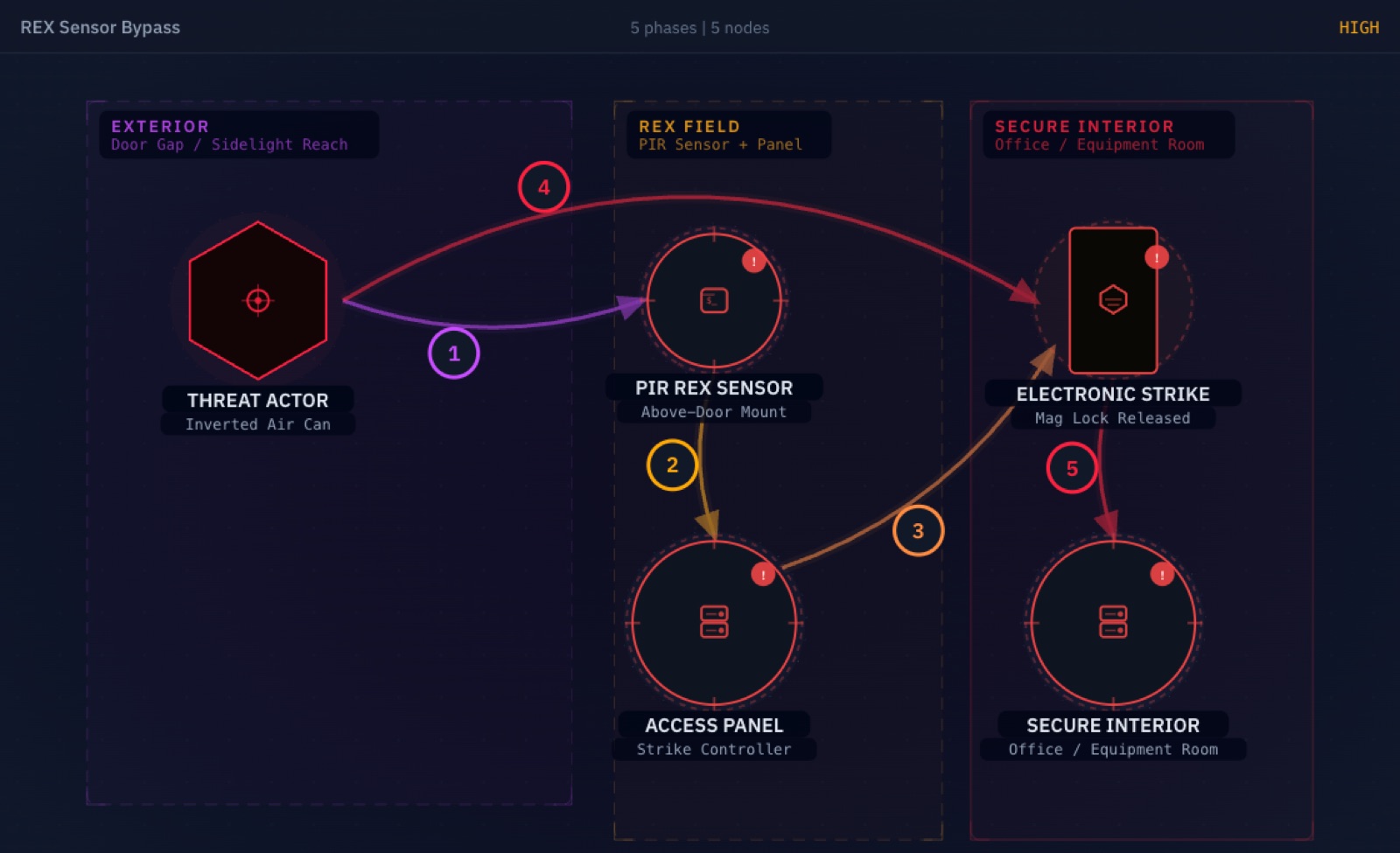
Your organization spent $50,000 on a state-of-the-art access control system. Encrypted badge readers. Biometric scanners. Mantrap entries. Impressive.
We bypassed it with a $10 can of compressed air from Office Depot. And then, just to make sure the client understood the scope of the problem, we did it again with a piece of cardboard.
Open interactive version →
The Vulnerability Nobody Tests
Every secured door needs a way out. Fire codes mandate unimpeded egress. On doors secured with electromagnetic locks, which have no mechanical release, that requirement is typically satisfied by a Passive Infrared (PIR) Request to Exit (REX) sensor that detects an approaching occupant and releases the lock automatically.
The assumption built into every access control design: only authorized personnel are ever on the secure side of that door.
The problem: REX sensors cannot verify that assumption. They detect change. They do not verify identity, presence, or intent. And the physical gap between a door and its frame, or between a door and an adjacent glass panel, is often all the access an attacker needs to reach into that detection zone from the wrong side.
This is not a software vulnerability. It does not have a CVE. It does not show up in a Nessus scan. It is a physics problem baked into millions of installed access control systems worldwide.
The Engagement: Main Office Entry
During a recent physical assessment, our team arrived at the client’s main office. The lobby was professional, the badge readers were modern, and the access control system had clearly received significant investment.
Past the reception desk, several interior office doors caught our attention. Each door had one consistent feature: a visible gap between the door itself and an adjacent glass sidelight panel. And through that gap, visible from the outside, was the characteristic dome of a REX sensor mounted on the interior door frame.
The sensor was doing exactly what it was designed to do. It was watching the secure side of the door for anyone who needed to exit. It had no way to know we were watching it from the wrong side.
Bypass 1: Compressed Air
Tools required: One can of compressed air duster. Available at any office supply store. Price: $9.99.
Our team positioned the straw nozzle of an inverted compressed air can through the gap between the glass panel and the door frame, angling it upward toward the REX sensor dome.
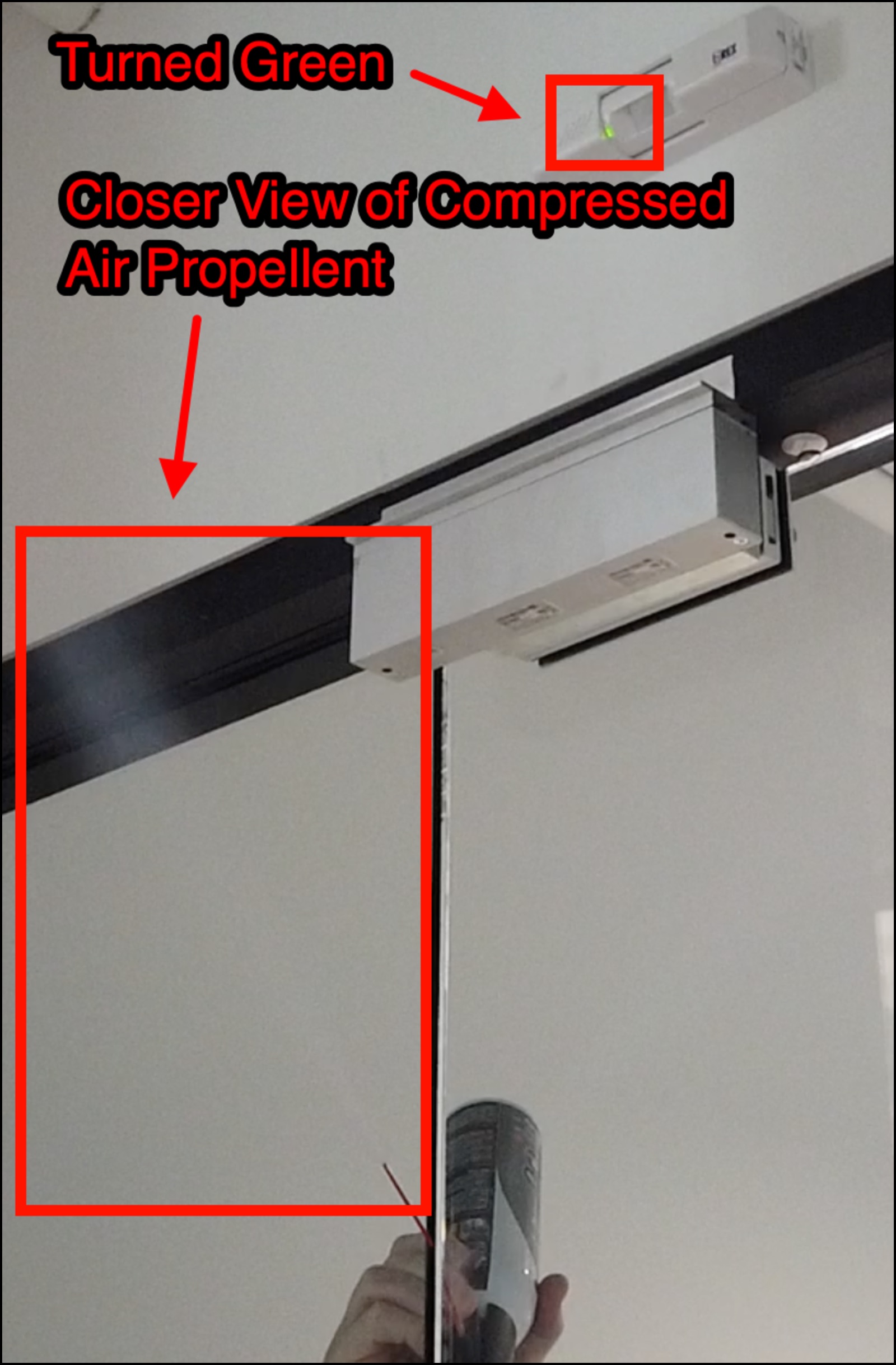
When a compressed air can is inverted, it expels liquid propellant rather than pressurized gas. That propellant, commonly 1,1-difluoroethane (HFC-152a), has a boiling point of -24.7 degrees Celsius at atmospheric pressure per NIST. Rapid evaporation during discharge drives the spray cold fast: direct contact with a target surface can transiently reach roughly -40 degrees Celsius, with briefly colder spikes possible right at the nozzle. The free plume itself sits nearer the boiling point as it travels, but the combination of low temperature and forward motion is what matters to the sensor.
PIR sensors detect changes in infrared radiation across segmented detection zones created by a Fresnel lens. They require two things to fire: a temperature differential from ambient, and motion across those zones. The propellant plume delivers both simultaneously. The sensor cannot distinguish between a human body radiating heat across its detection field and a column of rapidly moving supercooled gas producing the inverse effect.
We pressed the trigger.
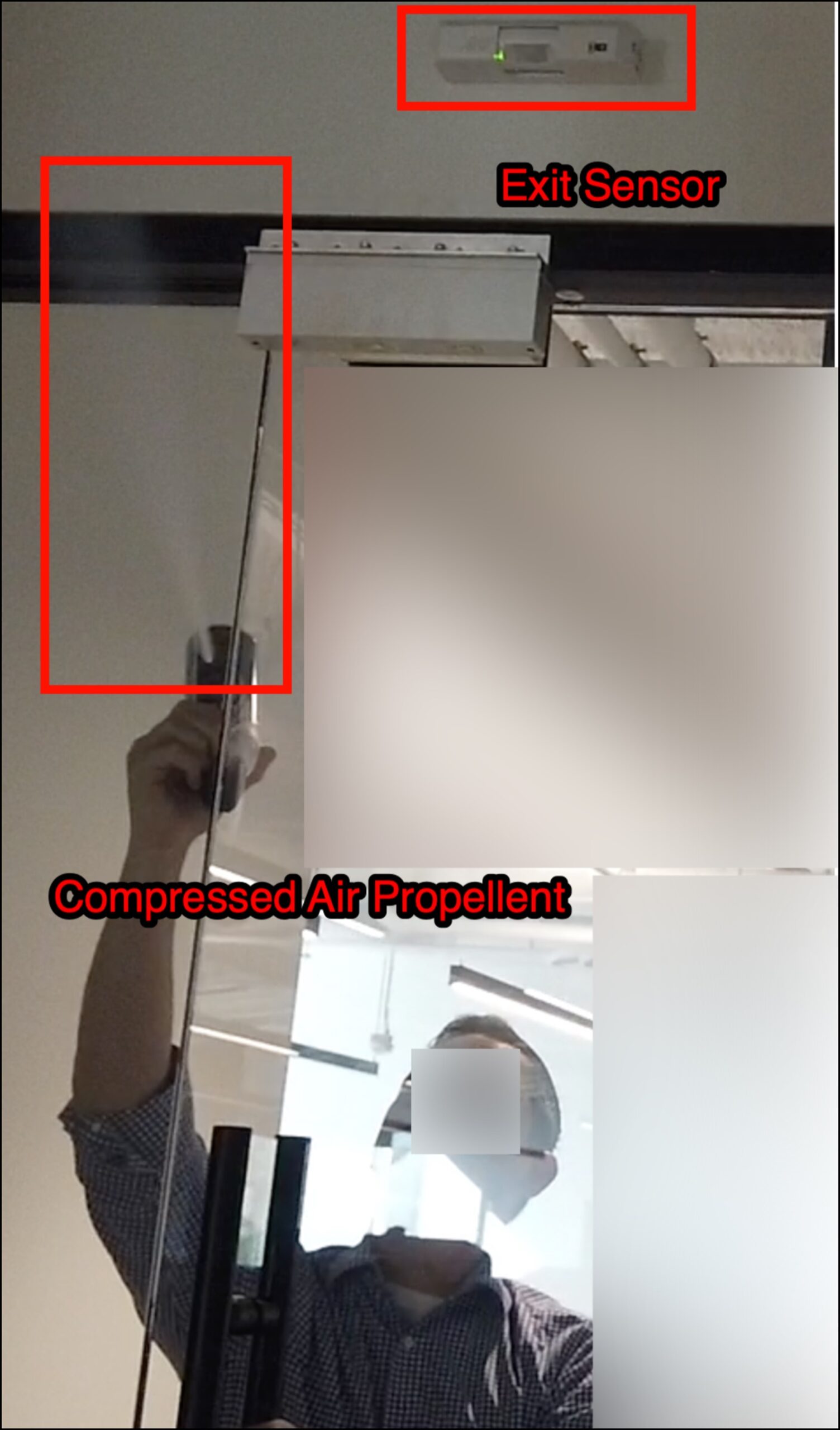
The light turned green.
The door opened.
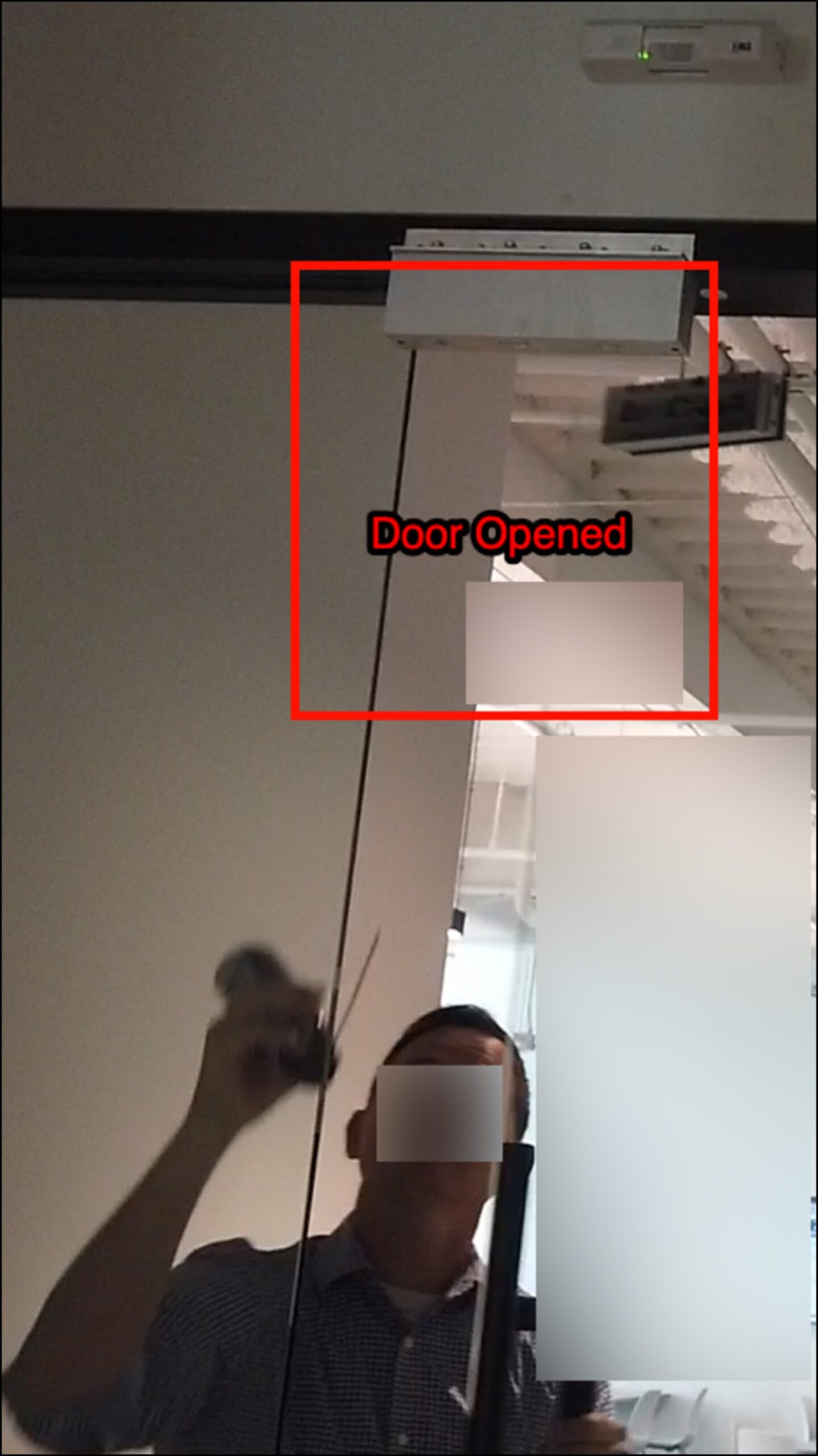
Total elapsed time: 11 seconds.
Bypass 2: Cardboard
For the second demonstration, we wanted to show the client something more unsettling: this attack does not require any specialized tool, any purchase, or any advance preparation.
We picked up a piece of cardboard from a discarded shipping box near the office supply area. We inserted one edge through the gap at the side of the glass panel and moved it slowly within the sensor’s detection zone.
The cardboard, near ambient temperature, provides less dramatic thermal contrast than compressed air. But it does not need to be warmer or colder than the room to work. The dominant mechanism is thermal occlusion: cardboard is opaque across the 8 to 14 micrometer infrared band that PIR sensors watch. As it sweeps through the detection zones, it blocks and unblocks the background thermal pattern behind it: the wall, the door frame, any warmer body nearby. From the pyroelectric element’s perspective, the infrared pattern is changing even though the cardboard itself is room temperature. That change, combined with physical motion across Fresnel zone boundaries, is enough to satisfy the trigger threshold on a standard sensitivity setting.
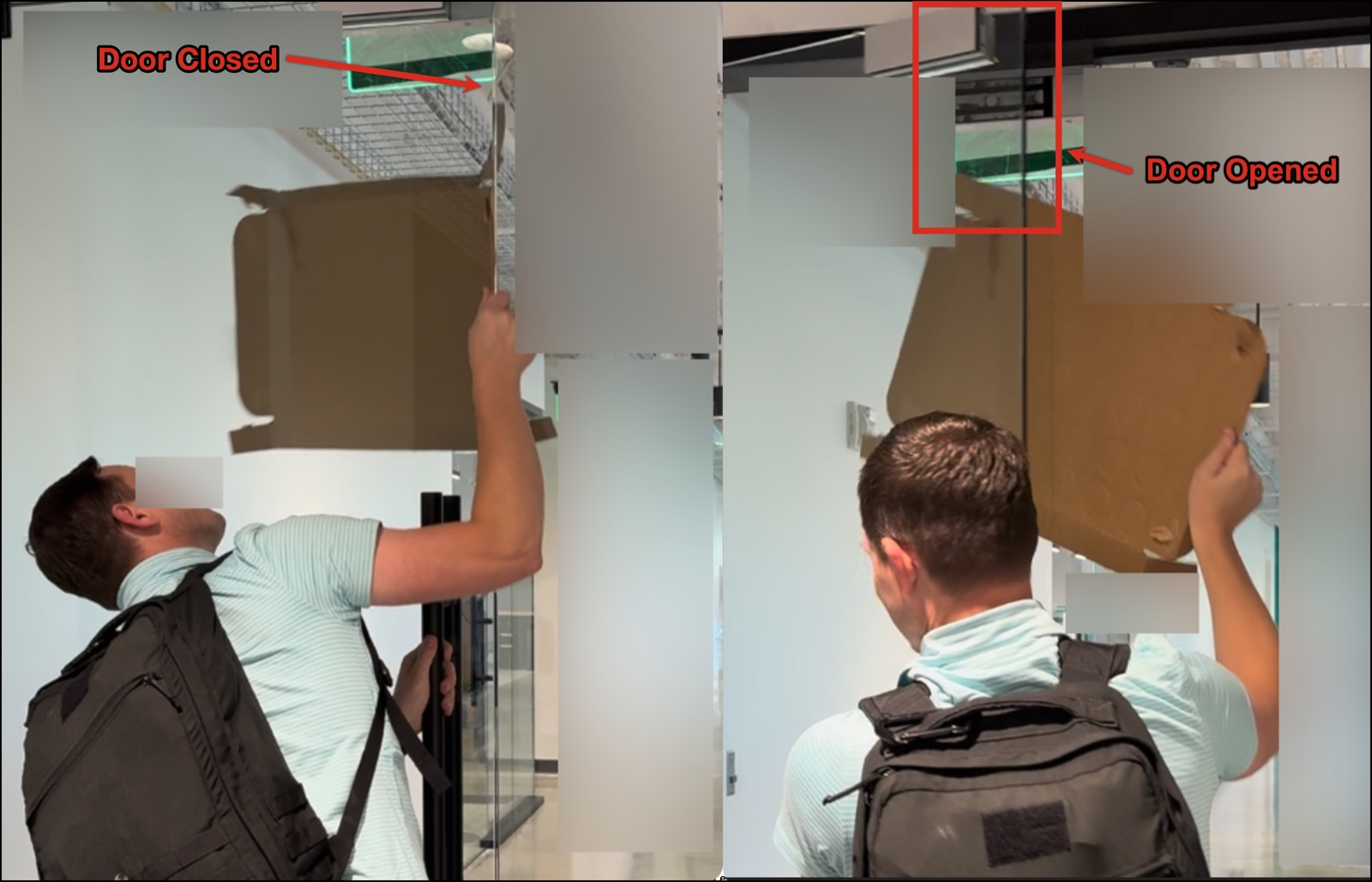
The light turned green again.
The door opened again.
This time the tool cost nothing. The attacker needed no preparation, no equipment, no cover story for carrying unusual items. A cardboard box from any office trash bin was sufficient.
Why This Works: The Physics
PIR sensors are inherently change detectors. A pyroelectric sensing element registers shifts in incident infrared energy. The Fresnel lens array in front of the element divides the field of view into alternating active and blind zones. When an infrared source crosses from one zone to the next, the element generates a voltage differential that the sensor interprets as motion.
Critically, the sensor detects that the infrared pattern changed. It does not analyze what caused the change. It does not verify that the source is a human. It does not confirm that the approaching object is on the correct side of the door.
This means any input that produces a detectable change in the infrared pattern across Fresnel zone boundaries satisfies the trigger conditions. Compressed air propellant delivers cold with forward momentum, producing a dramatic thermal differential. Cardboard works through infrared occlusion, blocking and unblocking the background thermal pattern as it moves. Both produce the change the sensor is looking for. Both unlock the door.
This is not a design flaw in any particular manufacturer’s product. It is a fundamental limitation of passive infrared detection. A PIR REX sensor, by definition, cannot authenticate. It can only detect.
The Compliance Gap
This finding is particularly frustrating for security teams because it is invisible to standard compliance audits.
A compliance assessment verifies:
- Badge readers are installed
- Access logs are maintained
- Credentials are properly managed
- REX sensors are present (required for fire code egress)
What a compliance assessment does not verify:
- Whether REX sensors can be triggered from outside the secure area
- The physical relationship between sensor placement and door gaps
- Whether adjacent glass panels create an exploitable line of sight to the sensor
- Whether the sensor is PIR-only or dual-technology
- Whether REX events are correlated with door position sensor data
The audit passes. The access logs are clean. The door opens for anyone with a $10 purchase and 11 seconds.
Real-World Impact
Once inside the main office, our team had access to the same resources any insider would. Workstations left logged in. Network drops for implant deployment. Physical access to servers, network switches, and backup media. The ability to move through the building without badge access being recorded, because we never used a badge.
Physical access changes the entire threat model. Endpoint detection does not stop someone who can physically touch your infrastructure. Network monitoring does not flag someone on a wired drop who is already inside your perimeter. The assumption that the interior of your building is the secure zone collapses the moment that assumption is the only thing standing between an attacker and your assets.
Remediation
Immediate actions:
- Audit REX sensor placement relative to door gaps and glass panels. Walk every secured door. If you can see the sensor from outside, an attacker can likely reach it. If there is a gap at the door bottom, sides, or adjacent glass, test whether objects can be inserted into the detection zone.
- Install door sweeps and kick plates. Metal kick plates at the door bottom and adjustable door sweeps eliminate or dramatically reduce under-door gaps. This is a low-cost, immediate mitigation.
- Seal gaps around sidelights and glass panels. Any gap between glass and frame adjacent to a secured door is a potential bypass vector. Rubber molding, security astragals, and proper weatherstripping close these gaps.
- Add push-to-exit buttons as a secondary mechanism. A button requires physical contact on the secure side of the door. It cannot be triggered by anything inserted through a gap. Per NFPA 101 7.2.1.6.2 and IBC 2021 1010.2.9, the button must directly interrupt power to the lock, independent of the access control system electronics, and hold the door unlocked until the lock is manually reset. (The 30-second minimum unlock duration in the code applies to the sensor-release path, not the manual push-button.)
Longer-term solutions:
- Upgrade to dual-technology sensors. PIR-plus-microwave sensors require both detection methods to trigger simultaneously, which is specifically designed to resist single-channel bypasses like canned air (the microwave channel does not respond to a cold plume). No published demonstration, to our knowledge, has shown the canned-air bypass defeating both channels simultaneously. Dual-tech is not a guaranteed countermeasure (physical gap sealing and sensor relocation remain the most reliable mitigations), but it removes the single-input bypass that makes this attack so cheap.
- Correlate REX events with door position sensors. If the REX fires but the door does not physically open, that is an anomaly worth flagging. Repeated REX triggers without corresponding door-open events indicate potential tampering attempts.
- Implement video analytics tied to REX events. Correlate sensor triggers with camera coverage of the door area. Require confirmation of human presence before the unlock signal is sent, or flag triggers that do not correspond to visible human activity for review.
- Relocate sensors deeper into the secure space. A REX sensor mounted on the ceiling above the approach path, rather than on the door frame itself, places the detection zone well outside the reach of anything that could be inserted through a door gap.
The Bigger Picture
This assessment revealed two separate bypass methods against the same door configuration, using tools that any person could carry without raising suspicion and without any technical knowledge of access control systems.
The cardboard finding is the one that should keep facility security managers up at night. It requires no purchase, no preparation, and no explanation if discovered. The attacker is holding trash.
Physical security testing is not about checking whether badge readers are installed. It is about what happens when someone who should not be inside your building decides to test your assumptions. Your access control policy assumes that physical separation enforces logical separation. A piece of cardboard tested that assumption and found it wanting.
Ask yourself: when was the last time someone actually tried to bypass your access controls? Not audited the policy. Not reviewed the logs. Actually stood at your secured doors and tested whether they hold.
If the answer is “never” or “not recently,” you have compliance. You do not yet have security.
If your scan reports keep growing but your remediation rate has not changed, the gap is already there. BladeIntel publishes threat intelligence and security research to help businesses understand the risks they face. For more analysis like this, follow us at bladeintel.com or subscribe to our threat briefings.
Key Takeaways
| What Compliance Checks | What Attackers Exploit |
|---|---|
| Badge readers installed | REX sensor placement relative to gaps |
| Access logs maintained | Physical door and glass panel gaps |
| Fire code egress compliance | PIR sensor thermal and motion physics |
| REX sensors present | Dual-technology vs. single-technology detection |
Bottom line: Compliance checks the lock. We check the physics.
All bypass demonstrations described in this post were performed during an authorized physical penetration test under a signed statement of work. The client has since implemented the recommended remediations. All images shown are from the authorized engagement.
