The Vendor That Opened Every Door
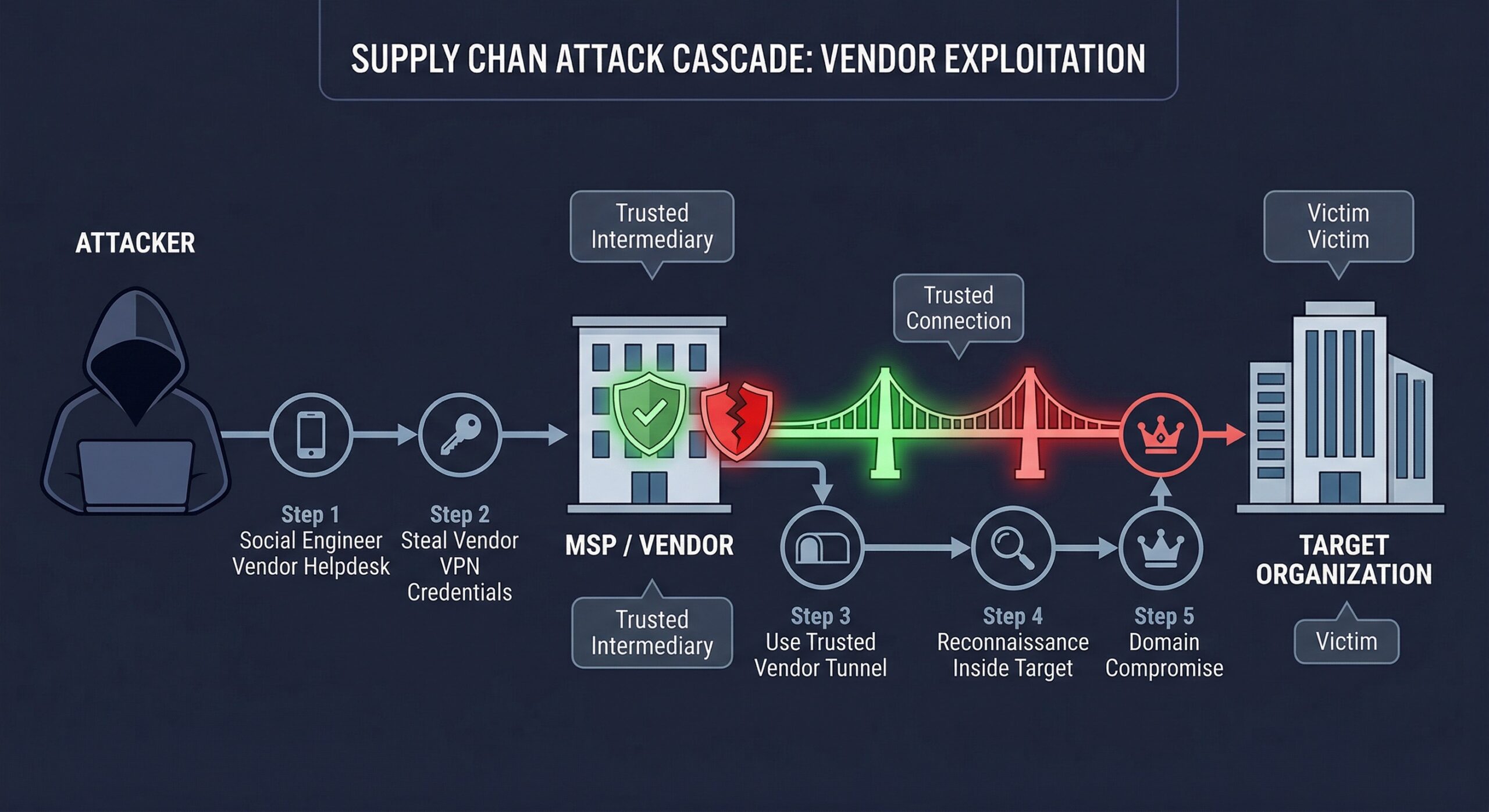
During a red team engagement for a defense contractor, we spent two weeks testing their hardened perimeter. MFA everywhere. Segmented networks. Well-trained employees who reported our phishing attempts.
Then we pivoted to their managed service provider.
The MSP had VPN access for “maintenance purposes.” Their help desk gave us credentials after a 10-minute social engineering call. Those credentials worked on the contractor’s network. Within 24 hours, we had access to classified program documentation.
The contractor had spent millions on their own security. Their vendor spent next to nothing.
Your security is only as strong as your weakest vendor.
Why Supply Chain Attacks Work
The Trust Problem
Organizations extend trust to vendors:
- VPN access for remote support
- API credentials for integrations
- Physical access for maintenance
- Network connectivity for managed services
Each trust extension is a potential attack path.
The Visibility Problem
| Your Environment | Vendor Environment |
|---|---|
| You control security policy | You hope they have one |
| You monitor for threats | You can’t see their network |
| You train employees | You trust their training |
| You test defenses | They probably don’t |
The Asymmetry Problem
Attackers have learned: why attack the fortress when you can attack the supply wagon?
| Direct Attack | Supply Chain Attack |
|---|---|
| Hardened target | Softer target |
| Monitored activity | Less visibility |
| Limited access | Often privileged access |
| High effort | Often easier |
Major Supply Chain Breaches (Recent History)
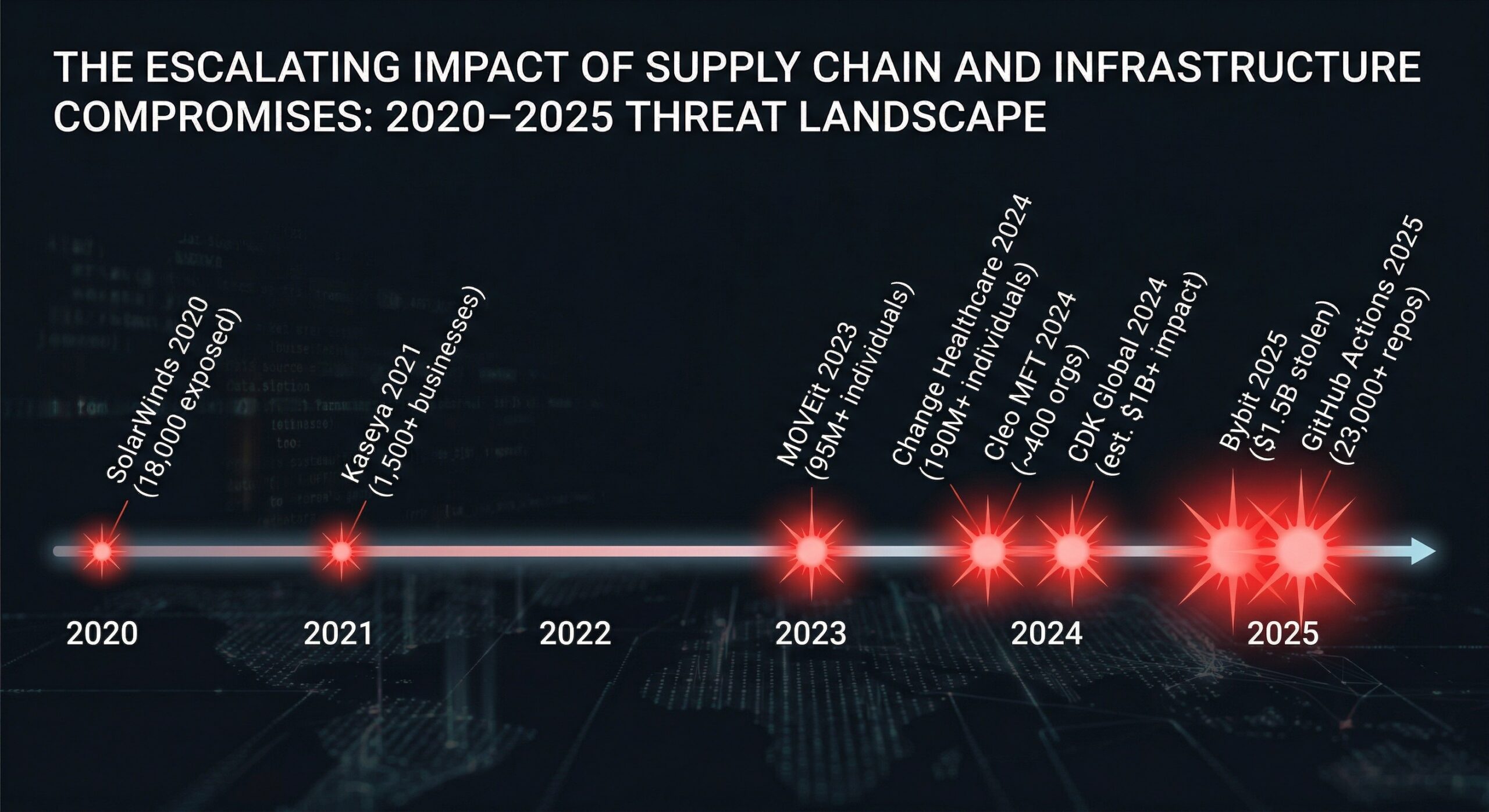
SolarWinds (2020)
- Attack Vector: Compromised software update mechanism
- Victims: 18,000+ organizations received the trojanized update; fewer than 100 actively targeted including US government agencies
- Access Achieved: Trusted software with administrative privileges
- Lesson: Even “trusted” software can be weaponized
Kaseya (2021)
- Attack Vector: MSP management platform vulnerability
- Victims: 1,500+ businesses through ~60 MSPs
- Access Achieved: Ransomware deployment via trusted management tool
- Lesson: One vendor compromise affects thousands
MOVEit (2023)
- Attack Vector: Zero-day in file transfer software
- Victims: 2,770+ organizations, 95M+ individuals affected
- Access Achieved: Data exfiltration from trusted file transfers
- Lesson: Data sharing tools are high-value targets
Change Healthcare (2024)
- Attack Vector: Stolen credentials used to access a Citrix remote access portal lacking MFA
- Victims: 192M+ individuals; disrupted healthcare claims processing nationwide
- Access Achieved: Healthcare payment processing disruption
- Lesson: Central chokepoints create systemic risk
XZ Utils Backdoor (2024)
- Attack Vector: Multi-year social engineering campaign to embed a backdoor in the XZ compression library used across nearly all Linux distributions
- Victims: Caught days before widespread distribution; would have compromised SSH authentication on millions of servers
- Access Achieved: Backdoor in a trusted open-source dependency, targeting SSH authentication
- Lesson: Open-source supply chains are vulnerable to long-term, patient compromise
Polyfill.io (2024)
- Attack Vector: Acquisition of the polyfill.io domain by a malicious entity, followed by injection of malicious JavaScript into the CDN
- Victims: 100,000+ websites that embedded the polyfill.io script
- Access Achieved: Malicious code execution in browsers of site visitors
- Lesson: CDN and third-party script dependencies create invisible trust chains
What We Test (And What We Find)
Vendor Access Assessment
We evaluate how vendors connect to your environment:
| Access Type | Common Finding |
|---|---|
| VPN access | Shared credentials, no MFA, excessive permissions |
| API integration | Overprivileged tokens, no rotation, poor secrets management |
| Physical access | Unescorted access, badge sharing, no background checks |
| Remote support | Persistent access, unmonitored sessions, credential reuse |
Vendor Security Posture
Through OSINT and authorized testing, we assess:
Technical Indicators:
- Public-facing vulnerabilities
- Data exposure (leaked credentials, misconfigured storage)
- Email security (SPF/DKIM/DMARC configuration)
- Certificate management
Organizational Indicators:
- Security certifications (SOC 2, ISO 27001)
- Incident history
- Employee security awareness (social media OPSEC)
- Published security practices
Trust Boundary Analysis
We map how vendor access could enable attacks:
Vendor VPN Access
└── Corporate Network (VLAN 10)
└── Active Directory Access
└── Service Account Enumeration
└── Domain Admin Path Identified
└── Access to Production Data
The Questionnaire Problem
What Organizations Do
Send 200-question security questionnaires to vendors. Receive checkbox answers. File in compliance folder. Never verify.
Why It Doesn’t Work
| Questionnaire Says | Reality Often Is |
|---|---|
| “MFA is implemented” | MFA is available but not enforced |
| “Annual pentest performed” | Pentest scope was limited, findings not remediated |
| “Encryption at rest” | Encryption keys stored with data |
| “Security awareness training” | Annual 15-minute video, no testing |
| “Incident response plan” | Plan exists, never tested |
The Attestation Gap
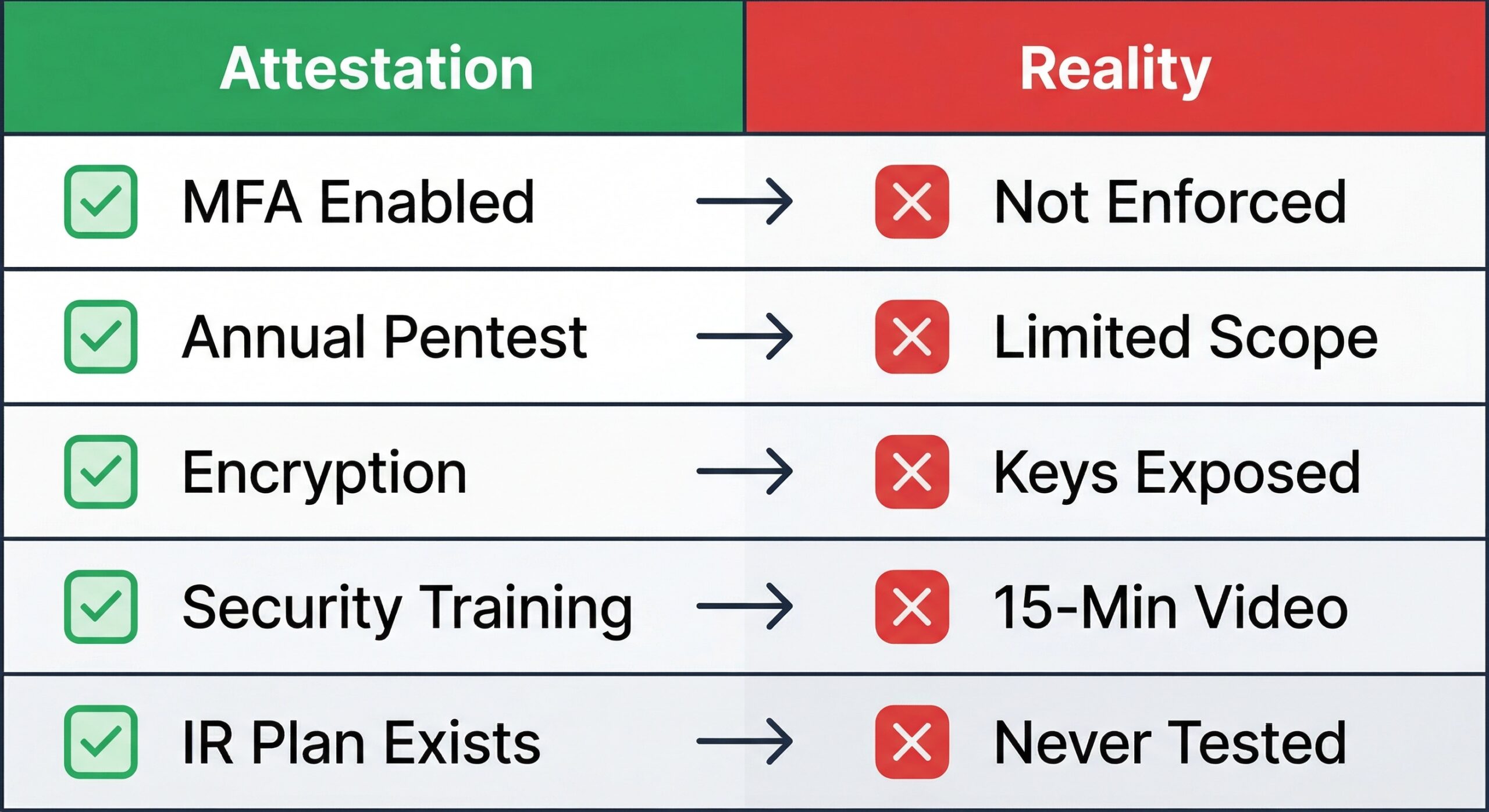
Vendors attest to their security based on their understanding of the question. That understanding varies wildly:
Question: “Do you perform vulnerability scanning?”
- Vendor interpretation A: “We run Nessus weekly”
- Vendor interpretation B: “We have a scanner license”
- Vendor interpretation C: “IT runs Windows Update”
All might answer “Yes.”
A Better Approach: Vendor Security Assessment
Tier Your Vendors by Risk
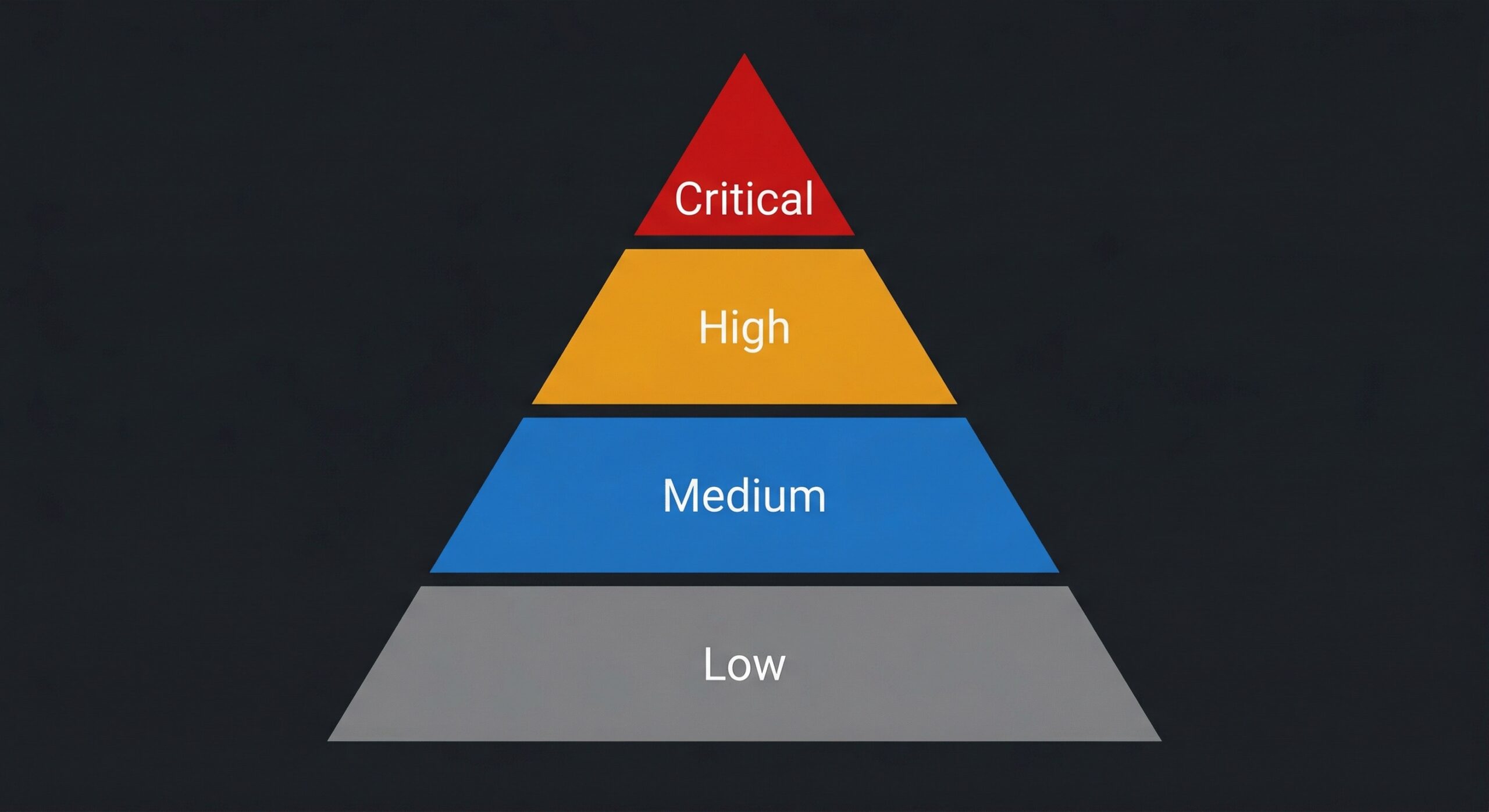
Not all vendors deserve the same scrutiny:
| Tier | Criteria | Assessment |
|---|---|---|
| Critical | Access to crown jewels, network connectivity, data processing | Full security assessment + annual pentest |
| High | Limited privileged access, handles sensitive data | Security questionnaire + verification + periodic assessment |
| Medium | Business-critical but no sensitive access | Security questionnaire + spot verification |
| Low | No sensitive access, easily replaceable | Standard terms, basic verification |
Critical Vendor Assessment Components
For Tier 1 vendors, we recommend:
1. Technical Assessment (Authorized)
- External penetration test of vendor’s environment
- Review of integration points and access controls
- API security assessment
- Credential and secrets management review
2. Process Assessment
- Incident response capability verification
- Change management review
- Employee security practices
- Subcontractor management
3. Ongoing Monitoring
- Continuous external posture monitoring
- Threat intelligence for vendor indicators
- Breach notification alerting
- Annual reassessment
Contractual Requirements
Your vendor contracts should require:
Security Requirements:
- Annual penetration test by qualified third party
- 72-hour breach notification
- Right to audit clause
- Minimum security controls (MFA, encryption, logging)
- Insurance requirements
- Subcontractor approval
Testing Your Vendor Trust
Scenario 1: The MSP Compromise
We simulate a compromised managed service provider:
- Assume attacker has MSP credentials
- Test what access those credentials provide
- Map lateral movement possibilities
- Identify data accessible via MSP access
- Test detection of MSP-based attacks
Common Finding: MSP service accounts have Domain Admin rights “because they need to fix things quickly.”
Scenario 2: The Software Supply Chain
We assess software vendor risk:
- Inventory software with automatic update capability
- Analyze update mechanisms for tampering potential
- Review code signing and verification
- Test detection of malicious updates
- Identify software with excessive permissions
Common Finding: Agents run as SYSTEM, auto-update without verification, have network access.
Scenario 3: The Integration Point
We test API and data integrations:
- Map all vendor API connections
- Assess authentication and authorization
- Test for excessive data exposure
- Verify logging and monitoring
- Test credential rotation capabilities
Common Finding: API tokens never rotated, provide more access than needed.
Case Study: The HVAC Vendor
A financial services client had strong perimeter security. Annual penetration tests consistently showed good results against direct attack paths.
We expanded scope to include vendor assessment.
What We Found
Their building management vendor (HVAC, lighting, access control) had:
- Network connectivity to corporate network (needed for badge system integration)
- VPN credentials stored in shared documentation
- No MFA on VPN access
- Workstations with direct internet access and corporate network access
- Employees who would provide “password resets” over the phone
The Attack Path
Social Engineer HVAC Help Desk
└── Obtain VPN Credentials
└── Connect to Corporate Network
└── Discover Badge System Server
└── Pivot to Corporate Domain
└── Domain Compromise
Sound familiar? This mirrors the Target breach of 2013, where attackers phished an HVAC contractor (Fazio Mechanical Services) to steal network credentials and pivot into Target’s payment systems. The specific technique changes, but the attack pattern has not, because most organizations still have not addressed vendor access risk.
Quick Wins: Immediate Actions
1. Inventory Vendor Access
Create a complete list:
- Who has VPN access?
- What service accounts exist for vendors?
- What API integrations exist?
- Who has physical access?
If you can’t produce this list quickly, that’s your first problem.
2. Apply Least Privilege
For each vendor access:
- What do they actually need?
- Can access be time-limited?
- Can access be scoped to specific systems?
- Is MFA enforced?
3. Monitor Vendor Activity
Ensure logging covers:
- VPN connections from vendor accounts
- Service account authentication
- API usage patterns
- After-hours access
4. Test the Assumptions
Pick your most critical vendor. Call their help desk. Try to social engineer credentials. You’ll learn something valuable either way.
The Board Conversation
When presenting supply chain risk to leadership:
The Risk:
“Our critical vendors have access that, if compromised, would give attackers the same access as a successful direct attack. We’ve verified our own defenses but haven’t verified theirs.”
The Evidence:
“In recent testing, we identified [X] vendor access paths that could enable network compromise. [MSP/Software Vendor/Integration Partner] has access that requires the same scrutiny we apply to our own systems.”
The Ask:
“We’re requesting budget to assess our top 5 critical vendors and establish ongoing vendor security requirements. This addresses a risk that caused the [SolarWinds/Kaseya/MOVEit] incidents that affected organizations with stronger direct defenses than ours.”
Conclusion: Extend Your Perimeter
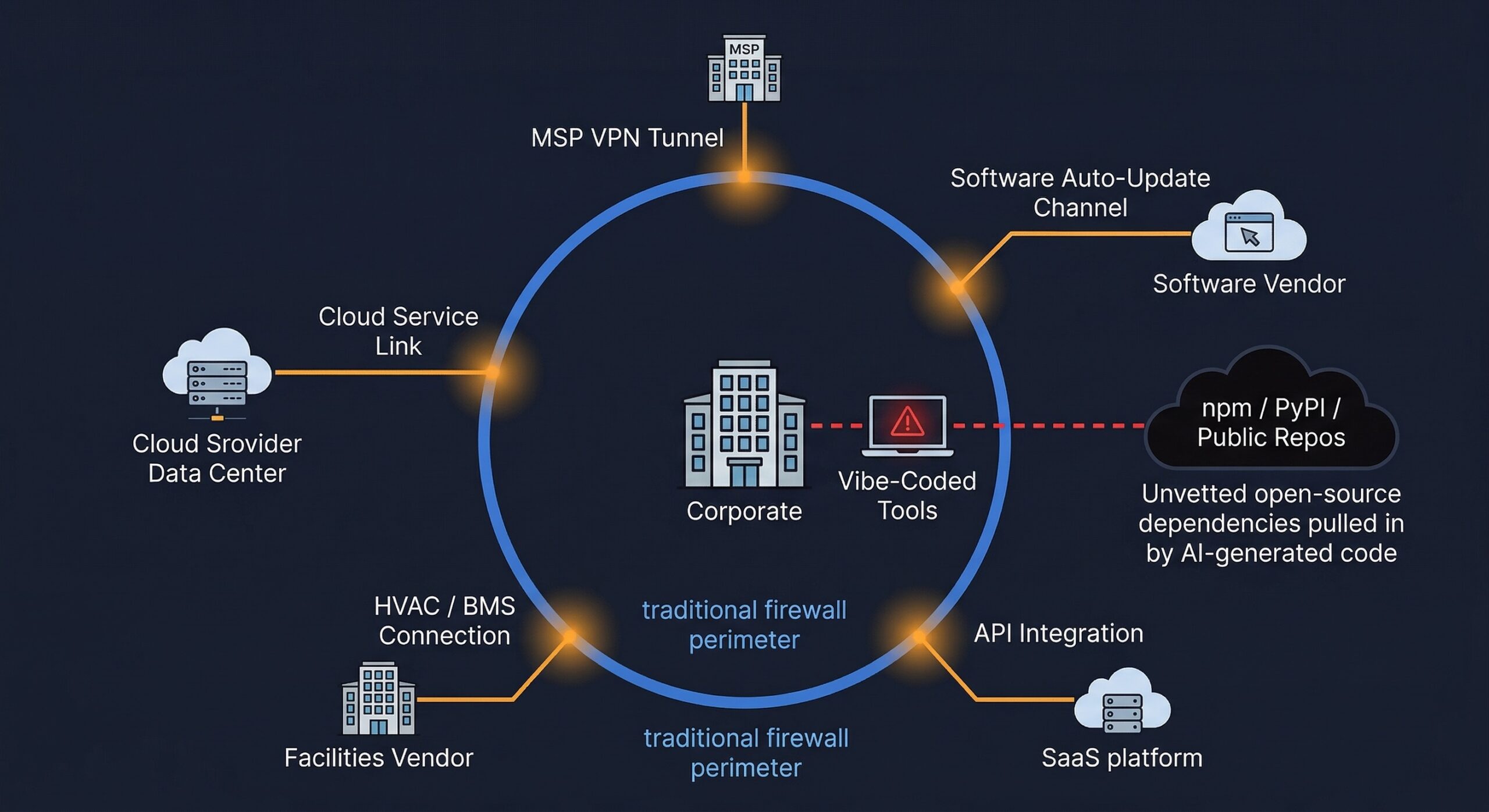
Your security perimeter doesn’t end at your firewall. It extends to every vendor with access to your environment, every software that auto-updates, every API integration.
Testing your own defenses while ignoring vendor risk is like locking your front door while leaving the garage open.
We help organizations understand and address vendor risk through:
- Critical vendor penetration testing
- Vendor access assessment
- Supply chain attack simulation
- Vendor security program development
Your attackers are already thinking about your vendors. Are you?
If your scan reports keep growing but your remediation rate has not changed, the gap is already there. BladeIntel publishes threat intelligence and security research to help businesses understand the risks they face. For more analysis like this, follow us at bladeintel.com or subscribe to our threat briefings.
