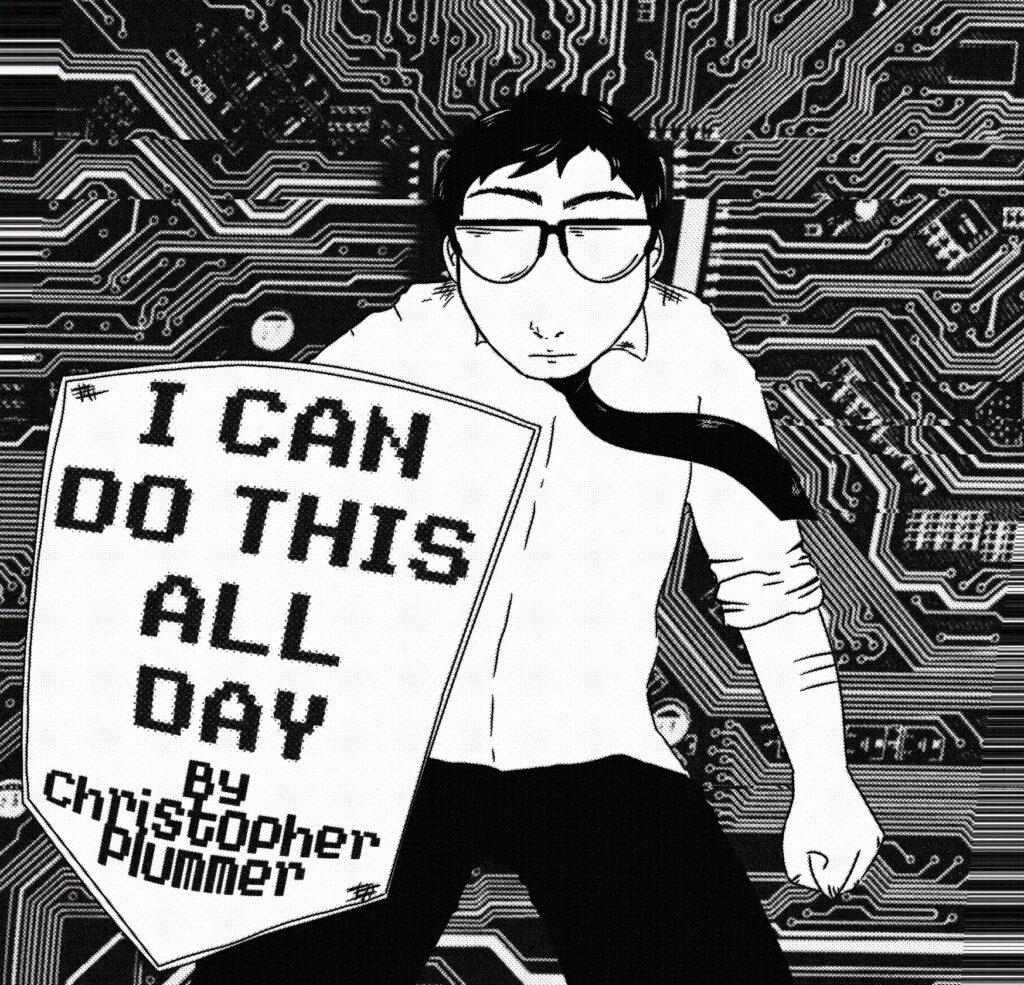
I CAN DO THIS ALL DAY
By Chris Plummer*
[*The Cyber Defender]
Last year a New Hampshire hospital was breached, and I was the only one who knew. And that cannot happen again.
I have been consuming ransomware victim reports every day for nearly a decade, as long as I have worked as a healthcare defender. This information has always been readily available, provided through a number of avenues but lately I consume it through the H-ISAC (the global information sharing exchange for healthcare). I am always searching for a company that is either my organization, affiliated with my organization, has a supplier relationship with my organization, or is local to my state or region.
The truth is, by the time an organization lands in a ransomware victim report, and by extension mentioned on a criminal data leak site, it’s too late and the damage is done. The network has already been penetrated, persistence achieved, the mission is over – the organization has already been operationally impaired in some way and their data has been stolen. As a third party to this, nothing can be done except to inquire privately with the victim and try to understand your own level of exposure by virtue of any connected relationship. Rather – understand how much water went under the bridge. Generally it’s far too late and these conversations are a formality.
Late last year I encountered a New Hampshire hospital on a ransomware data leak site. An enormous quantity of data was dumped on the dark web, as depressing as you could possibly imagine. I analyze data dumps like this with frustrating regularity and the only emotion besides anger is pain. Pain, because I know how I would feel if my own health system’s data was in that same place. Like my personal effects were thrown out on the lawn for everyone to take. I never want this to happen to anyone, and when it’s close to home, it is even harder to watch.
I have long had close relationships with federal partners. They had no awareness of this event, and further, the hospital itself had no awareness. What seems likely to have happened is the ransomware attacker (unsuccessfully) negotiated with the wrong company, which is actually not unusual. Or their correspondence was simply not getting through to the victim. In the end, a massive trove of sensitive data was dumped, and Chris Plummer was the sole reason our government or the victim had any idea it had happened. Because I read an intelligence report.
The State of New Hampshire Fusion Center has not staffed a cybersecurity analyst for quite some time now. It is imperative that role gets filled. If that person does nothing but read ransomware victim reports, they will instantly bring up the level of cybersecurity for our state’s critical infrastructure sectors, and notably the hospitals every single one of us depend on to be the backstop of our society.
New Hampshire has been awarded $204 million in federal funding to advance rural healthcare in this state, and I am here to plead for some sliver of that to be focused on cybersecurity – beginning with this unfilled analyst role in the Fusion Center. It is the right place to start. Our endgame is a suit of armor around all of the hospitals in New Hampshire. This is a first step in getting there. We have to get there. We can do it. I am absolutely convinced of it.
Every hospital is responsible for protecting human lives, their physical well being, the security of their private information, no matter how big or how small. We must centrally support all of them from a cyber perspective. Not a single person living in this state deserves anything less.

Chris Plummer is a cybersecurity architect from Manchester. Nearly expelled from UNH for hacking in 1996, Chris has gone on to serve the US Navy and New Hampshire hospitals as a cyber defender in a career spanning nearly three decades. In 2023 he discovered a major vulnerability in Google’s Gmail, forcing security changes at some of the world’s largest names in tech. Chris has been a White House cybersecurity advisor for healthcare, served as an expert panelist for federal agencies, and his work has been covered in podcasts and media outlets across the globe – including this one! He is an assistant martial arts instructor here in the city, has run up McIntyre hundreds of times, and is a regular at the Backroom. You can reach him at [email protected]
