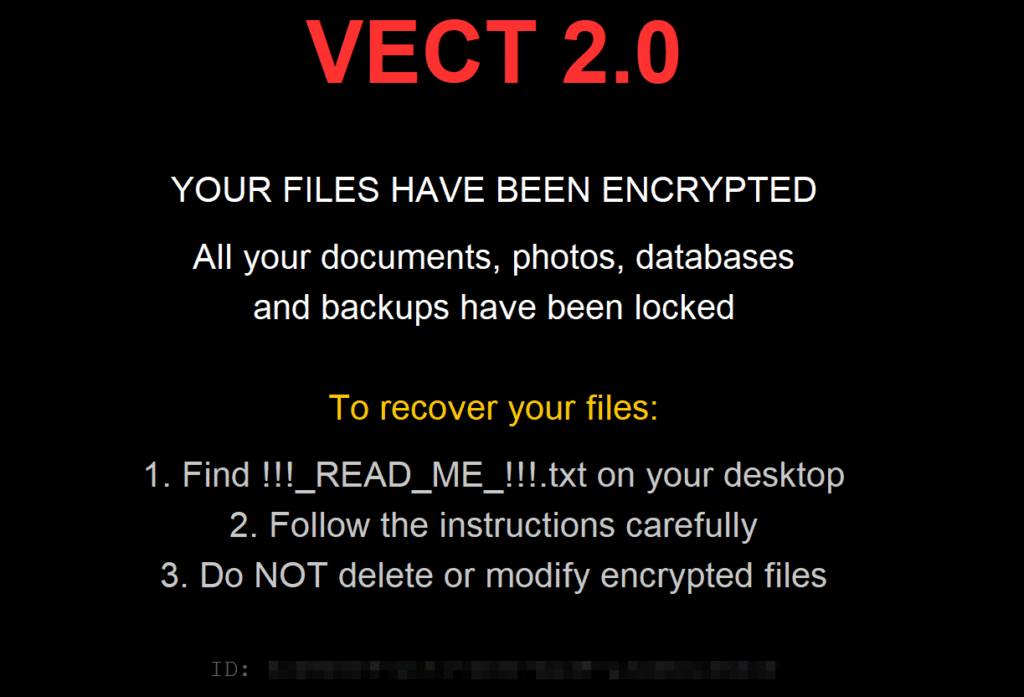
A major coding error in the VECT 2.0 ransomware is permanently destroying victim data, leaving no way for files to be recovered even if the ransom is paid. New findings from Check Point Research (CPR) and Halcyon reveal that while the hackers behind the project tried to build a professional-looking tool, their basic mistakes have turned this ransomware into a wiper that simply ruins data.
“Vect is a Ransomware-as-a-Service (RaaS) operation whose encryption implementation for Windows, Linux, and ESXI variants contains critical flaws that may render decryption and ransom payment ineffective for data recovery,” Halcyon researchers explained.
VECT 2.0 was first detected in December 2025. It quickly expanded its capabilities by February 2026 to target Windows, Linux, and ESXi systems. Normally, ransomware locks a file and saves a digital key so the victim can unlock it later, after paying the ransom; however, Check Point Research found a huge problem in how the software handles large files.
Any file bigger than 128 KB, which covers almost all office documents, databases, and backups, is broken during the attack. The malware creates four separate keys to lock the file, but accidentally overwrites and deletes the first three.
Since those keys vanish forever the moment they are used, the researchers noted that “full recovery is impossible for anyone, including the attacker.” Even the hackers do not have the keys needed to help their victims.
The group has done its best to make its campaign look high-end, but its malware is full of rookie errors. Analysis by Halcyon also found that the Full mode is defective because of a memory error that restricts encryption to files smaller than 32 KB, causing it to skip most data entirely.
Other errors discovered by researchers include ignored modes where settings for fast, medium, or secure modes are parsed by the code but then silently ignored. Also, the malware tries to start hundreds of tasks at once. This thread scheduler error overwhelms the computer and slows it down instead of speeding up the attack.
The hackers tried to hide their instructions using a method called XOR string obfuscation, but they’ve messed up the math so badly that the code cancels itself out. This leaves their plans in plain text for anyone to read.
Furthermore, the Windows version of the attack specifically targets files by adding a .vect extension and forces programs like Excel.exe, Winword.exe, and Outlook.exe to close so it can grab their data.
Despite these technical failures, the group has claimed several victims through a partnership with another group called TeamPCP. In March 2026, they launched attacks that hid malware inside popular developer tools like Trivy, Checkmarx KICS, LiteLLM, and Telnyx. The group has even invited members of BreachForums, giving out access keys to any member who wanted to join their network.
Although the hackers claim their system is sophisticated, in reality, they are just using a broken engine. Researchers warn that the information needed to unlock the files is destroyed during the attack; therefore, paying the hackers will not bring your data back.
“VECT 2.0 presents an ambitious threat profile with multi-platform coverage, an active affiliate program, supply-chain distribution via the TeamPCP partnership, and a polished operator panel. In practice, the technical implementation falls significantly short of its presentation,” CPR blog post concludes.