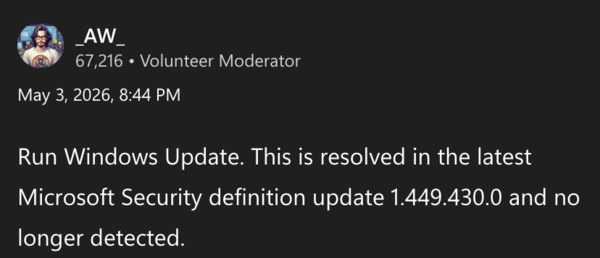
Update 03/05/26 – 11:16 pm (IST): Microsoft might have quietly addressed the false positive issue. A follow-up update, either version 1.449.430.0 or 1.449.431.0, reportedly no longer triggers the detection issue. Comments on Reddit also confirm the same.
After updating, affected certificates were restored from quarantine, and systems re-added them to the trusted root store without issues. Microsoft has seemingly restored the certificates via background processes visible in Microsoft Defender. While no public statement was issued, the problem appears to be fixed for now.
Original article published on May 3, 2026, follows:
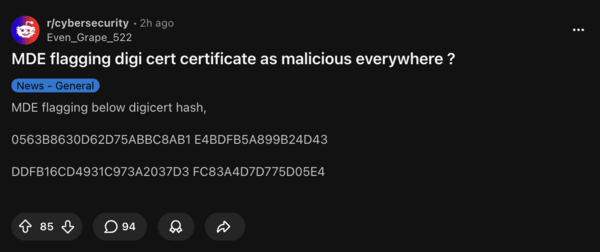
Microsoft Defender is mistakenly flagging two trusted DigiCert root certificates as malware, and this false positive began around May 3, 2026.
It began after users received a security intelligence update (version 1.449.424.0), and it targets two specific DigiCert root CA files present on nearly all Windows systems. The files are:
- DigiCert Assured ID Root CA, and
- DigiCert Trusted Root G4
Microsoft Defender quarantines these files, triggering a flood of high-severity incidents. A post on Reddit in r/cybersecurity explains the problem, going into further detail about the partial certificate hashes. Another post claims that “high-severity” malware was detected.
Microsoft Defender uses signature-based detection, and in this update, Microsoft apparently added a detection for “Cerdigent,” aimed at malicious activity. However, the update incorrectly seems to have matched the cryptographic hashes of these two long-trusted public root certificates.
Root CAs such as this validate countless websites and secure connections, and it can cause problems when quarantined.
In simpler terms, an antivirus seems to have decided that an essential part of the system is a threat and has quarantined it to prevent damage. DigiCert Root CAs have been trusted for years, and a buggy update caused Microsoft Defender to treat them as malware. It’s not an actual infection, and no malware code is spreading. It’s an error on Microsoft’s end.
The cybersecurity community reports seeing identical errors, and a lot of people initially panicked. Later on, it was decided to be a false positive.
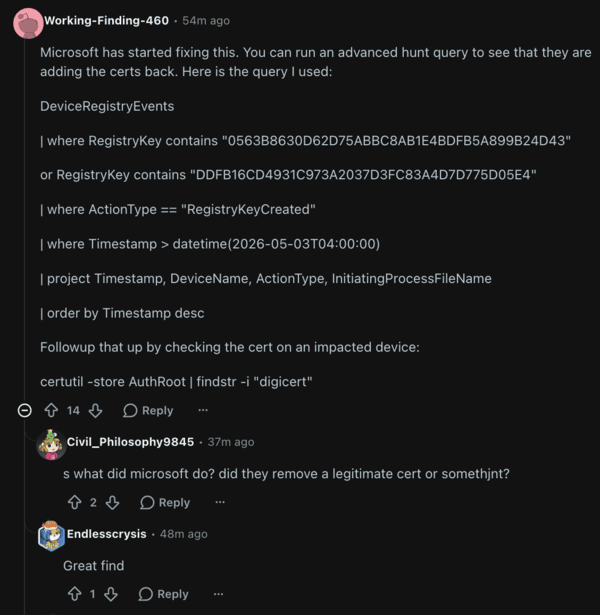
While Microsoft didn’t issue a statement on this, some replies on Reddit claim that the company has started fixing this. Running the advanced query mentioned in the reply allegedly shows that Microsoft is adding the certificates back. As Microsoft rolls out the update, these certificates should probably be back in place.
A temporary fix is to add exclusions for these two certificate files via Defender Settings. You may need to restore quarantined items if required.
You can keep track of the updates in Microsoft’s security intelligence changelog. While the false positive is annoying, it’s good that Microsoft has likely begun working on a fix.
We stand out from the tech-media crowd because we break news stories; we mainly bring you stuff that you won’t find anywhere in the mainstream tech media. Our stories have been picked up by some of the world’s most popular websites and media outlets—more info is available here.