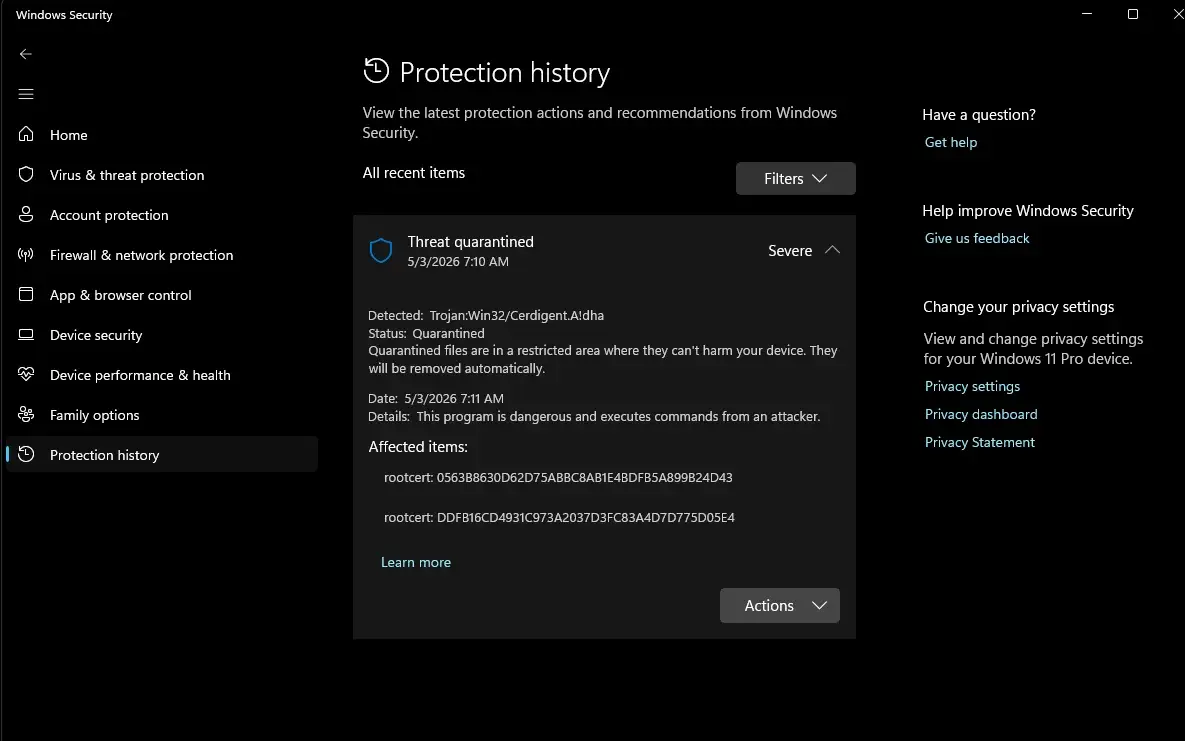
A wave of recent alerts from Microsoft Defender identifying a threat labeled “Cerdigent” on Windows systems is drawing the attention of users and security researchers worldwide, with early evidence suggesting the detections may be tied to the abuse of mis-issued digital certificates rather than a real malware campaign.
According to a report filed in Mozilla’s Bugzilla tracking system, the root of the issue lies in a security incident involving certificate authority DigiCert. The report suggests that a threat actor gained limited access to DigiCert’s internal support systems after compromising a support analyst’s machine. This access allowed the attacker to get initialisation codes for “a limited number of code signing certificates.”
These codes, when combined with approved orders, were sufficient to generate legitimate code-signing certificates that were used to sign software so that they appear trustworthy to operating systems like Windows and anti-virus products like Defender.
DigiCert investigated and found and revoked 60 certificates as they were being used by the Zhong stealer malware. In its full incident report on Bugzilla DigiCert explained: “During our investigation between 2026-04-14 and 2026-04-17, as DigiCert identified certificates potentially affected by the threat actor’s actions, we revoked them. DigiCert revoked 60 certificates issued from the following CAs:
- DigiCert Trusted G4 Code Signing RSA4096 SHA256 2021 CA1
- DigiCert Trusted G4 Code Signing RSA4096 SHA384 2021 CA1
- GoGetSSL G4 CS RSA4096 SHA256 2022 CA-1
- Verokey High Assurance Secure Code EV
27 of the revoked certificates were explicitly linked to the threat actor (11 were identified in certificate problem reports provided to DigiCert by community members linking the certificates to malware, and 16 were identified during our own investigation). … In addition to the 27 identified above, 33 of the 60 total certificates were revoked during our own investigation as a precautionary measure. … The exploited certificates identified by the community member were found to have been used to sign the “Zhong Stealer” malware family.”
Thus for now, available information suggests that many Cerdigent alerts may not indicate active infection but a false alarm. Microsoft’s own threat database does not say much about it except that “Cerdigent.A!dha can perform a number of actions of a malicious actor’s choice on your device.”
Since code-signing certificates play a key role in the trust model of modern operating systems, when compromised, they can blur the line between legit and malicious software. If you are encountering such warnings then you are advised to monitor updates from security vendors, as signature corrections are often issued quickly in cases of widespread false positives, which seems to be case here too.
Source: Bugzilla@Mozilla
Thanks for the tip, Aryeh Goretsky!!!