A newmalware campaignhas been uncovered by the security researchers at Malwarebytes Labs, which steals sensitive and personal information fromunsuspecting Windows users. It has proven to be an effective attack thanks to both how this malicious piece of software has been designed and the use of a legitimate looking but fraudulent clone of a Microsoft website.
Potential victims are steered towards a typo squatted web address that at a quick glance looks legit. They are greeted with a web page that supposedly hosts the Windows 11 24H2 update and at first glance it appears to be an official Microsoft site.
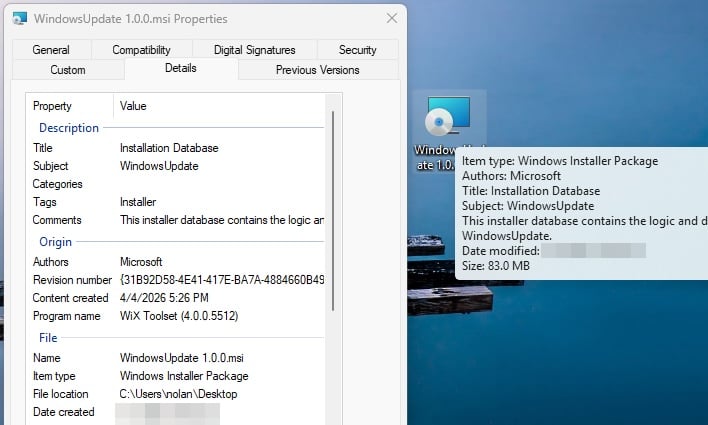
After clicking on the “download the update” button victims get a file titled WindowsUpdate 1.0.0.msi, built with what Malwarebytes says is a” legitimate open-source installer framework.” Attackers use a combination of Electron, JavaScript and Python at various levels within the installation process, which leads to a piece of malware getting installed that was difficult to analyze and detect. For example, “VirusTotal showed zero detections across 69 engines for the main executable,” while it was seen as “low risk” by behavioral scoring mechanisms.
It’s not the just the obfuscated installation process that makes this malware so potent. It also deploys two separate techniques for acquiring persistence on a victim’s machine. The first one modifies the Windows registry to add its own value called SecurityHealth, which is similar to Windows Security Health found in Defender. A second places a shortcut named Spotify.lnk in the startup folder to masquerade as the Spotify music app.
For now, this campaign has mostly targeted French speaking users but will likely be picked up quickly by attackers from other parts of the world. It’s recommended that Windows users only apply updates directly from Windows Update, within the operating system’s Settings menu, to avoid falling victim to these kinds of attacks.
